Post-Quantum Cryptography for Federal Systems
NIST's post-quantum cryptography standards are final. What federal agencies and defense contractors need to understand about cryptographi...
Practical engineering perspectives on cloud, security, and aerospace systems. Written from production experience, not theory.
NIST's post-quantum cryptography standards are final. What federal agencies and defense contractors need to understand about cryptographi...

Identity governance and administration (IGA) for federal cloud programs — covering identity lifecycle, privileged access management, and ...

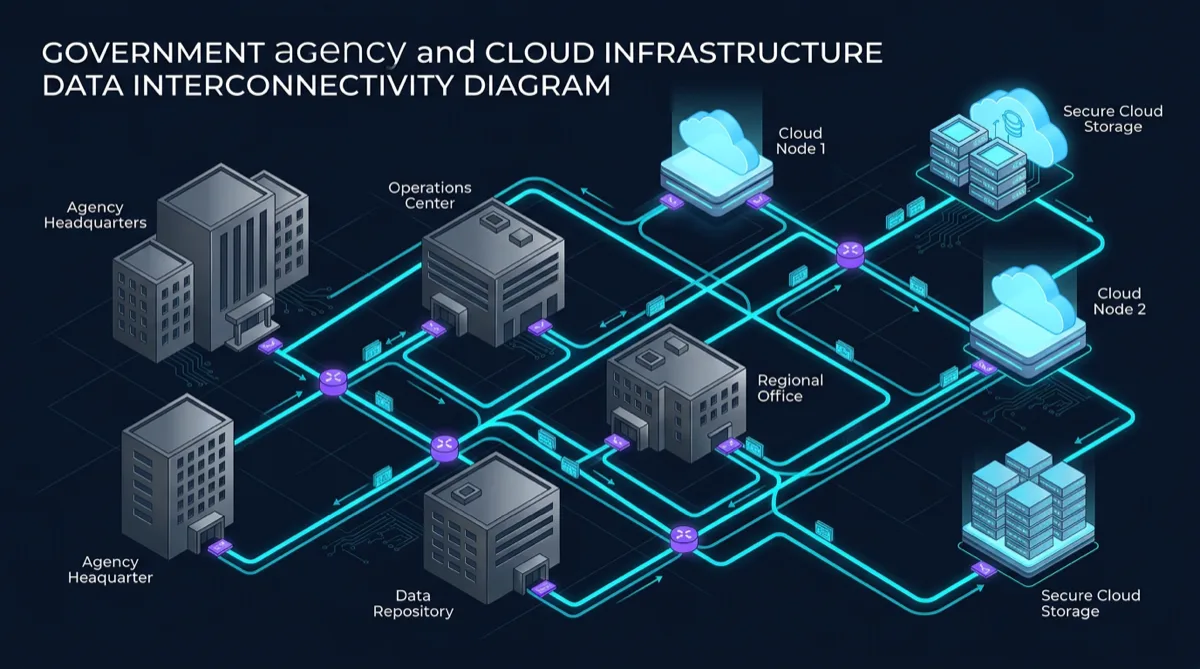
How AWS Control Tower structures multi-account government cloud environments — landing zones, guardrails, account vending, and FedRAMP al...
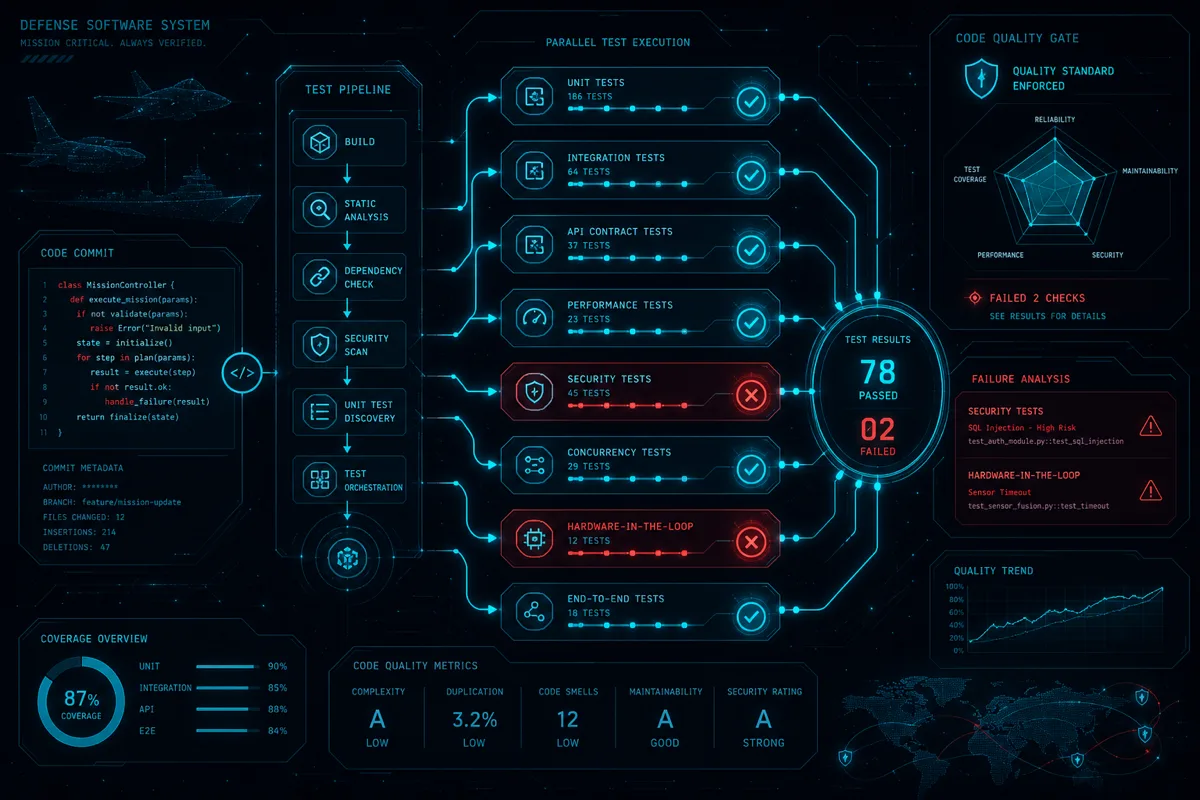
How defense software programs implement meaningful test automation — shift-left testing, DoD software testing policy, automated security ...

Building mobile apps for government? Understand NIST mobile security guidelines, DoD mobility framework, MAM vs. MDM approaches, and what...

Comparing GitLab and GitHub for government DevSecOps environments — FedRAMP status, self-hosted vs. SaaS deployment, pipeline integration...

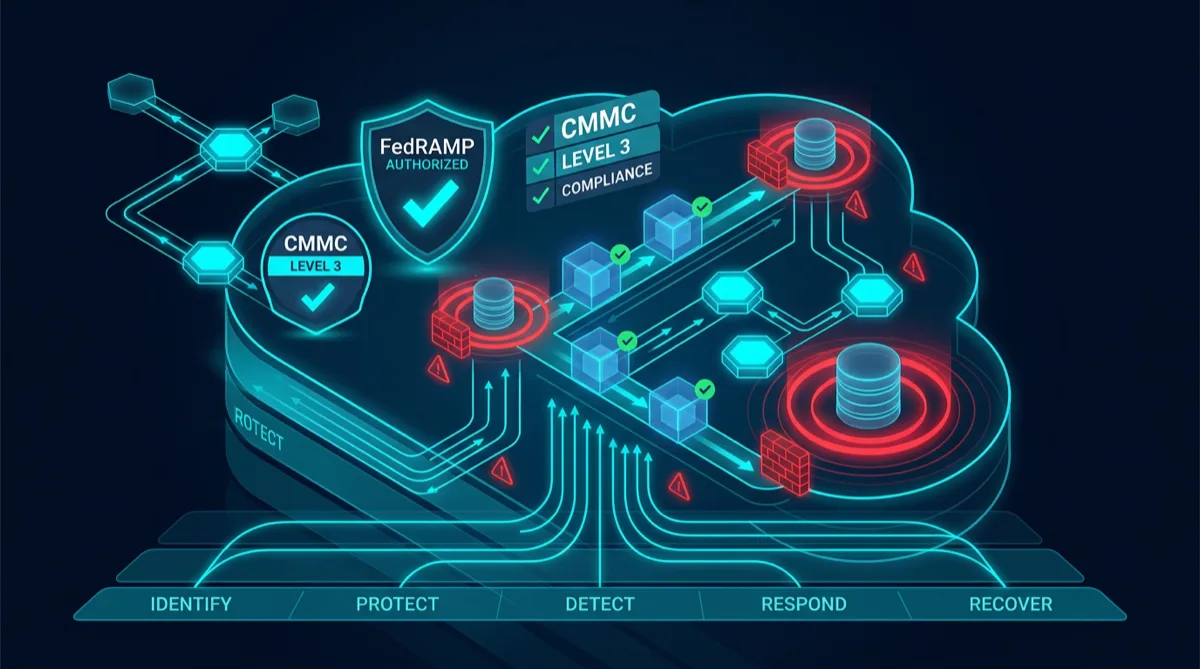
Small businesses pursuing DoD contracts: understand CMMC 2.0 requirements, which level applies to your work, how to achieve compliance, a...

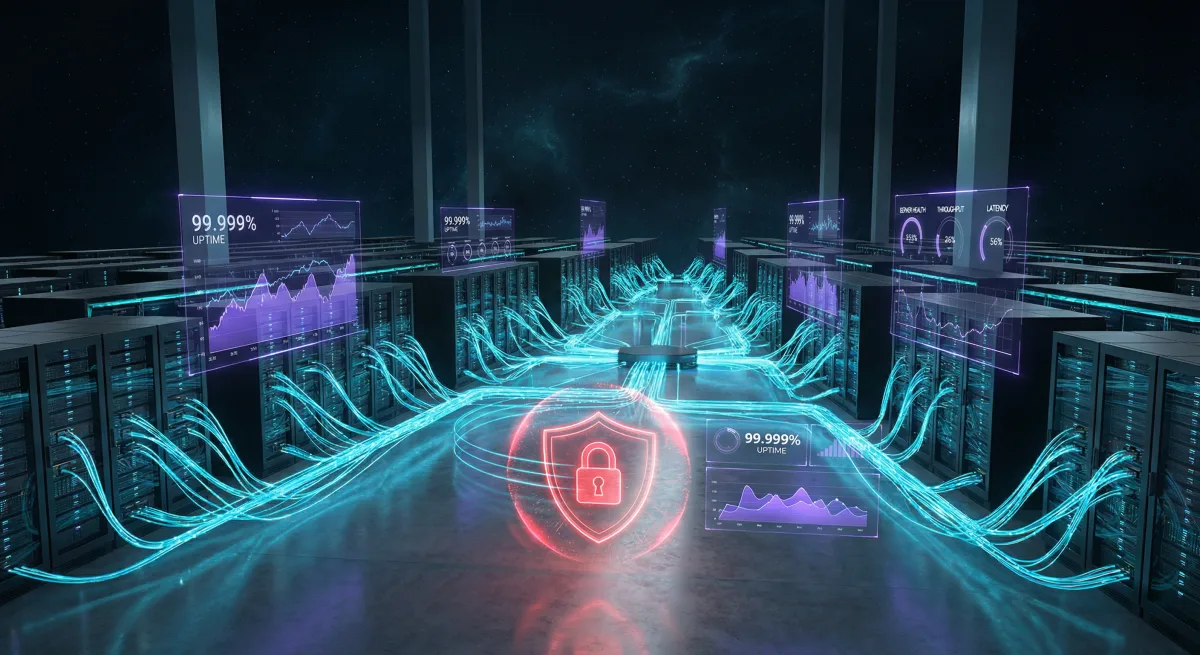
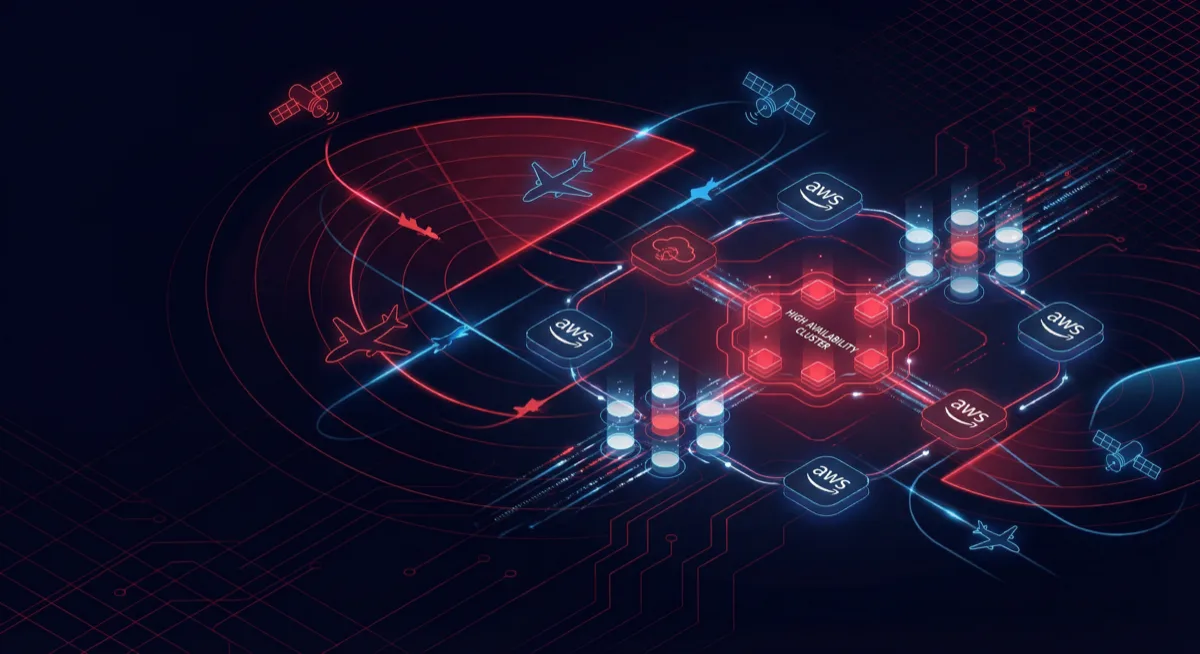
How federal agencies and contractors design disaster recovery for government cloud — RTO/RPO requirements, multi-region architectures, Fe...

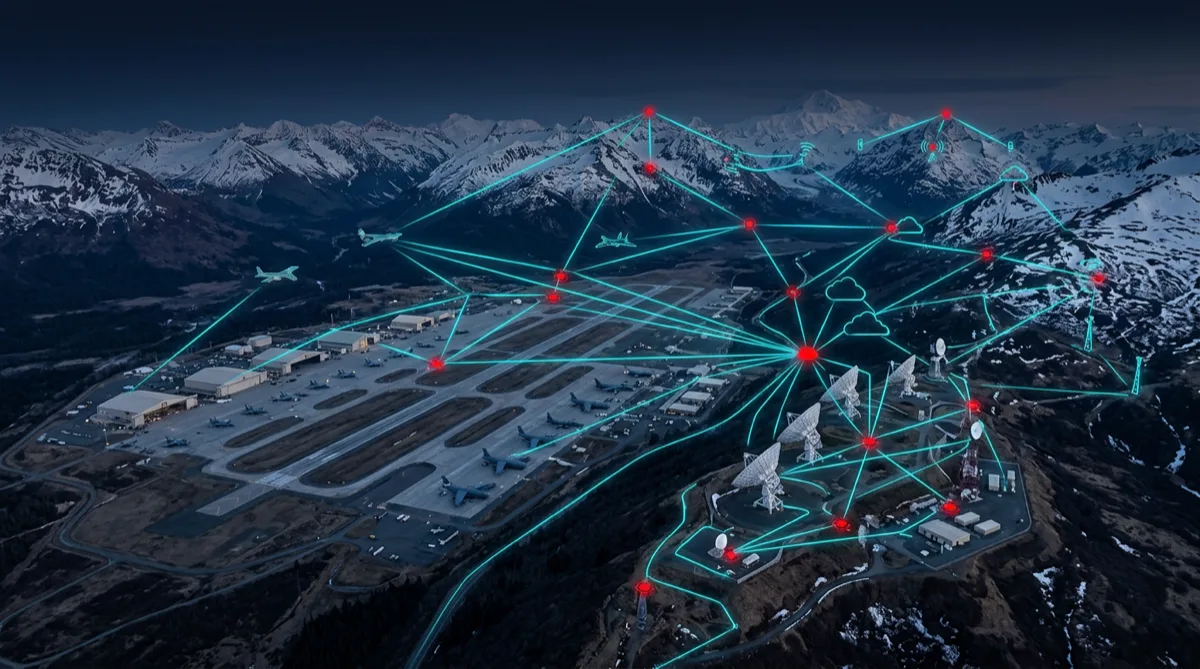
Engineering software systems for Arctic ground station operations — environmental constraints, connectivity requirements, autonomy archit...

What defense and space companies look for in software subcontractors on launch vehicle programs — quality systems, process standards, saf...
How federal agencies deploy Drupal on AWS GovCloud for FedRAMP compliance — architecture patterns, USWDS integration, Section 508, and CD...

How federal programs apply chaos engineering principles to validate cloud resilience, meet FedRAMP contingency testing requirements, and ...

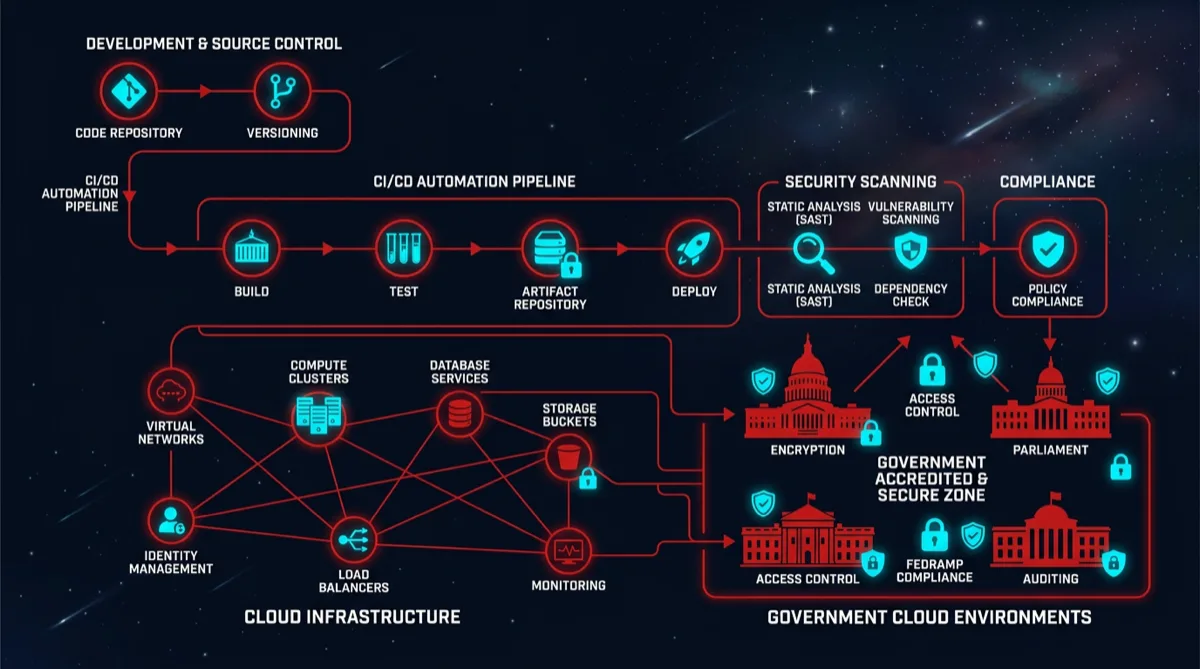
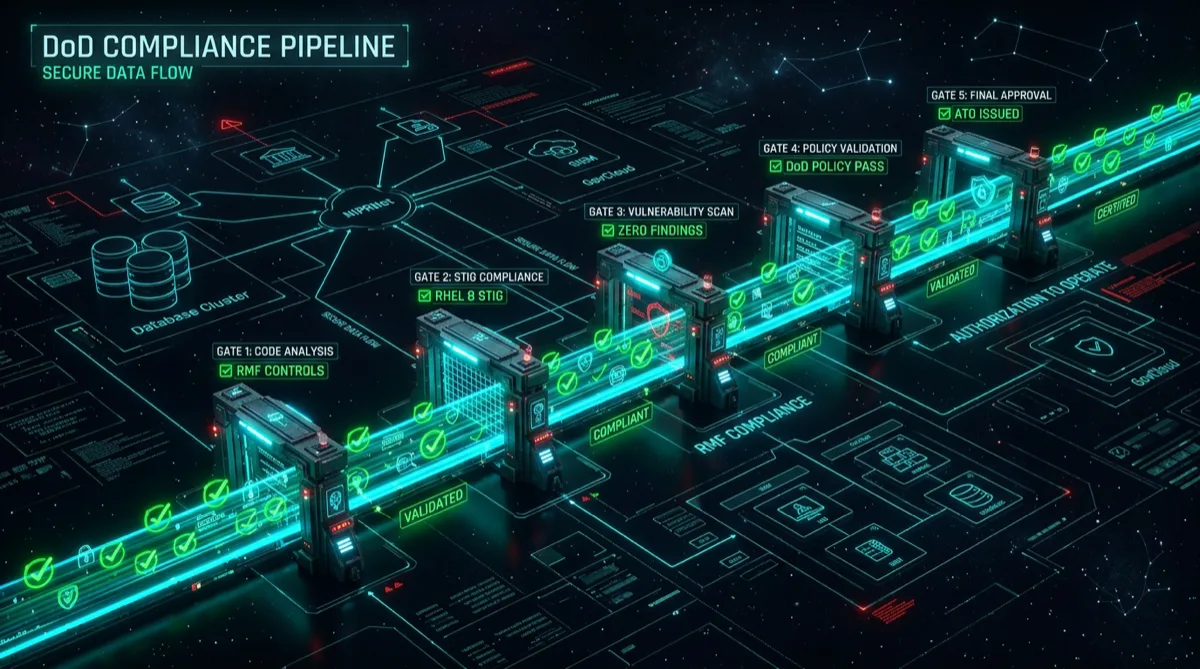
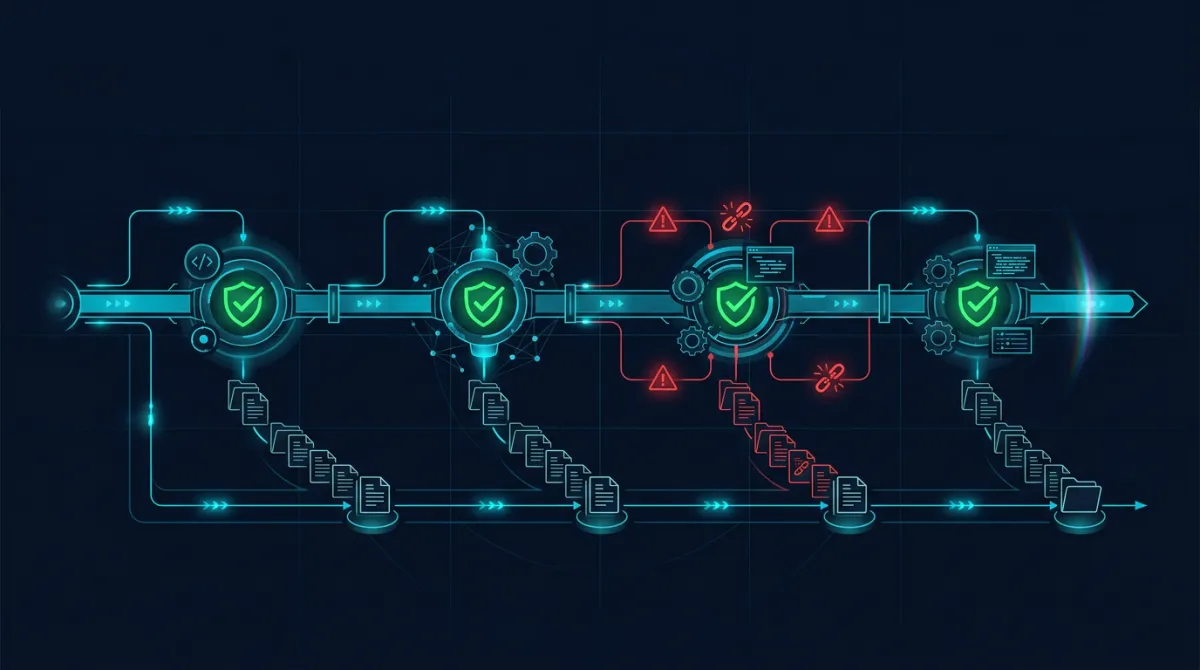
What DoD Software Factory pipeline templates actually contain — security scanning stages, STIG compliance automation, artifact signing, a...
How defense programs test and validate AI/ML models — responsible AI principles, DoD AI assurance framework, adversarial robustness testi...

The intersection of high-performance computing, Arctic science, and government research contracts in Alaska — UAF's research computing in...

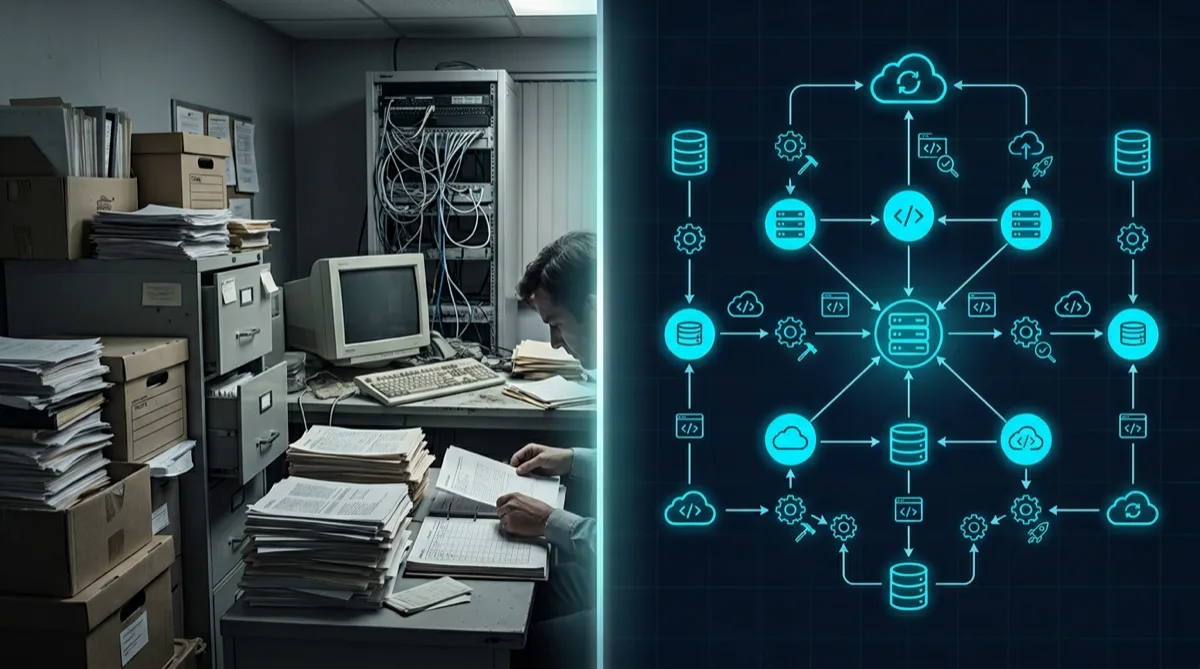
How defense programs migrate legacy applications to cloud using Software Factory infrastructure — assessment frameworks, strangler fig pa...

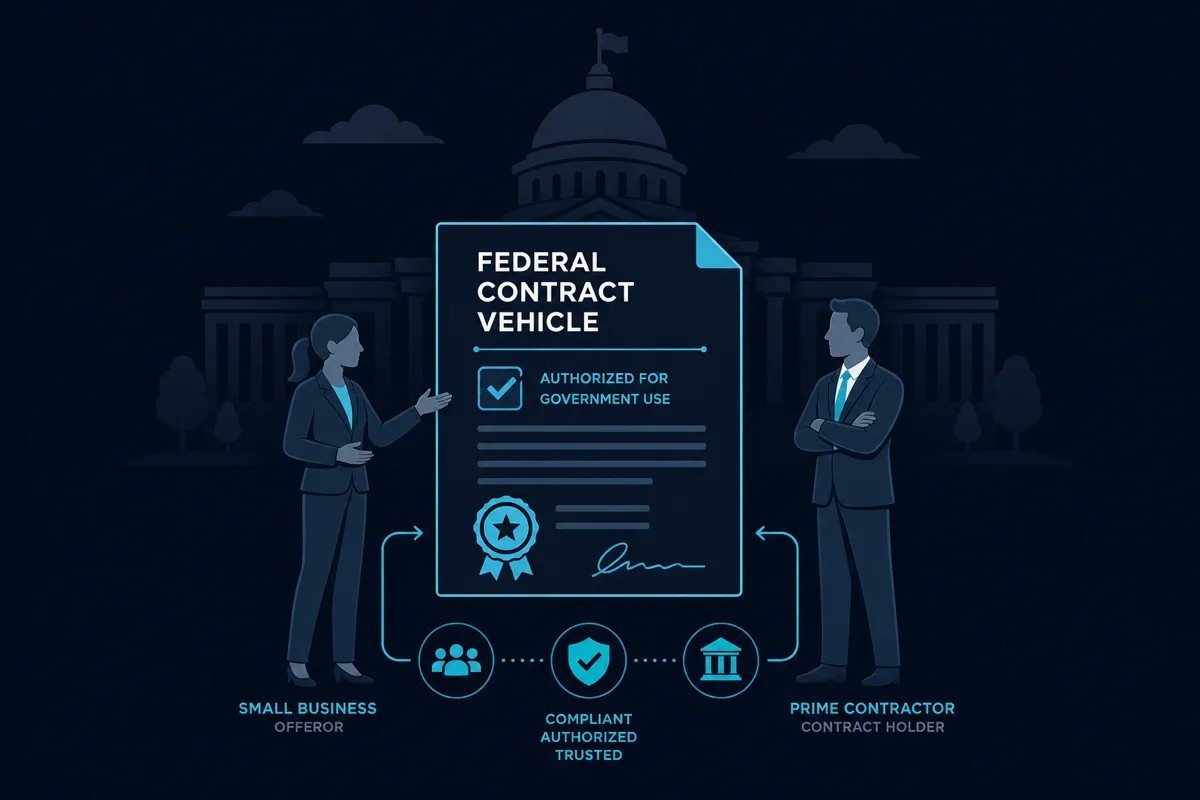
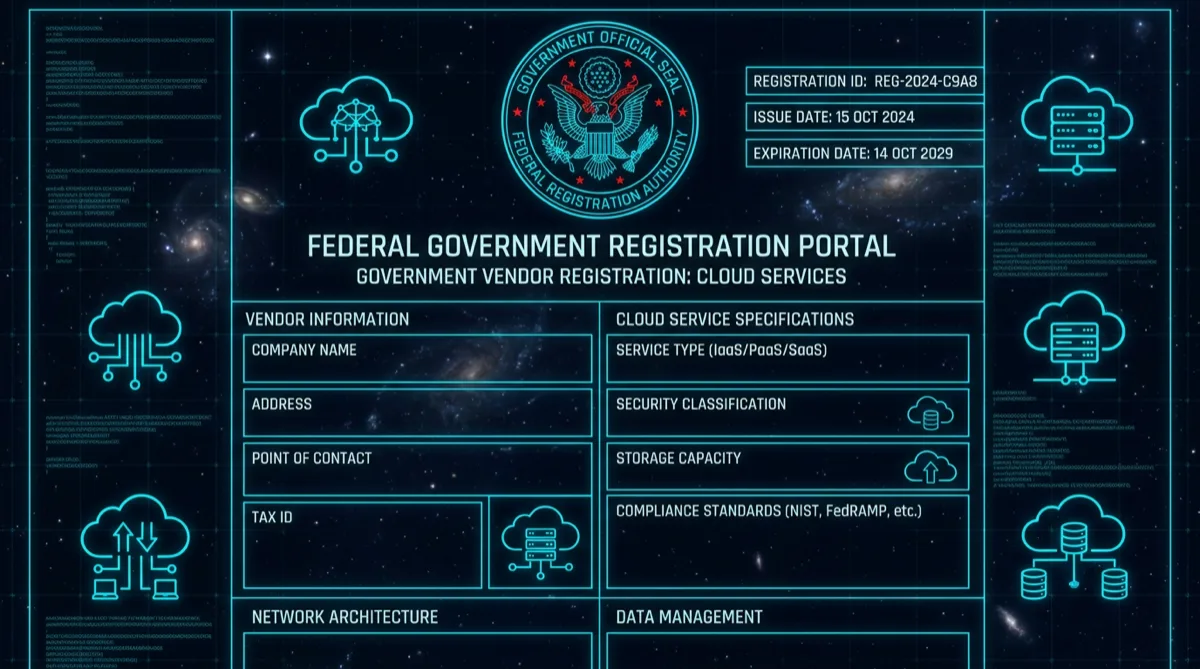
How technology companies get onto GSA IT Schedule 70/IT Schedule and DoD marketplace vehicles as SaaS providers — contract vehicles, FedRAMP

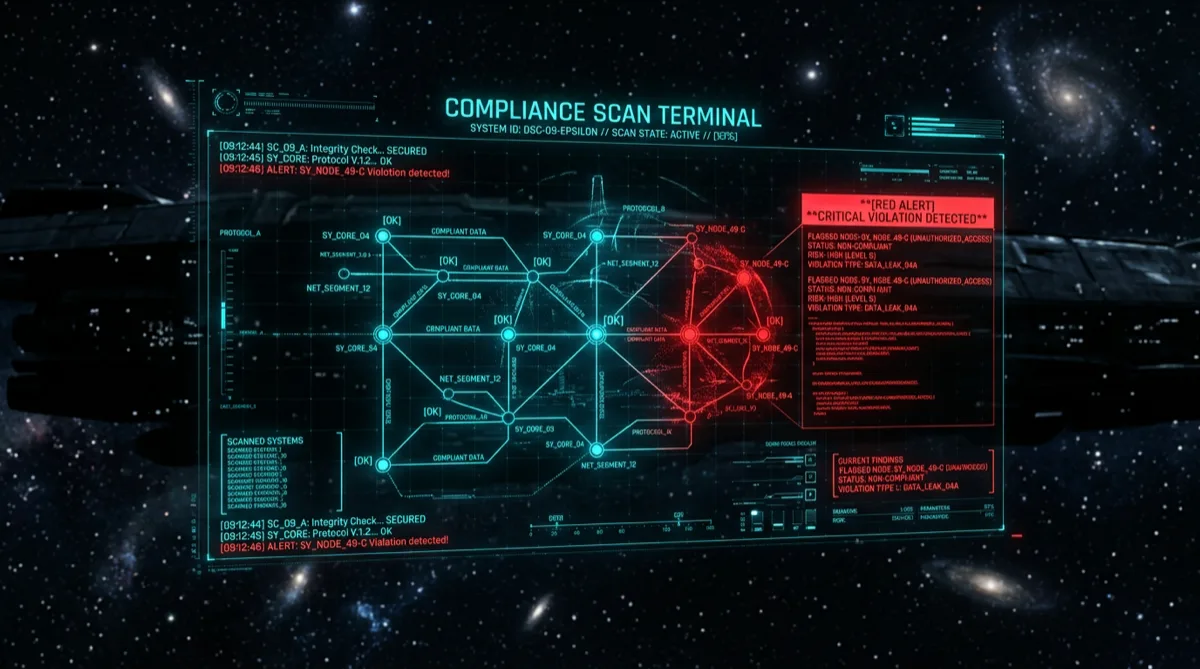
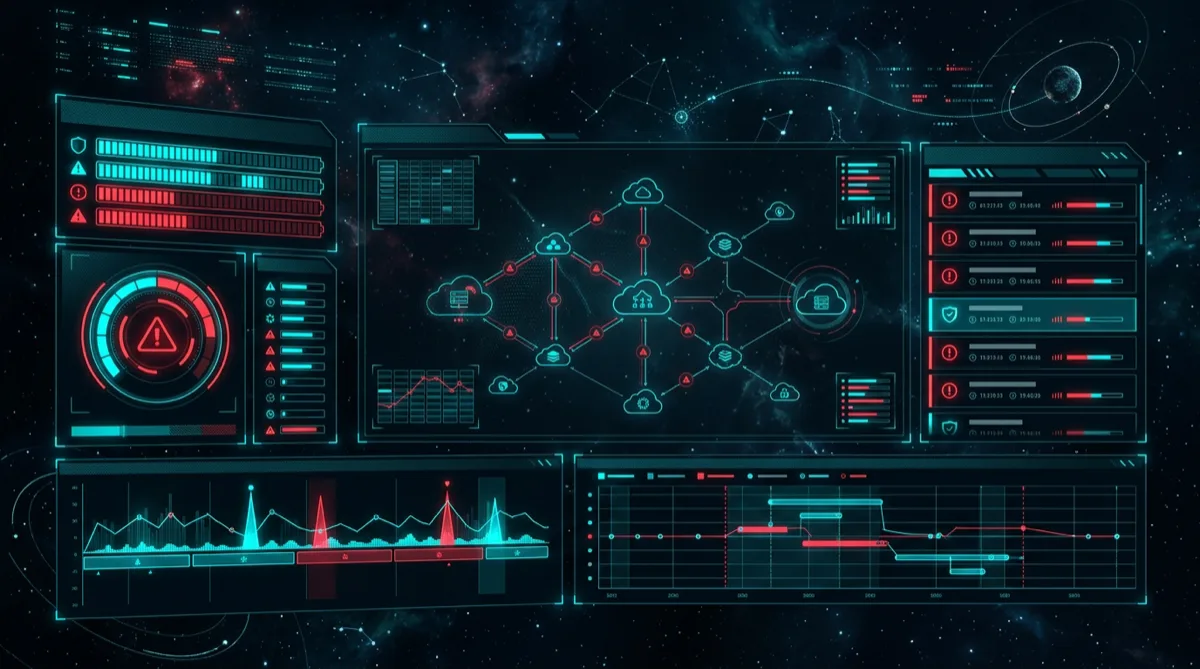
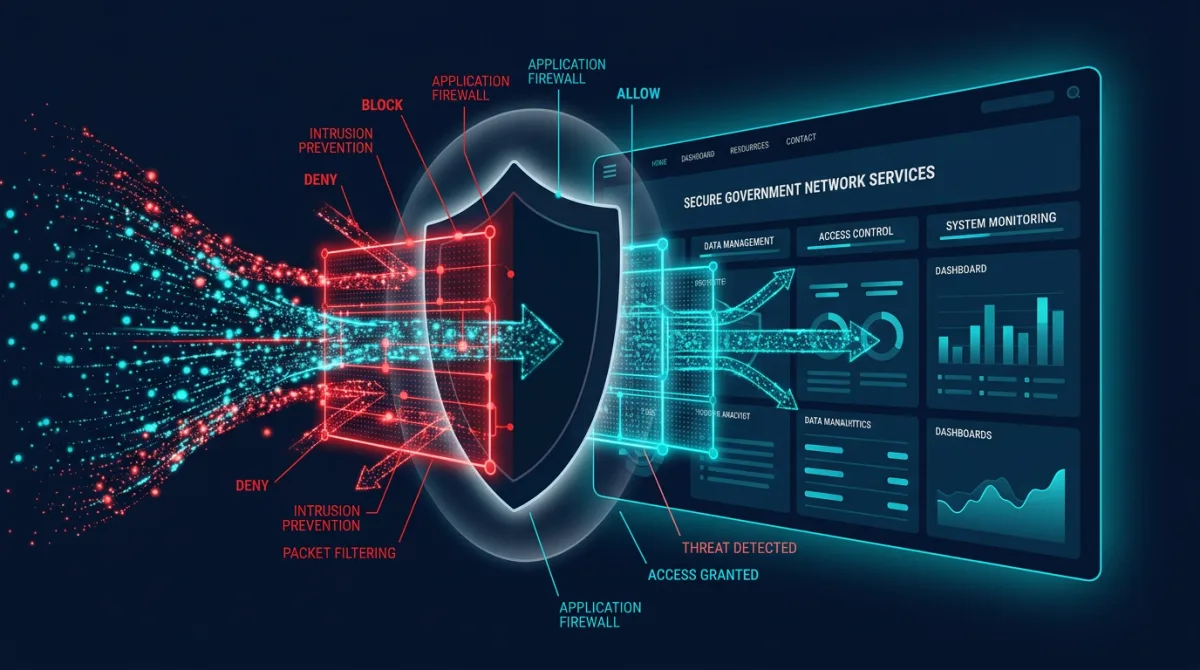
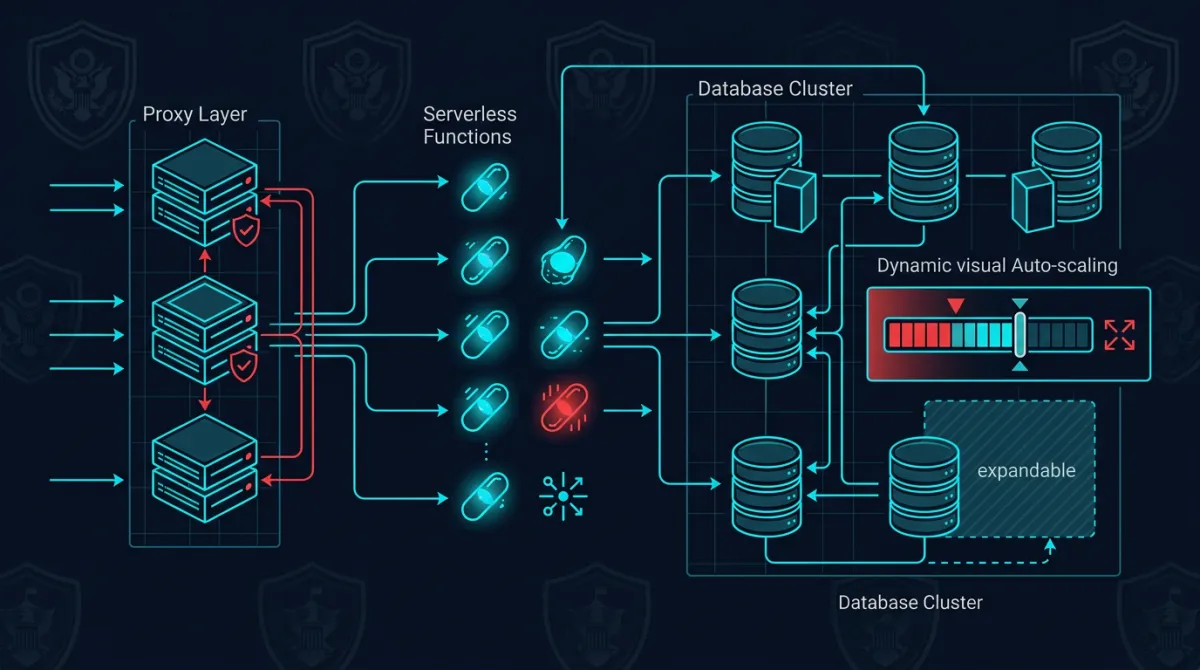
How federal programs build event-driven security monitoring architectures — Security Hub, EventBridge, Lambda automation, SIEM integratio...

How small businesses in Alaska compete for DoD and federal defense contracts — NAICS codes that work, Alaska-specific opportunities, set-...

What to expect when onboarding as a technology subcontractor on a defense cloud program — clearance requirements, DCAA compliance, securi...
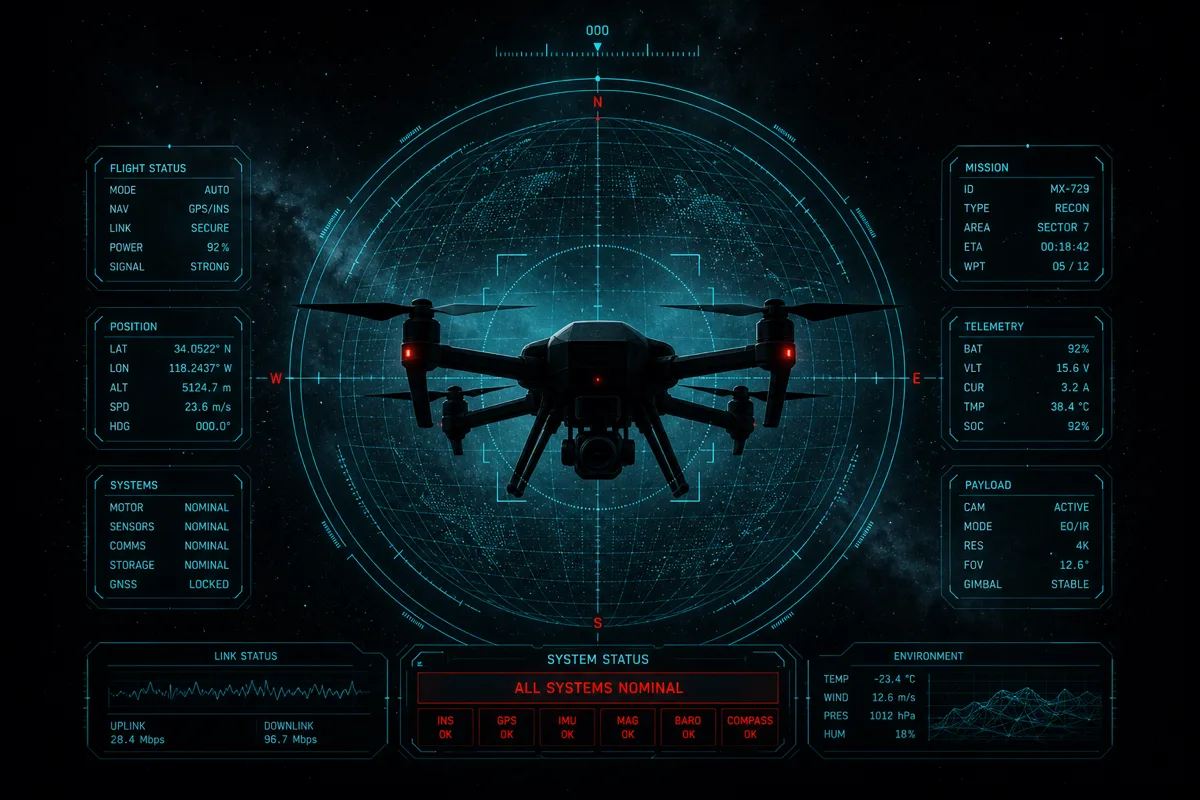
Ground control software for autonomous and unmanned systems demands real-time data pipelines, state machine management, and resilient C2 design.
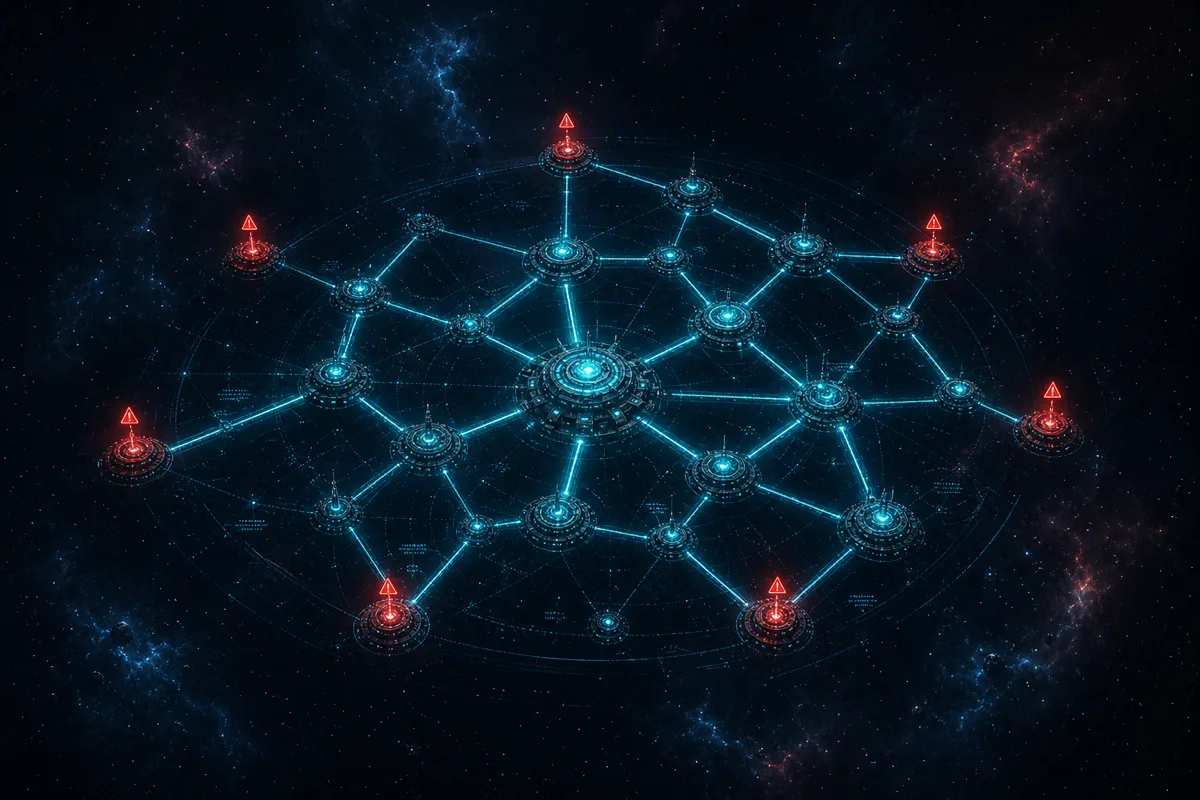
Deploying DevSecOps pipelines across distributed defense environments demands more than a single CI/CD server. Here's how Rutagon architects for.
Primes accessing OASIS+ task orders need cloud engineering subs who can respond fast and deliver against IL requirements. Here's what Rutagon brings to.
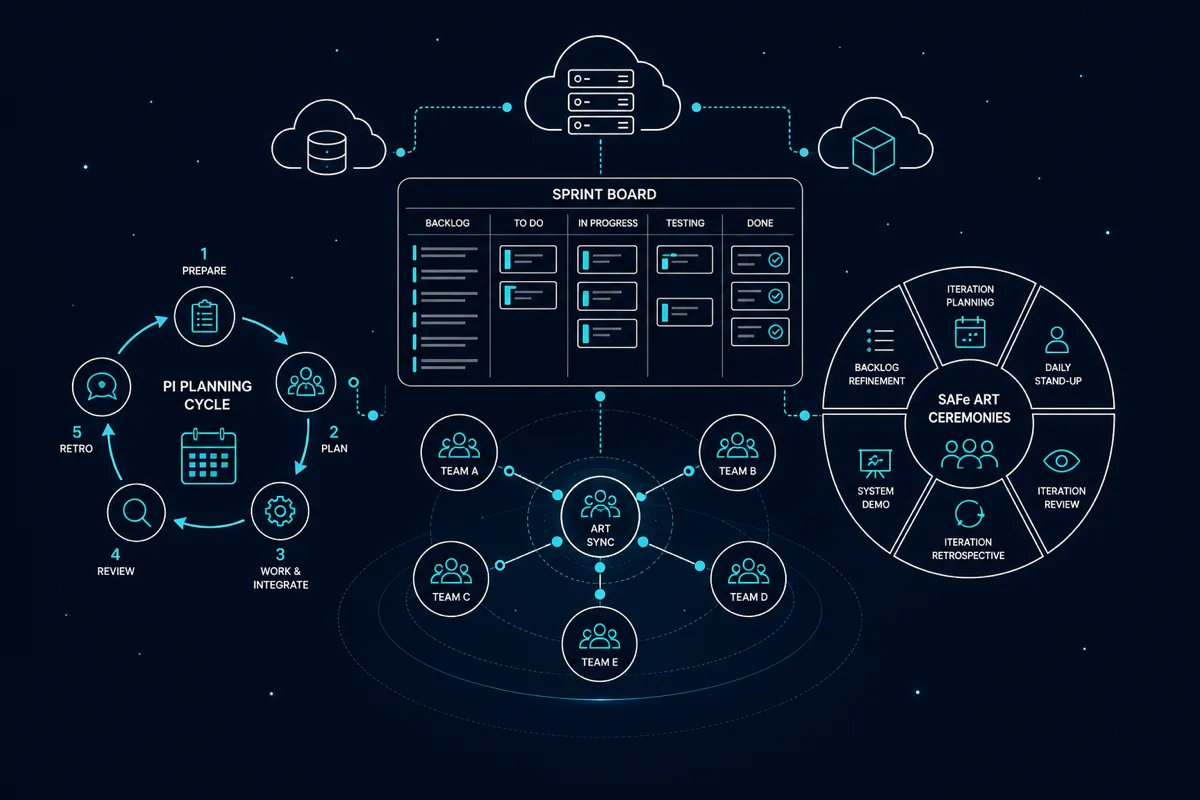
Defense programs using SAFe expect subcontractors to plug into PI planning, sprint reviews, and ART ceremonies. Here's how Rutagon integrates as an.

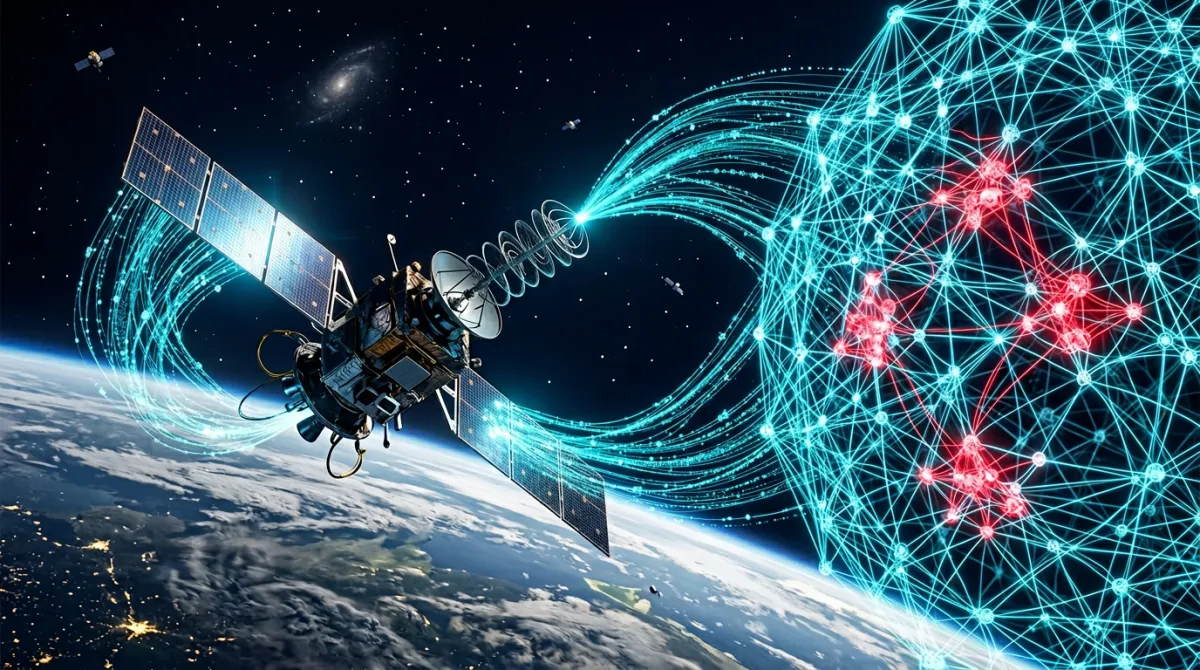
SDA programs require real-time sensor data fusion, cloud-native processing, and resilient ground architectures. How Rutagon approaches space domain.
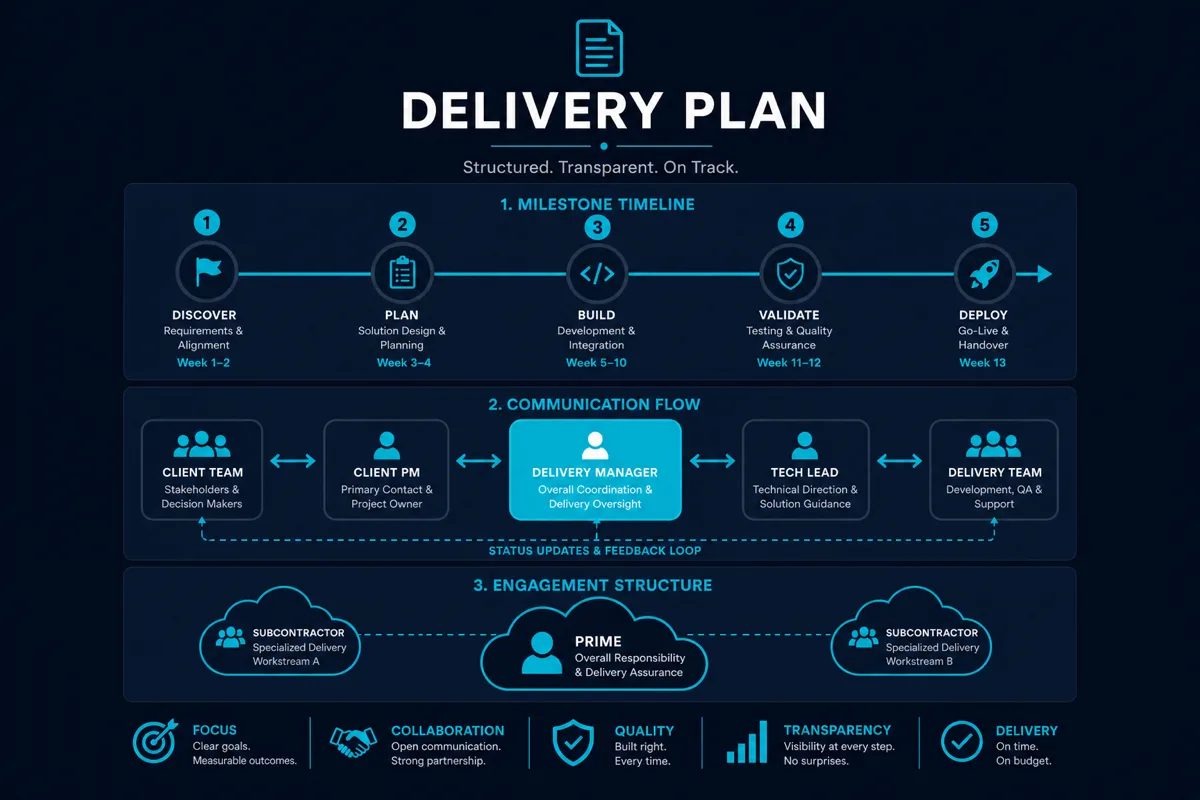
A subcontractor management plan for cloud engineering programs should cover delivery cadence, ATO evidence handoff, clearance requirements, and.

Knowledge transfer at program transition or sub offboarding is a prime contractor risk event. How Rutagon approaches documentation, handoff, and.

Programs using DISA cloud services must implement a specific security stack. Here's how Rutagon implements DISA's security requirements in cloud.
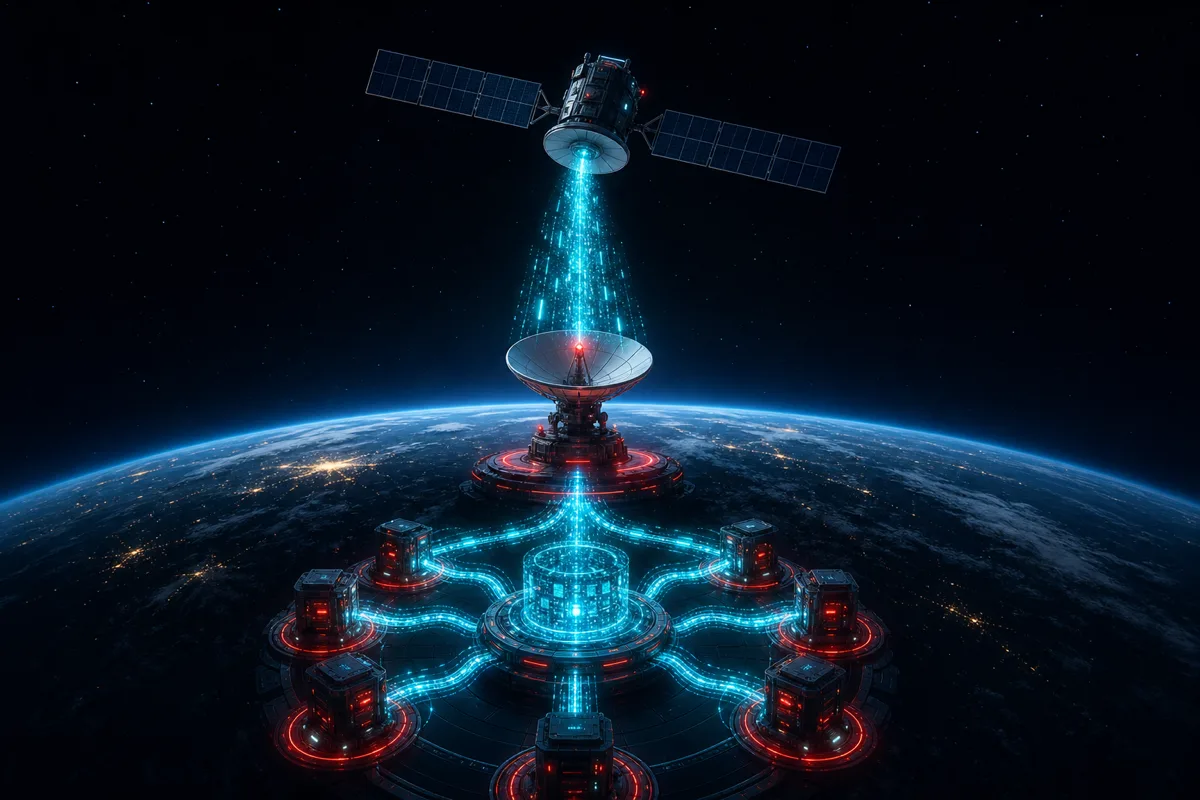
Satellite programs generate terabytes of raw telemetry and mission data per orbit. Cloud-native data pipelines transform raw downlink into actionable.

Rutagon operates on one rule — deliver working software, not slide decks. Here's the engineering and delivery philosophy behind Alaska's defense.
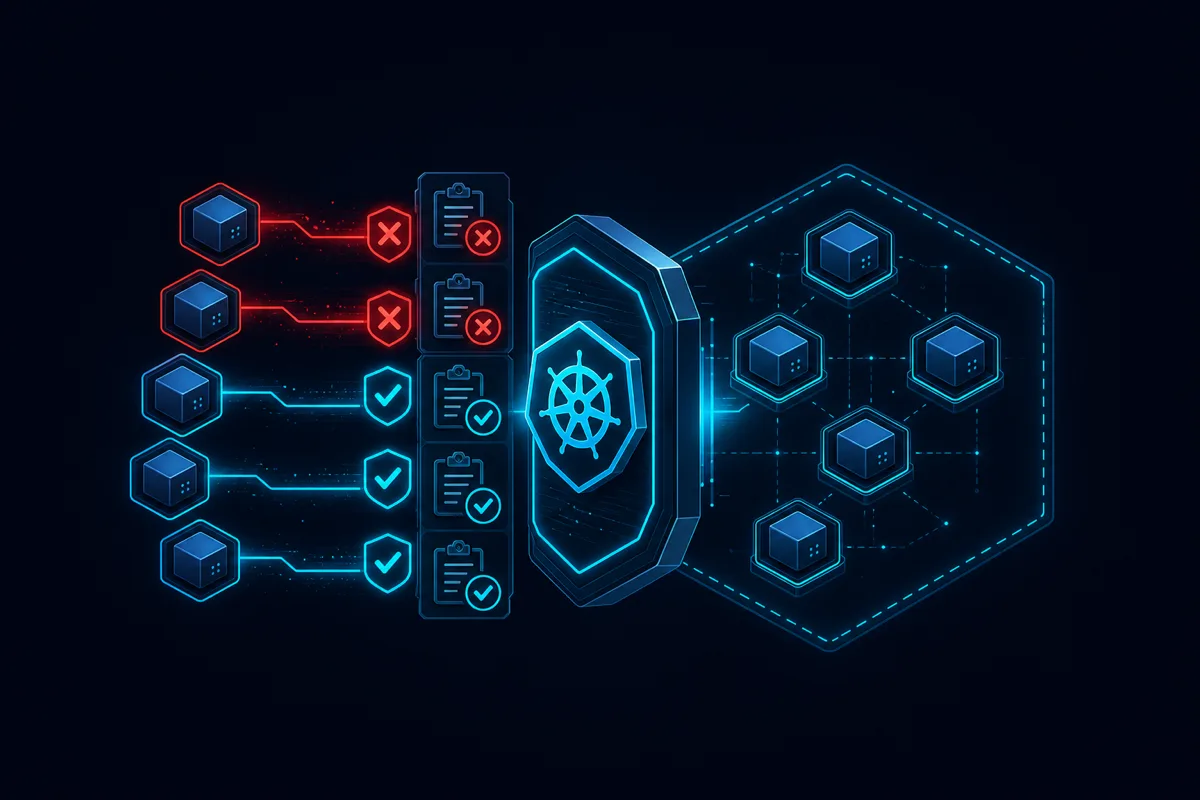
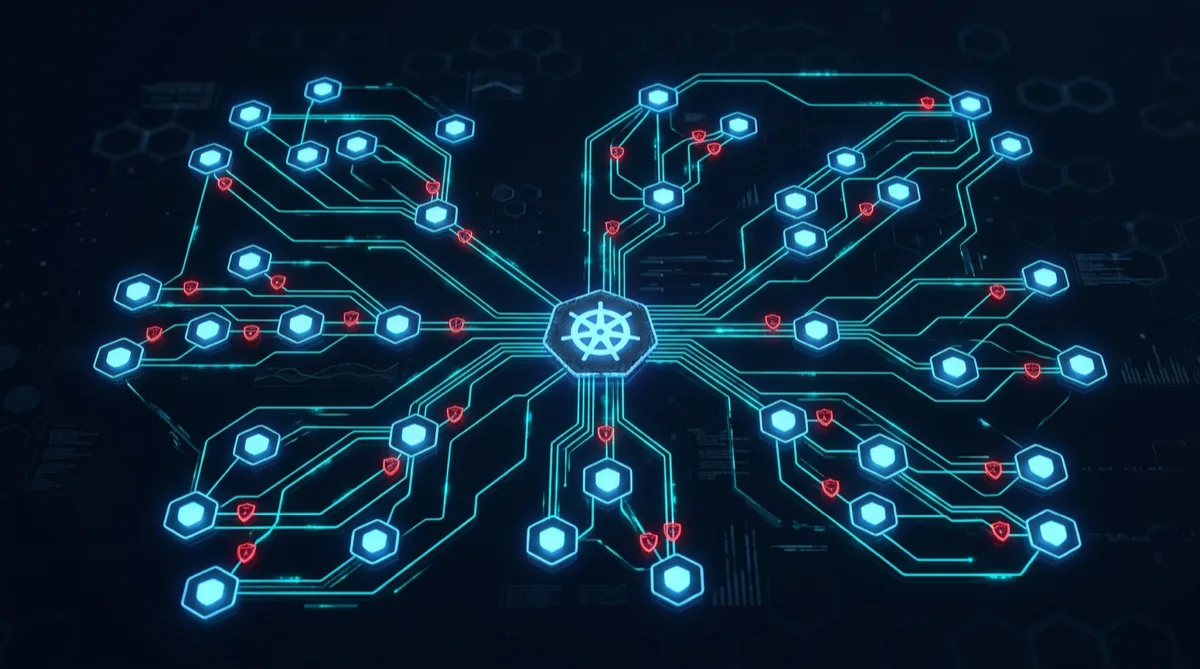
Admission controllers are Kubernetes's last line of defense before a workload runs. How Rutagon uses admission control to enforce security policy at.

Cloud subcontractors on defense programs need structured program management — not just technical delivery. How Rutagon manages delivery, risk, and.
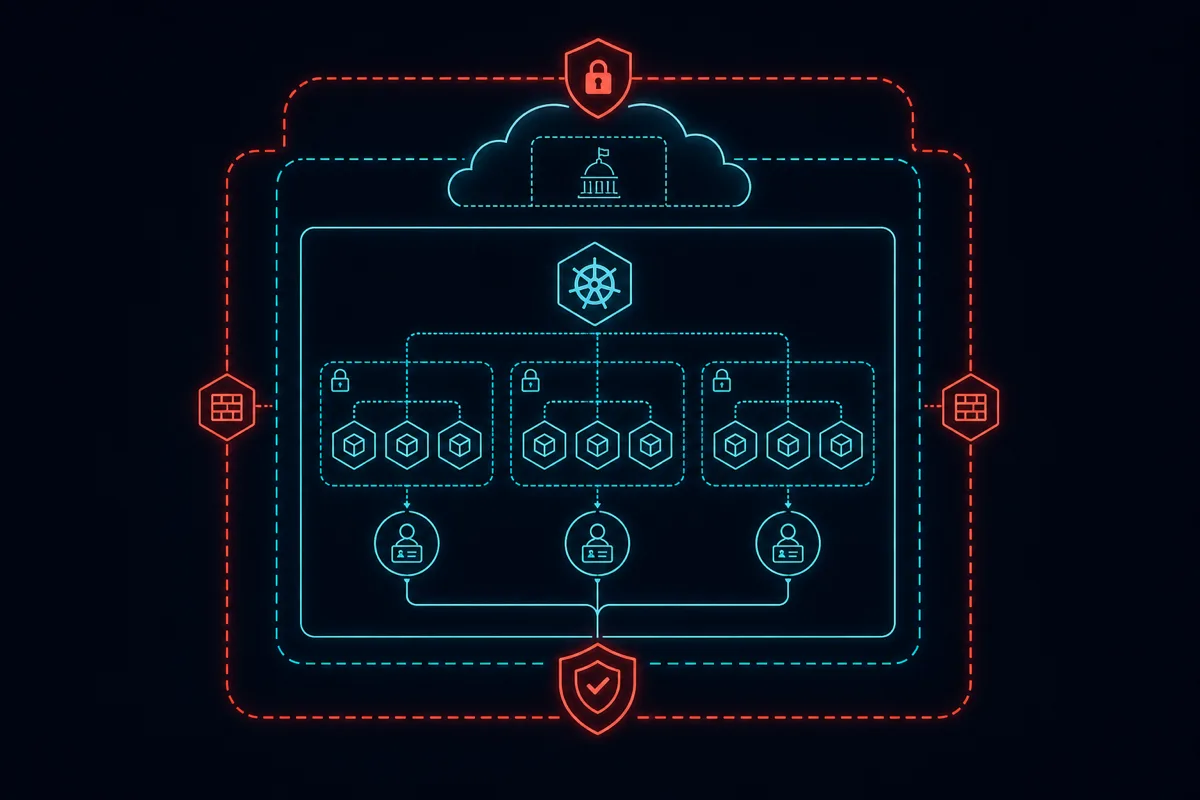
EKS on GovCloud for DoD programs requires specific security configuration — STIG compliance, network isolation, IAM design, and ATO evidence generation.

CMMC scoping for cloud subs determines what assessment scope, security controls, and evidence applies. How Rutagon manages CMMC boundaries on defense.

The Software Acquisition Pathway enables iterative delivery on DoD programs. What primes need from cloud subs operating under SAP's continuous delivery.

Alaska small businesses have structural advantages in federal contracting. How cloud engineering firms in Alaska can leverage those advantages for.

Migrating legacy DoD systems to cloud requires more than a lift-and-shift. Rutagon's approach to the real technical and compliance challenges of defense.

Infrastructure as Code on DoD cloud programs must be reproducible, auditable, and aligned with STIG compliance. Rutagon's production Terraform patterns.

A weak teaming agreement creates delivery risk on defense cloud programs. Key terms cloud engineering subs should require before signing with a prime.

Cloud engineering subs need to understand how federal contract vehicles work — GSA MAS, OASIS+, SEWP, and agency-specific IDIQs. Which vehicles matter.

Modern satellite ground systems leverage cloud-native architectures for antenna scheduling, data ingest, processing, and distribution. Rutagon's.
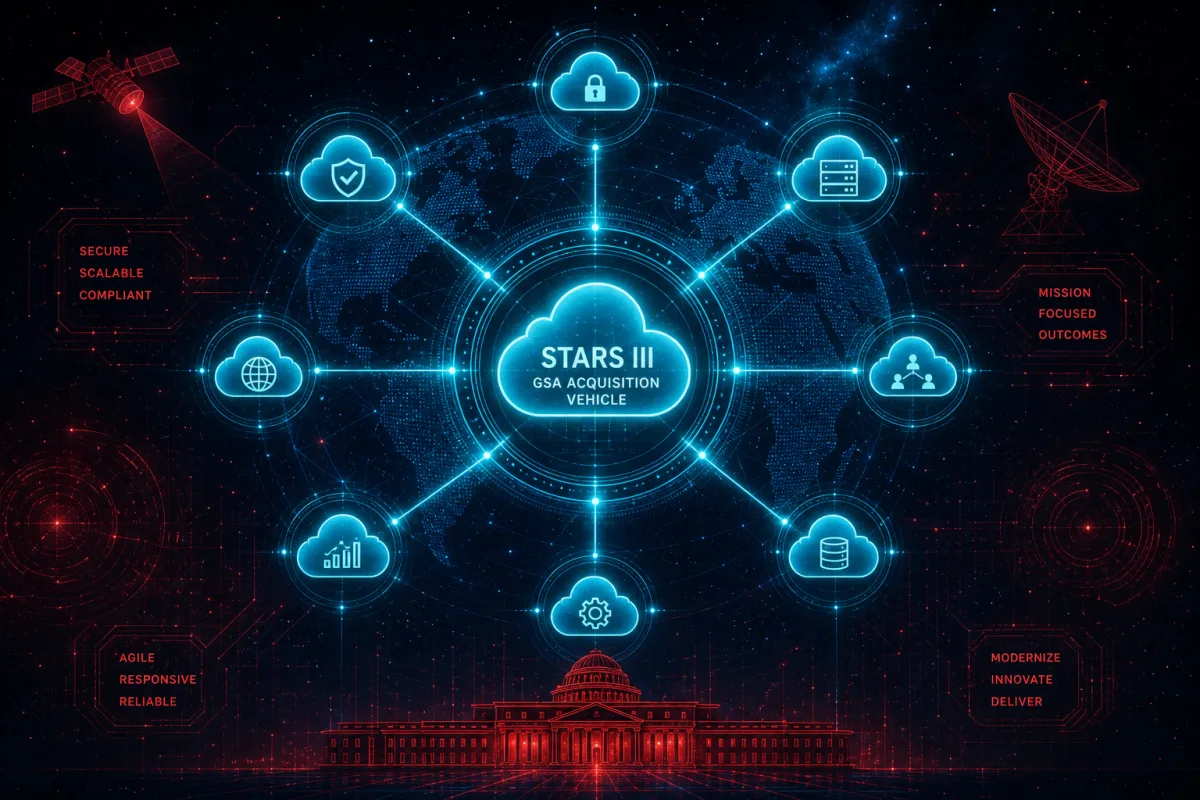
How Rutagon delivers cloud engineering on STARS III — technical capabilities, sprint delivery, and what primes gain from teaming with a cleared sub.

Rutagon delivers small satellite software as a subcontractor — ground software, telemetry pipelines, command uplink, and cloud-native mission systems.

A DCAA-compliant cloud subcontractor brings audit-ready billing, proper cost categorization, and transparent labor tracking to prime defense IT programs.
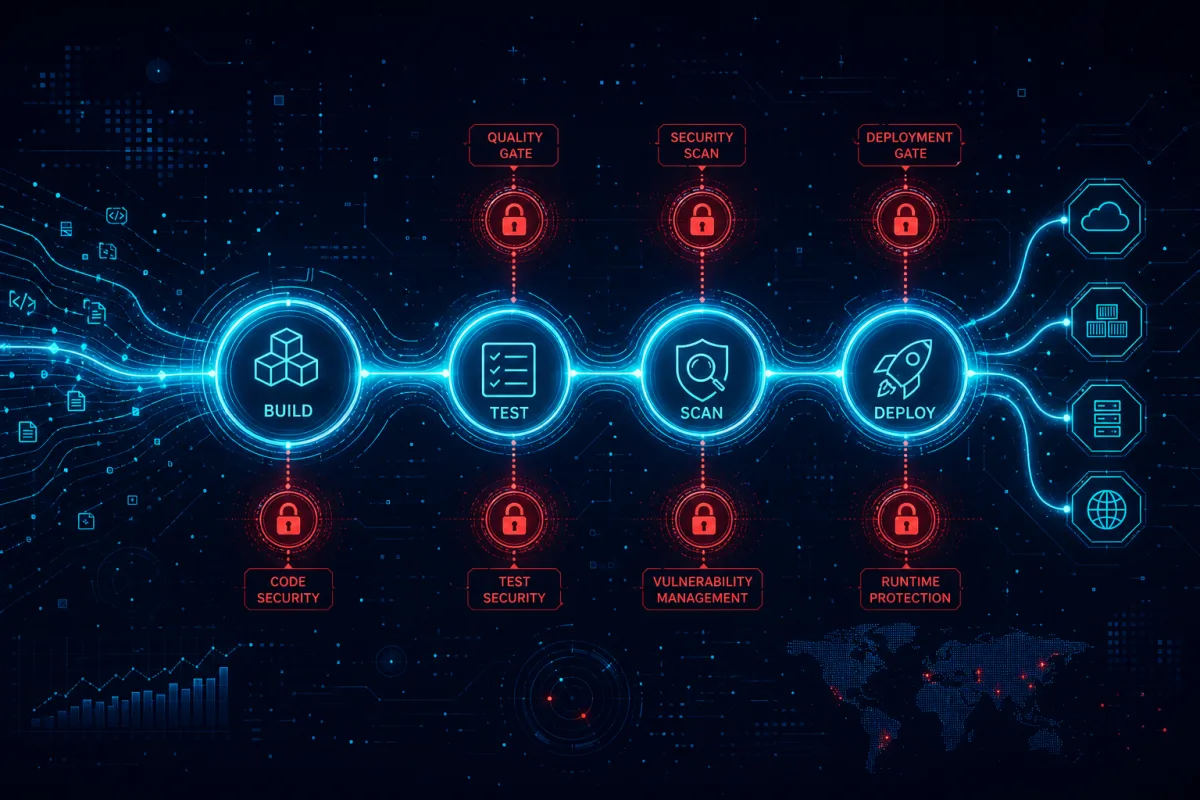
A cleared DevSecOps subcontractor delivers pre-built pipelines, Iron Bank containers, ATO-ready code, and sprint delivery for DoD prime programs.

How cloud engineering primes use Seaport NxG to bring in specialized IT subs — what Rutagon delivers on Navy and DoD programs via this IDIQ vehicle.

A government cloud sub delivers incident response infrastructure — detection pipelines, automated triage, and 72-hour DoD reporting capabilities.

How a cloud IT subcontractor delivers earned value management — tracking schedule, cost, and scope to protect prime CPARs and program health.

Rutagon delivers unmanned systems software as a subcontractor — autonomous operations software, mission data pipelines, and cloud-native ground control.

Why primes choose a small business defense IT subcontractor — SBA goal credit, agile delivery, and mission-ready cloud engineering capabilities.

How the AWS shared responsibility model applies to cloud subs on GovCloud — what Rutagon manages, what primes inherit, and security boundaries.

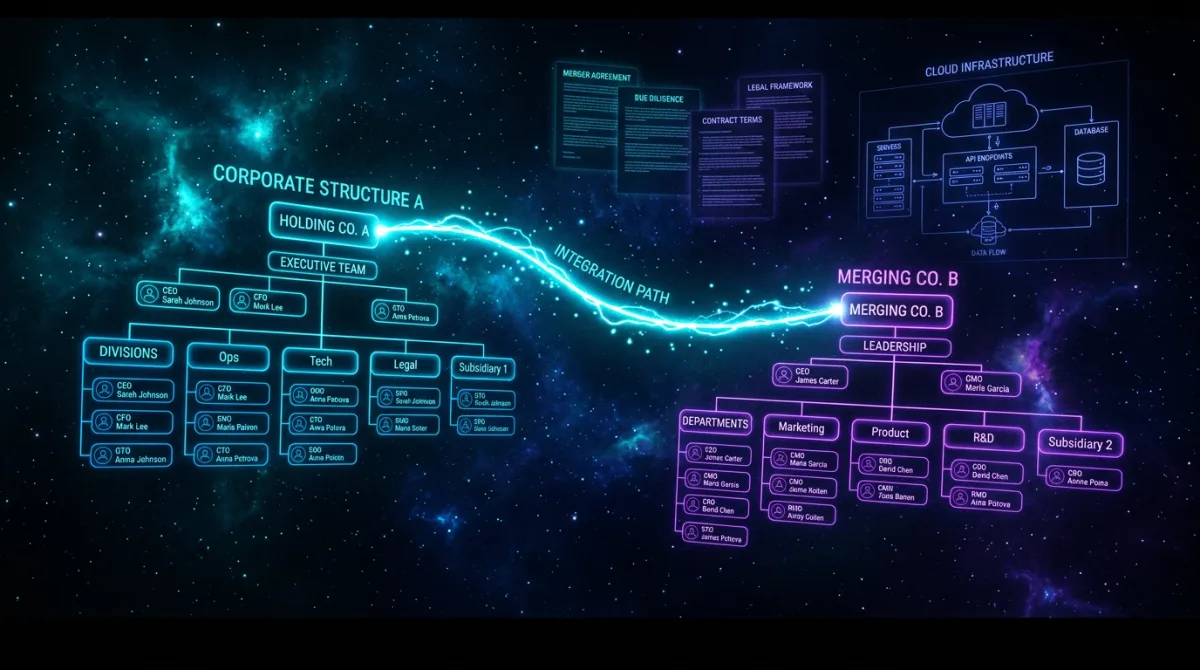
How cloud-focused joint ventures between small businesses and primes unlock federal contracts neither could win alone under SBA rules.
Key FAR and DFARS clauses that must flow down to cloud IT subcontractors and what compliant subs already have in place to accept them.

How your cloud subcontractor's delivery directly impacts your CPARS rating across all six evaluation areas and future contract competitiveness.

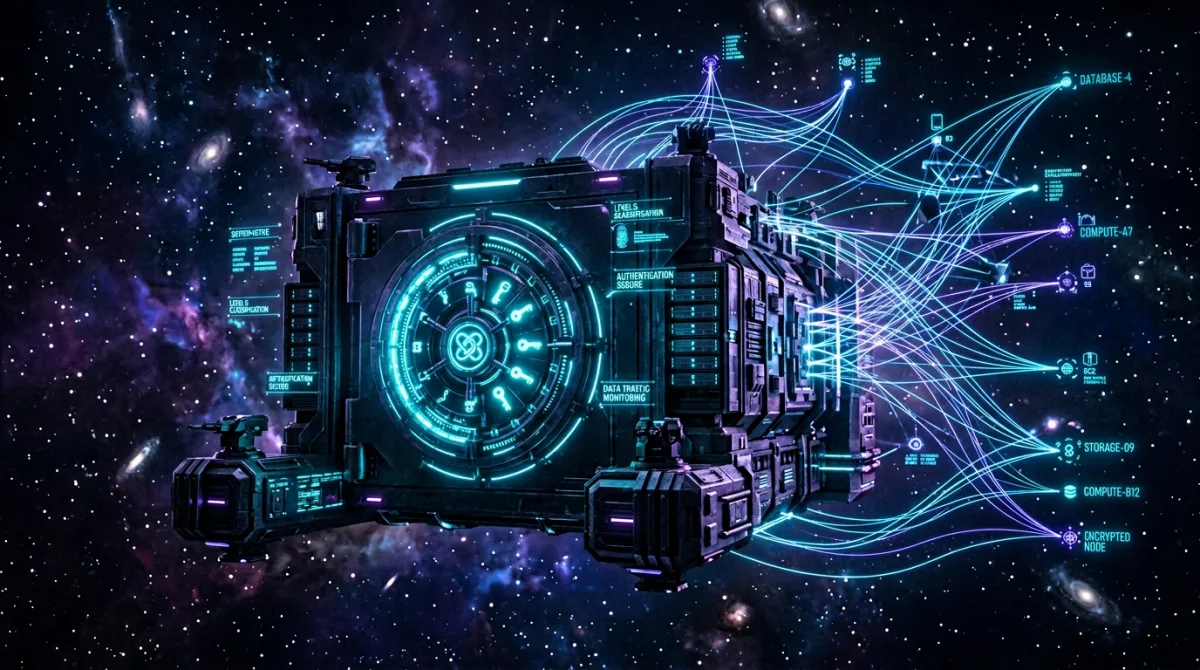
DoD zero trust mandates require specialized cloud subcontractors who deliver identity federation, microsegmentation, and continuous verification.

A cloud engineering sub compresses IDIQ task order proposal timelines with ready-made technical volumes, staffing matrices, and past performance.

Federal cloud migration task orders need a subcontractor who delivers GovCloud expertise, Terraform IaC, and ATO continuity during cutover.

How a cloud engineering subcontractor compresses ATO timelines by generating authorization artifacts directly from CI/CD pipelines.

How a SAM-registered cloud subcontractor simplifies ISR and SSR compliance for prime contractors on federal contracts.

Learn what prime contractors gain from a DoD Mentor-Protege agreement with a cloud engineering protege and how it satisfies SBA goals.

How a cloud engineering subcontractor integrates into SAFe and Scrum rhythms on government programs without slowing the prime's team.

Small satellite ground software stack design — pass scheduling, telemetry decode, command uplink, cloud-native K8s operations, and ATO-aligned architecture.

DoD Zero Trust 5 pillars mapped to cloud-native implementation — identity, device, network, application, and data controls in GovCloud and DoD environments.
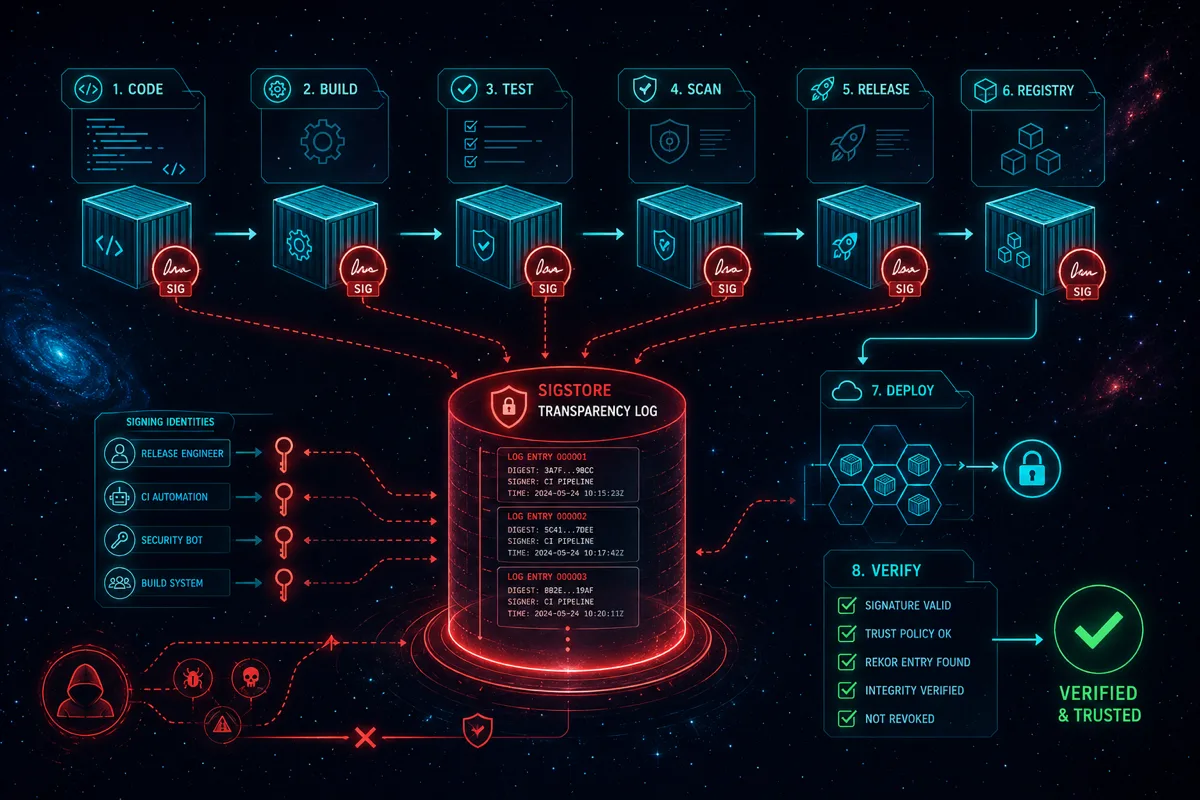
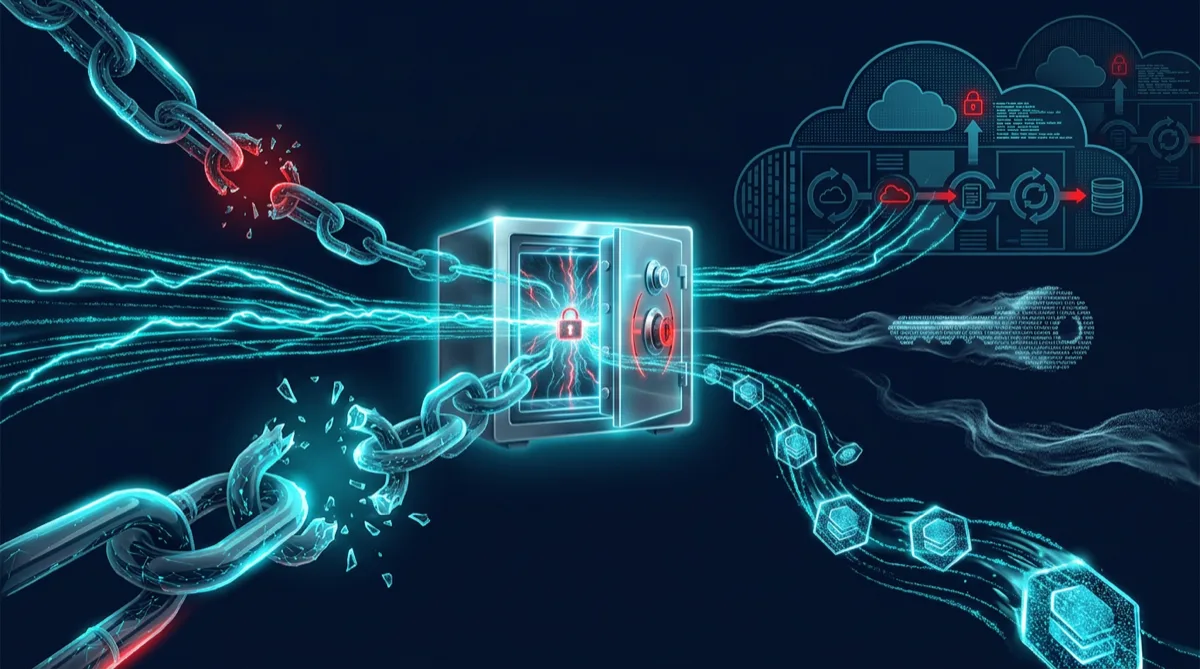
Container image signing with Cosign and Sigstore for federal CI/CD — supply chain integrity, SLSA provenance attestations, and ATO evidence generation.
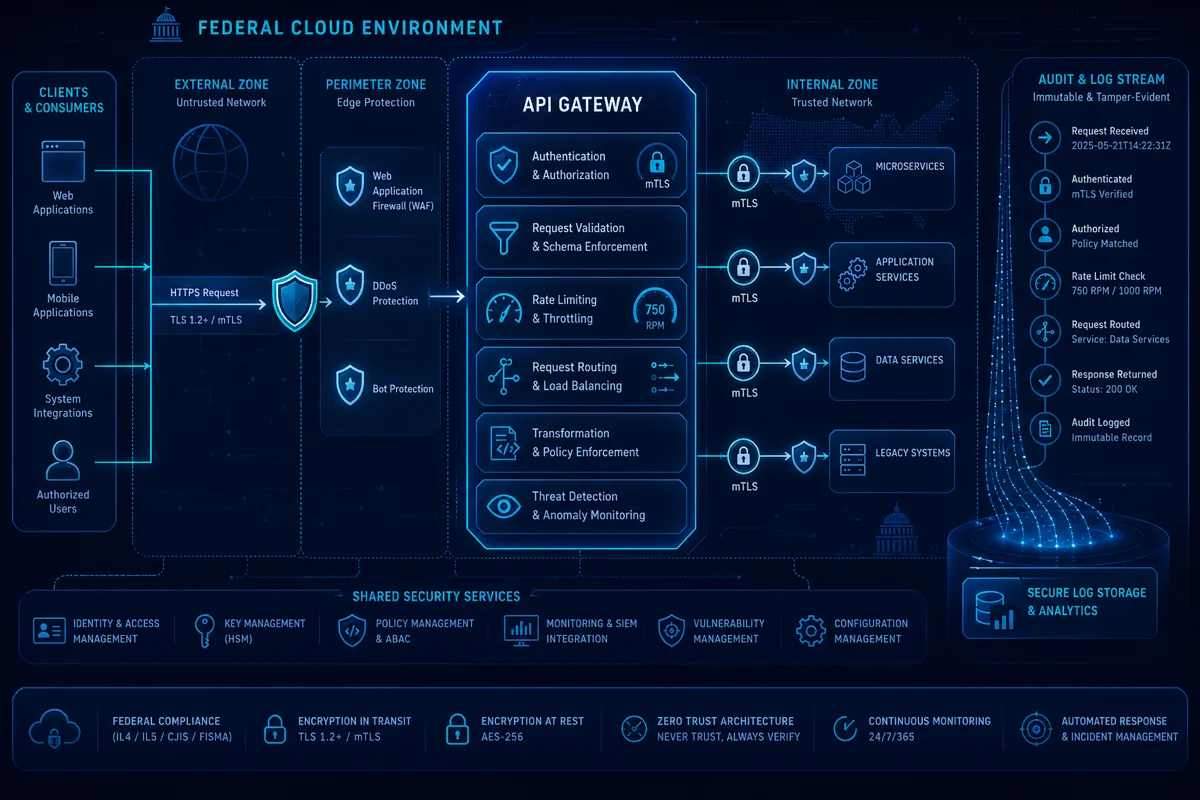
API gateway patterns for FedRAMP and DoD cloud programs — AWS API Gateway, mTLS enforcement, rate limiting, audit logging, and NIST control mapping.
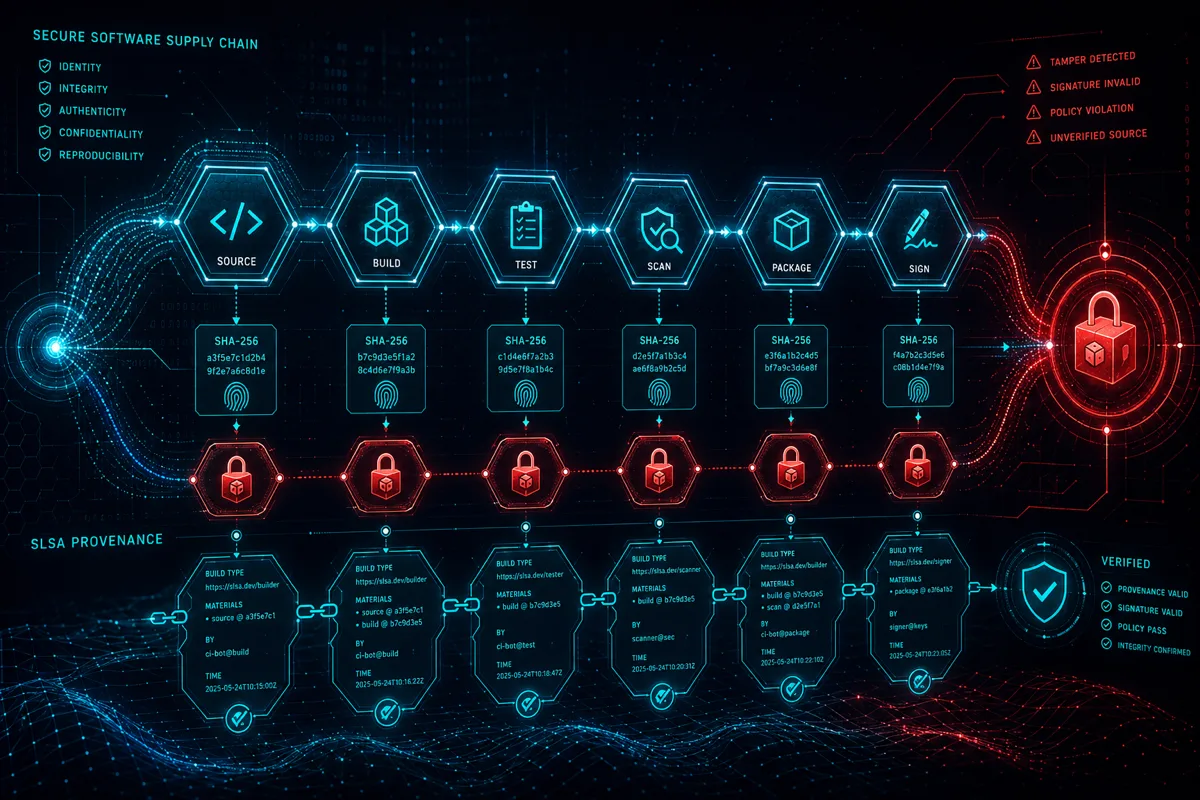
SLSA supply chain security for federal programs — provenance generation, artifact integrity, hardened build environments, and NIST 800-161 control mapping.

Production defense software factory on DoD Cloud One — hardened CI/CD, Iron Bank container integration, automated cATO evidence generation, and security gates.
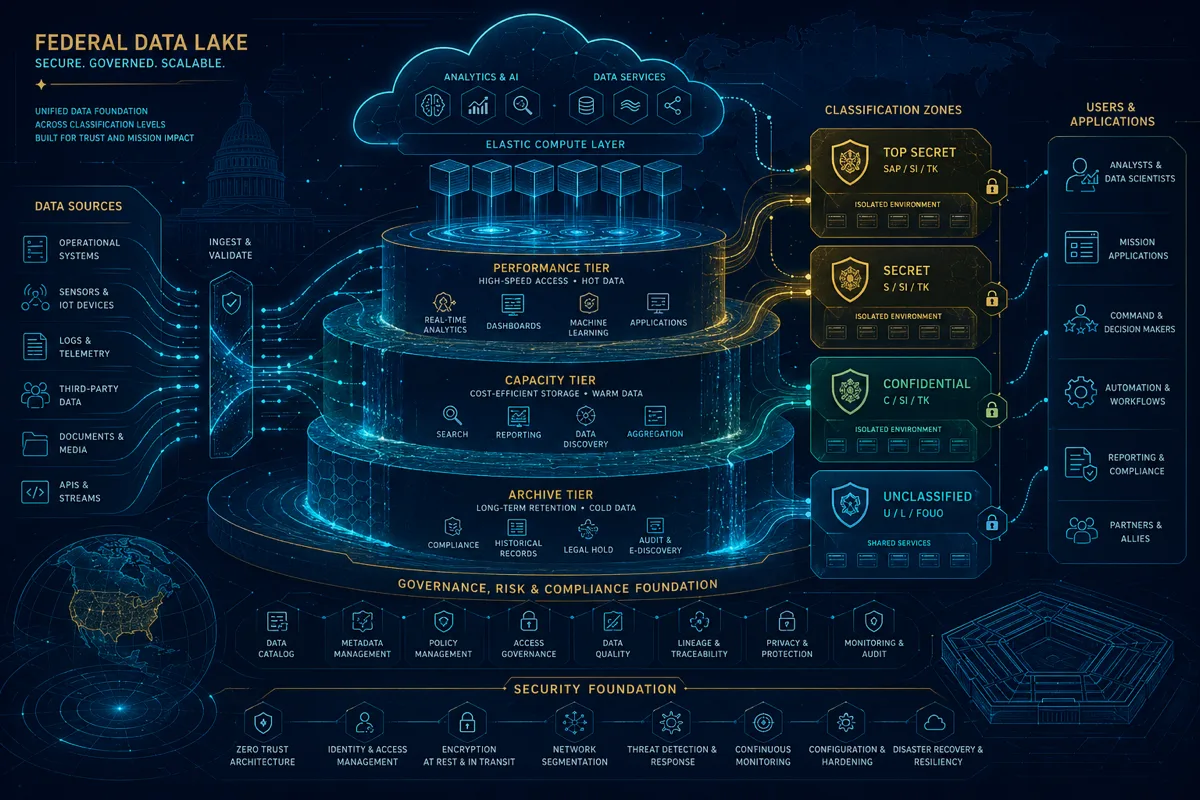
Compliant data lake architecture on AWS GovCloud — S3 with Object Lock, Lake Formation ABAC, Macie classification, Glue cataloging, and NIST control mapping.

NDAA Section 5949 compliance for defense cloud programs — semiconductor prohibitions, CSP attestations, SBOM requirements, and what cloud engineering subs must document.
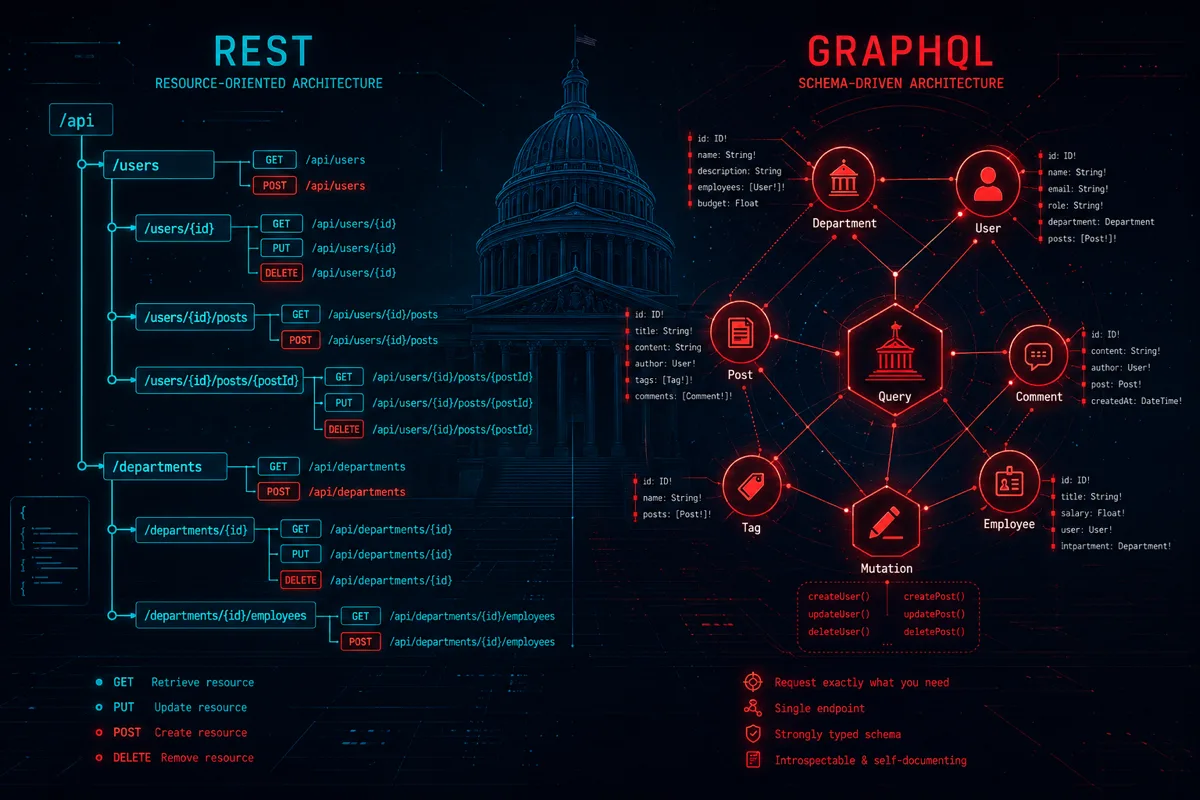
GraphQL vs REST for federal government APIs — security trade-offs, FedRAMP compliance, field-level authorization, audit logging, and production deployment patterns.
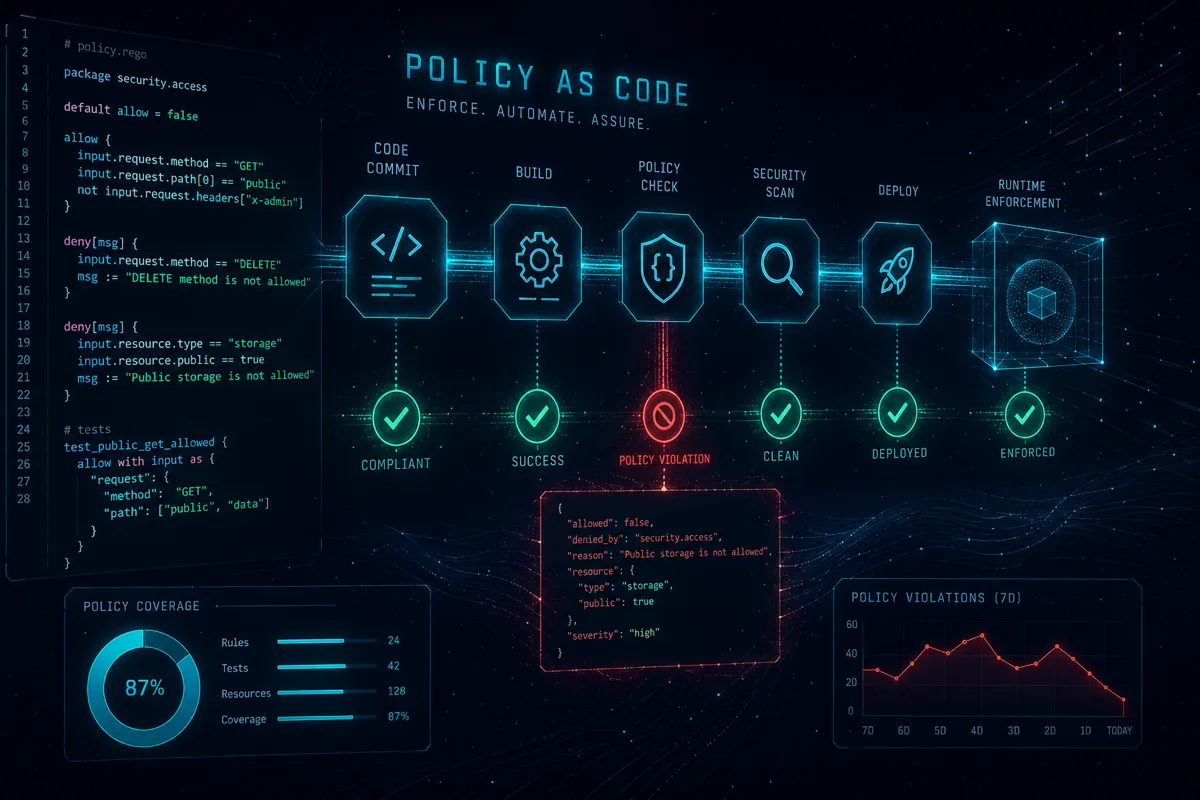
Policy-as-code with OPA and Rego for federal CI/CD — NIST 800-53 control gates in Terraform validation, Kubernetes admission control, and ATO evidence generation.
NDAA Section 889 compliance — prohibited technology lists, cloud service vetting, telecom bans, and contractor obligations for federal programs in 2026.
Platform engineering for federal teams — internal developer platforms, paved-path CI/CD, self-service infrastructure, and ATO acceleration patterns.

SBA sole source contracts — 8(a), HUBZone, and SDVOSB thresholds, justification requirements, and what prime contractors need from small business subs.

AWS Backup for government NIST compliance — CP-9/CP-10 control mapping, cross-region replication, Vault Lock, and ATO-ready backup testing documentation.

JADC2 software architecture — data mesh patterns, API-first interoperability, and edge-cloud distribution for multi-domain command and control operations.

NIST CSF 2.0 cloud implementation — the new Govern function, AWS GovCloud control mapping, FedRAMP and CMMC alignment for federal cloud programs in 2026.

Air-gapped Kubernetes in classified environments — registry mirroring, offline Helm, STIG hardening, and patterns for disconnected government systems.

CubeSat ground software — pass scheduling, telemetry decode, command uplink, and cloud-native ground system design patterns for small satellite missions.

Security clearances for small defense contractors — FCL vs PCL, FOCI issues, clearance timelines, and prime teaming strategies for cleared program work.

FISMA impact levels for cloud — Low, Moderate, and High thresholds, GovCloud implications, and how impact level drives your ATO boundary decisions.

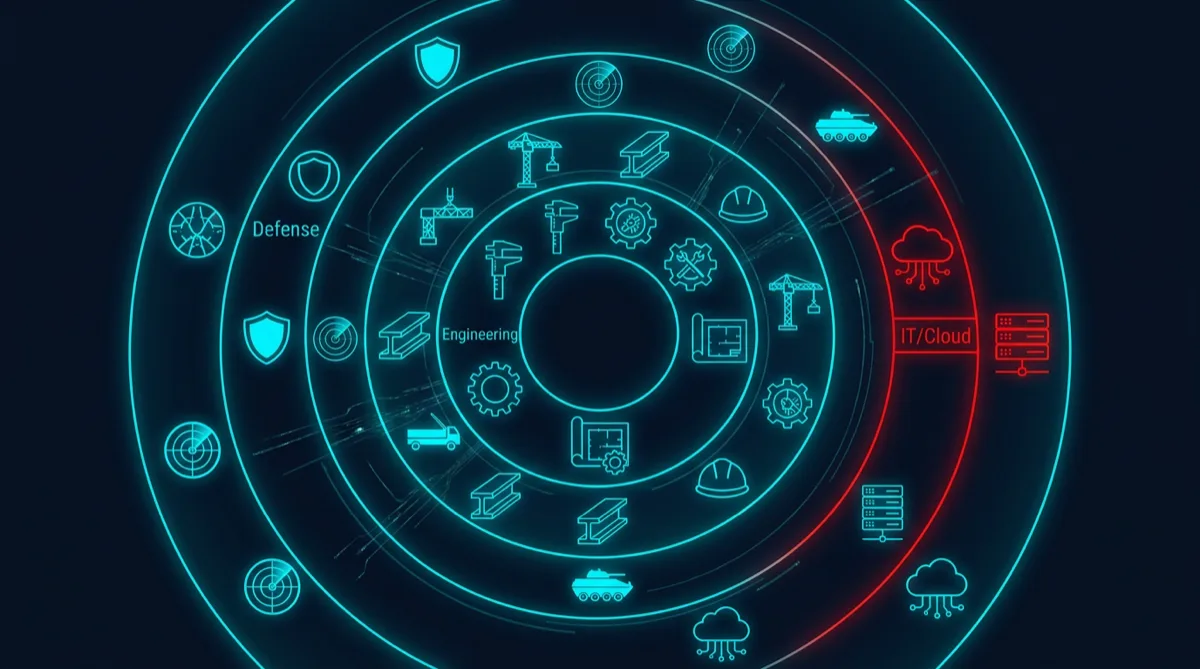
Why Alaska-based defense tech offers unique strategic value — geographic positioning, Arctic program access, and Rutagon's small business edge.
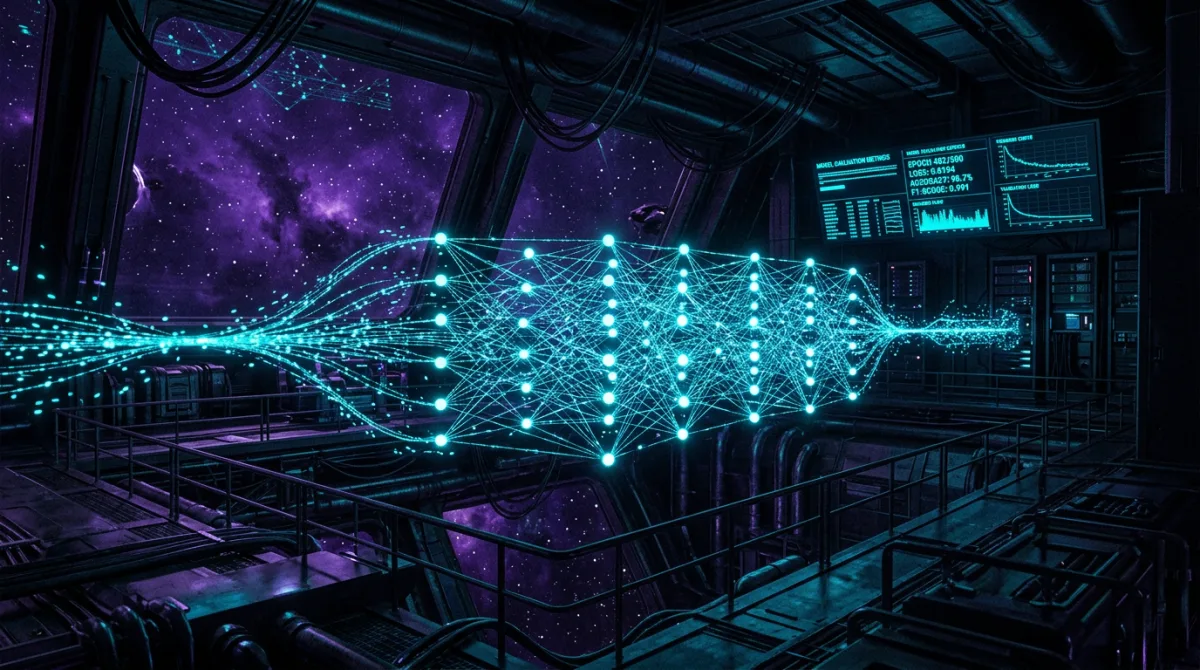
MLOps pipelines on AWS GovCloud IL5 — model training, validation, monitoring, and deployment for defense AI programs with NIST 800-53 compliance.

Migrating Oracle to PostgreSQL in government cloud — schema conversion, data migration, PL/SQL refactoring, Aurora GovCloud setup, and ATO continuity.
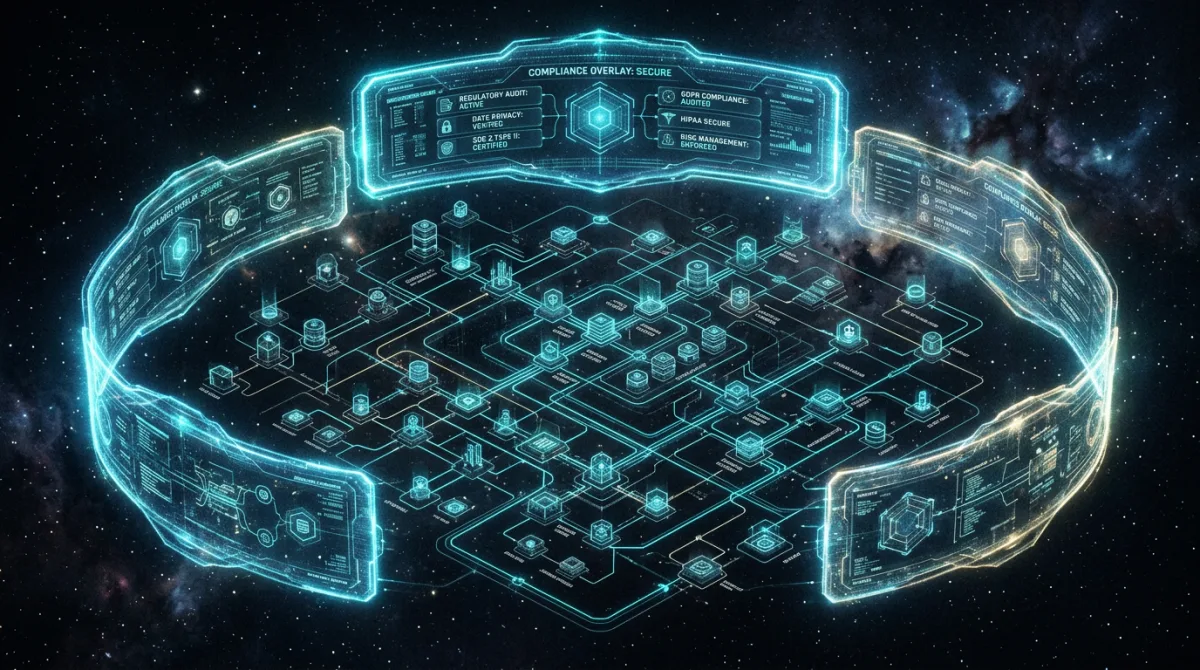
Building cloud-native applications that satisfy FedRAMP, CMMC, and NIST 800-53 simultaneously — architecture patterns, security controls, and ATO strategy.
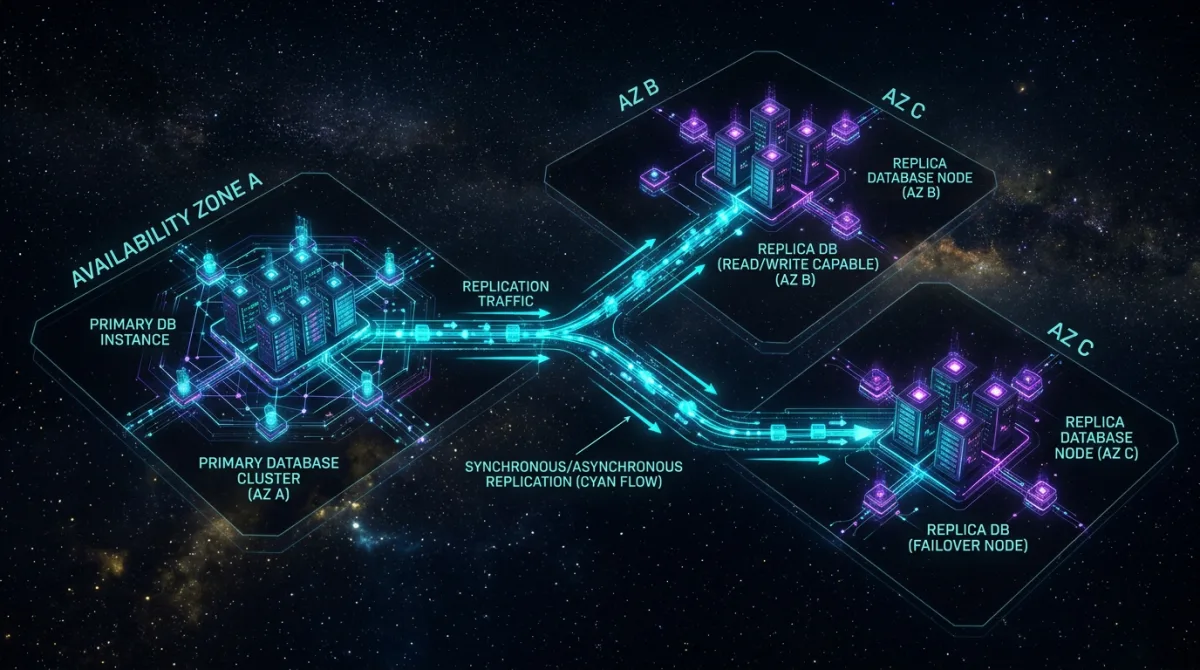
PostgreSQL HA on AWS GovCloud — multi-AZ RDS, Aurora Serverless failover, FIPS 140-2 encryption, and NIST 800-53 compliant database resilience patterns.
What prime contractors get from a cloud engineering sub — delivery model, compliance posture, past performance, and why Rutagon fits federal IDIQ programs.
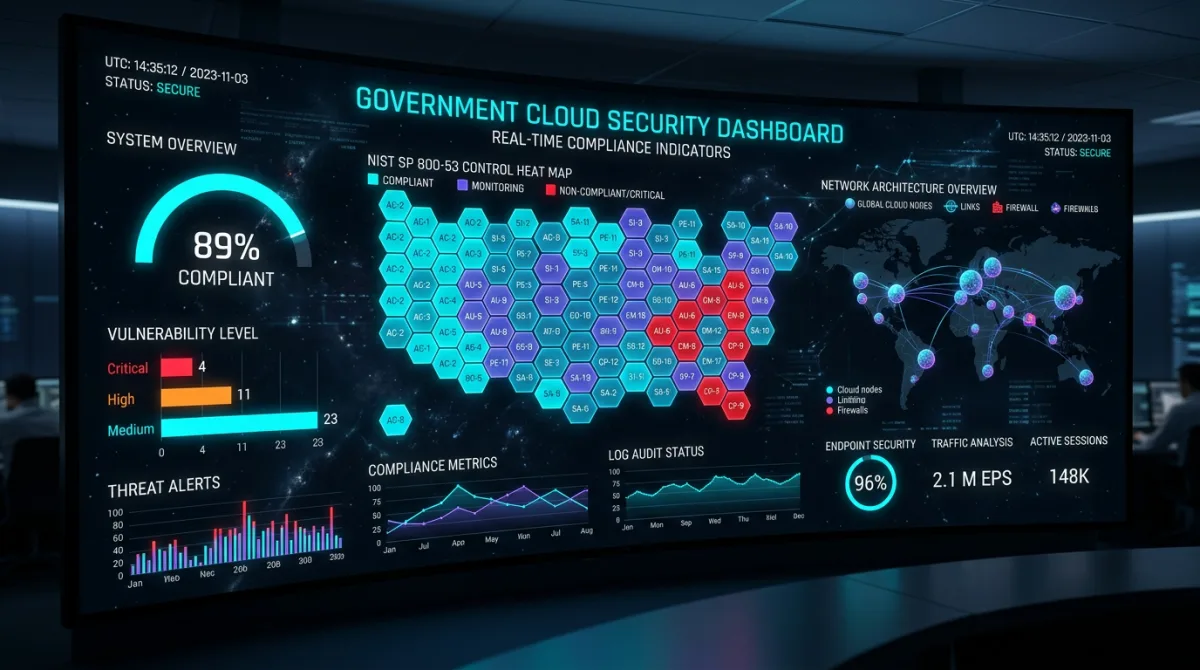
CSPM on AWS GovCloud — Config rules, Security Hub, GuardDuty tuned for NIST 800-53, and automated ConMon evidence for federal ATO programs.
Istio service mesh in federal cloud — mTLS enforcement, traffic policy, observability, and NIST 800-53 alignment for government Kubernetes workloads.
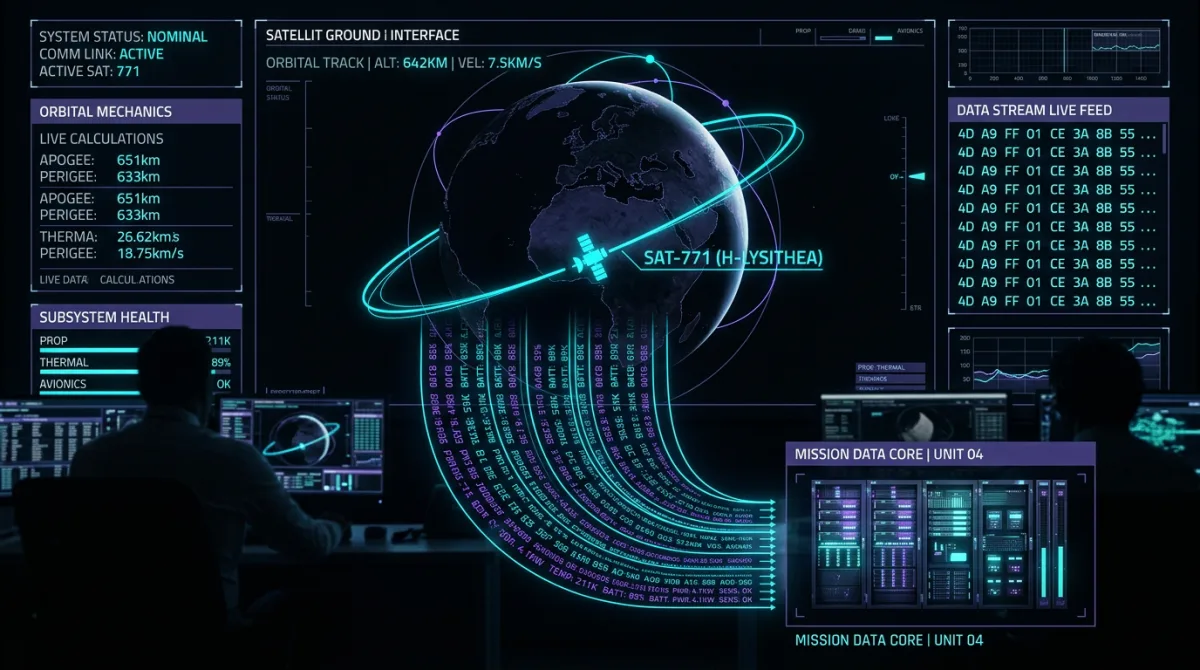
Cloud-native satellite C2 architecture — containerized microservices, CCSDS telemetry pipelines, and Kubernetes HA for space ground systems.
Eliminate long-lived secrets in GovCloud with AWS Secrets Manager, Parameter Store, and IRSA — patterns for NIST 800-53 IA-5 compliance in federal systems.

How to implement OpenTelemetry distributed tracing in AWS GovCloud — collector setup, OTLP config, sampling strategies, and FedRAMP-aligned observability pipelines for federal systems.
Kubernetes Network Policy patterns for GovCloud compliance — default deny, namespace isolation, ingress/egress controls, and how network policies satisfy NIST 800-53 SC-7.
How Other Transaction Authority (OTA) works for DoD software programs — agreement types, eligibility, prototype-to-production transitions, and key subcontractor requirements.

Architecture patterns for on-orbit spacecraft software updates — commanding systems, verification protocols, rollback mechanisms, and ground-to-space software delivery design.

How to architect multi-tenant SaaS for FedRAMP — tenant isolation models, data partitioning strategies, shared infrastructure controls, and ATO boundary decisions.

How DoD Acquisition Category (ACAT) levels work for software programs — ACAT I through III thresholds, acquisition milestones, and what IT subcontractors need to deliver.
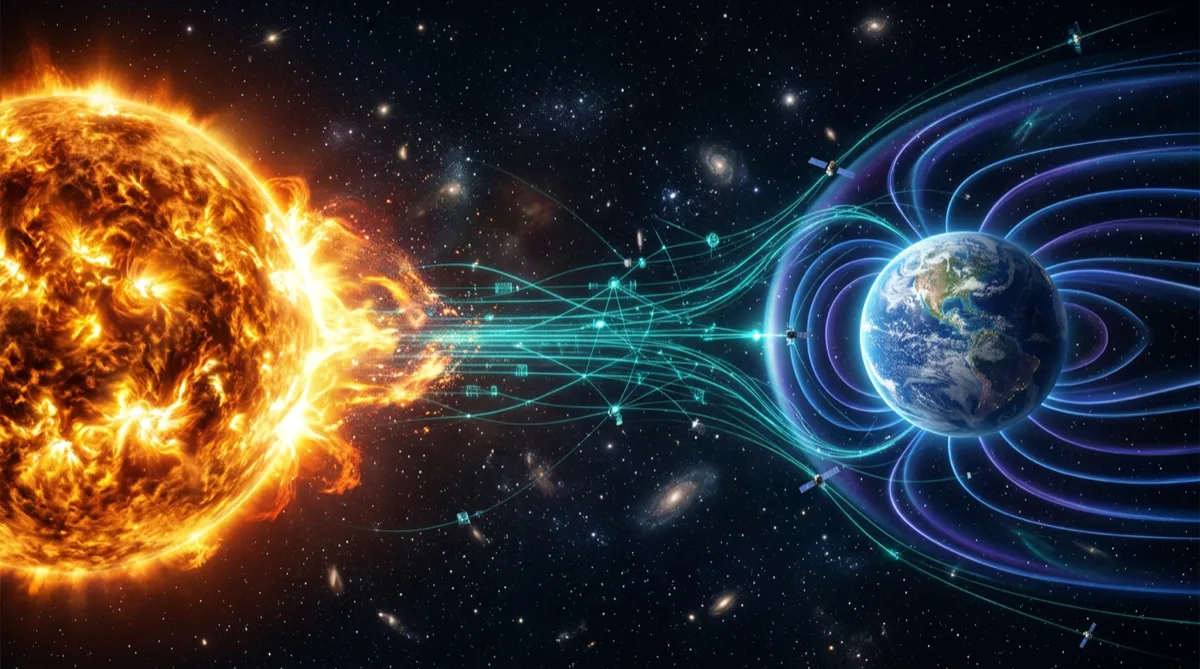
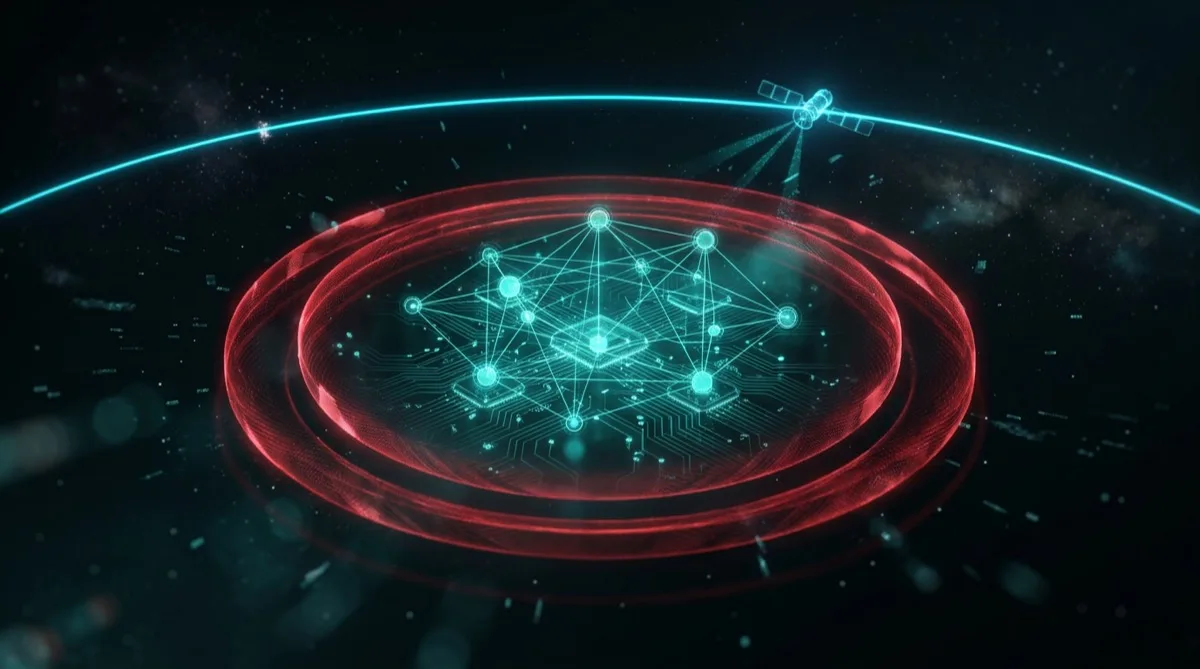
Engineering architecture for space weather data systems — sensor data ingestion, real-time processing pipelines, alert generation, and ground software design for satellite programs.

How to implement SRE error budgets in federal cloud — SLO definition, error budget calculation, compliance-aligned reliability targets, and burn rate alert architecture.

How performance-based contracting works for government IT — PBSA structure, performance work statements, AQLs, incentive fee mechanisms, and what technology subs must deliver.
Engineering velocity in defense tech — CI/CD automation, pre-built compliance modules, lean team design, and why speed and compliance reinforce each other.
Terraform state management for GovCloud — S3 backend, state locking, workspace strategies, and CI/CD integration patterns for federal programs.
How a cloud engineering sub accelerates FedRAMP authorization — SSP development, control implementation, ConMon setup, and what primes should expect.
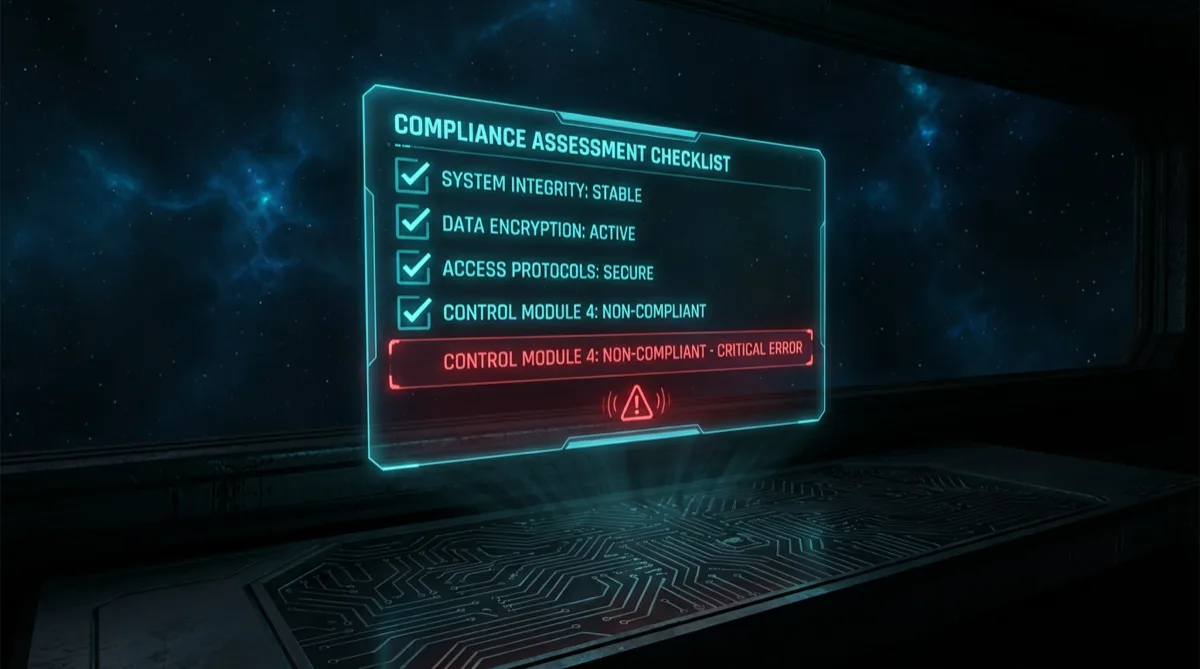
How to prepare for CMMC Level 2 C3PAO assessment — technical controls, evidence collection, gap closure, and what assessors actually evaluate.
Azure Government vs AWS GovCloud — a technical comparison of compliance posture, service coverage, IaC portability, and delivery fit for federal programs.
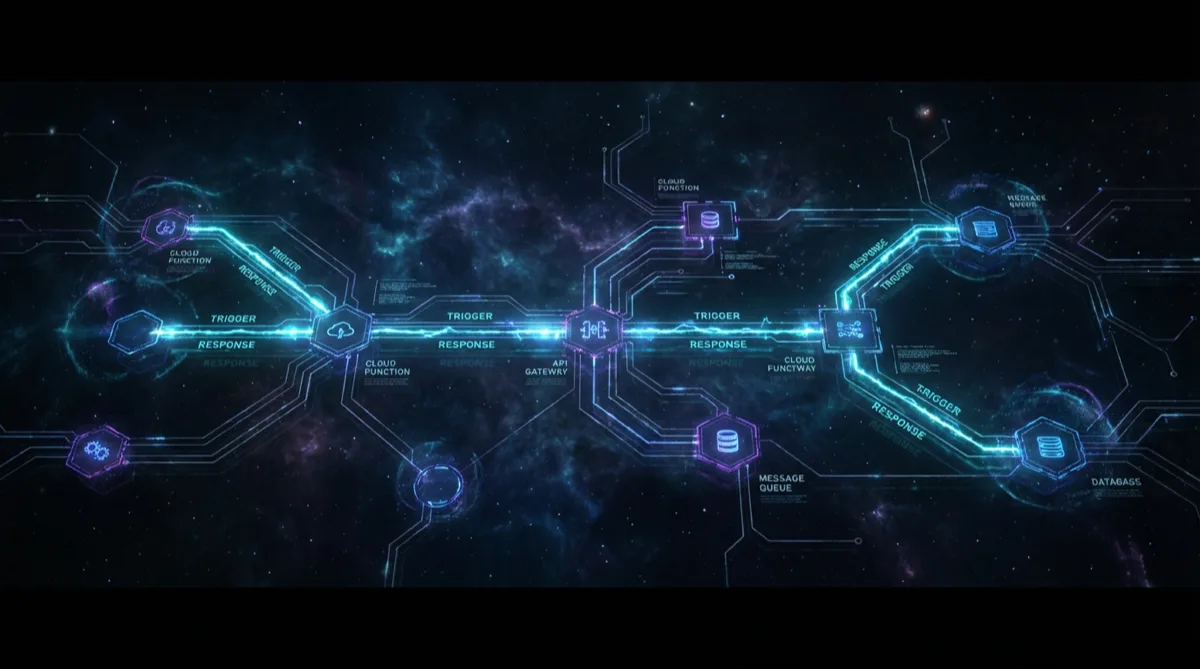
AWS Lambda in FedRAMP and CMMC environments — cold start mitigation, VPC config, IAM patterns, FISMA-aligned deployment, and government program lessons.
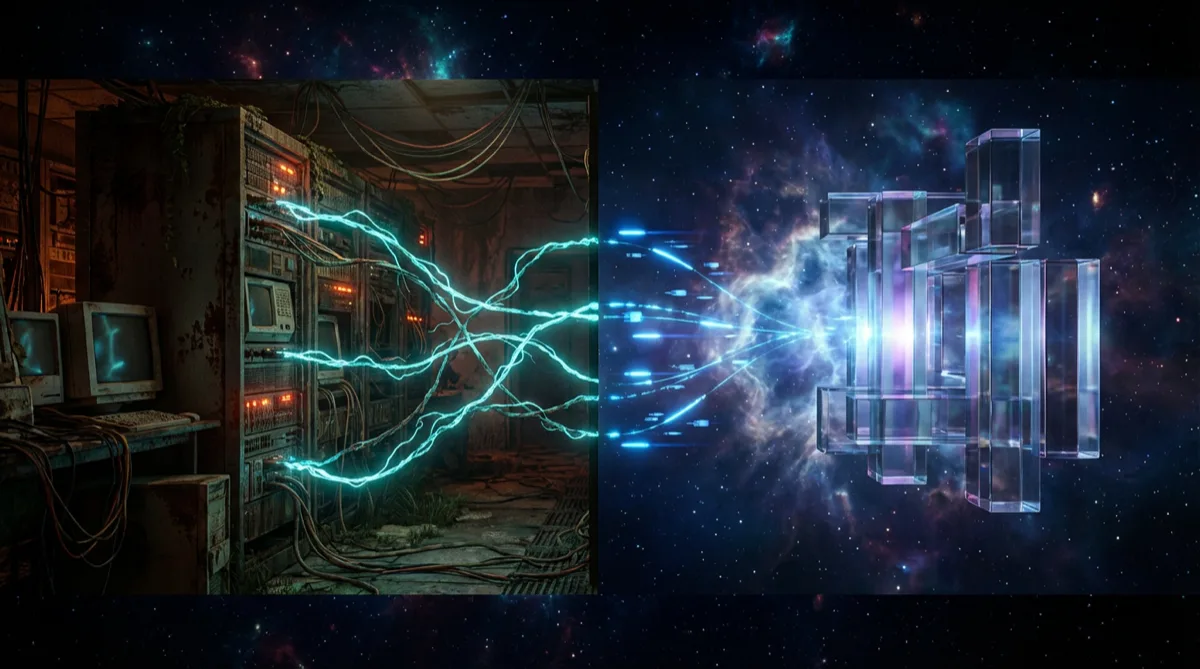
Practical government IT modernization — phased cloud migration, ATO continuity, legacy strangler-fig patterns, and what primes should expect.
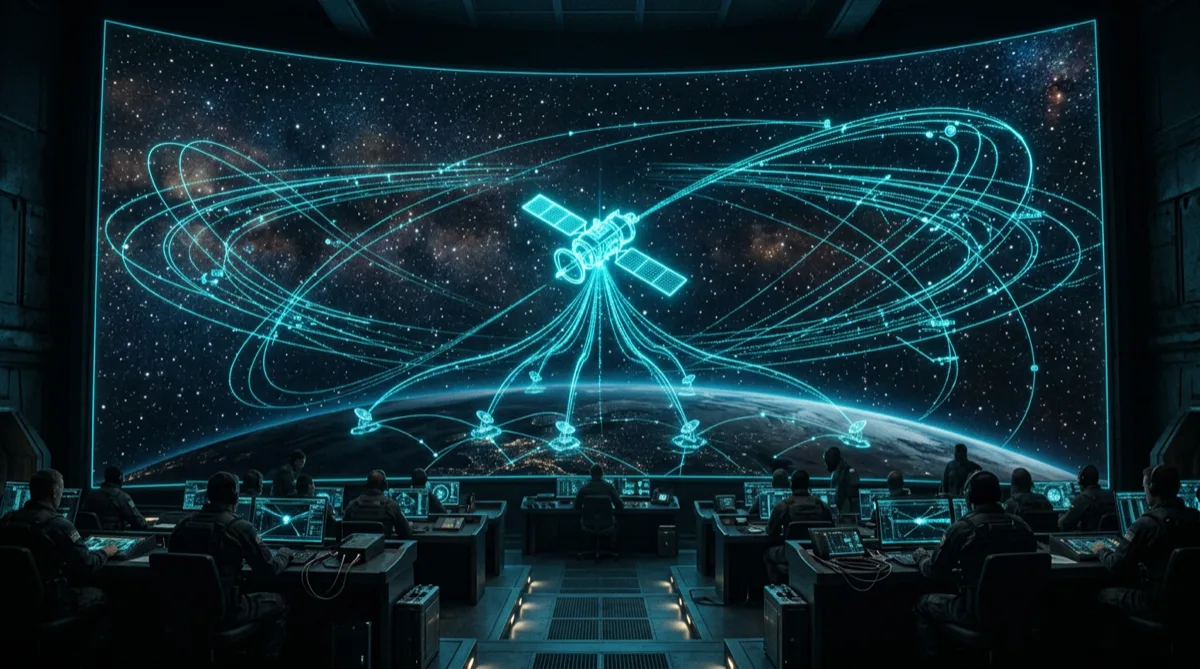
Cloud-native ground software architecture for Space Force programs — telemetry pipelines, command and control patterns, and resilience design.
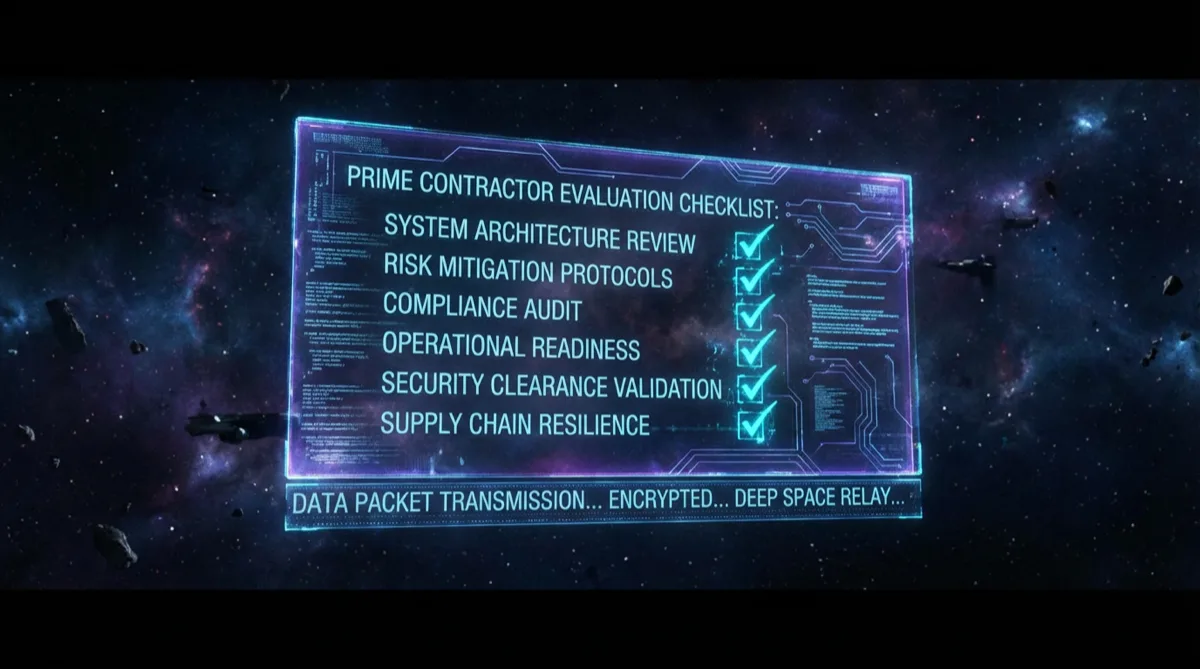
What prime BD teams should evaluate when vetting a defense cloud sub — delivery model, compliance posture, past performance, and technical fit.
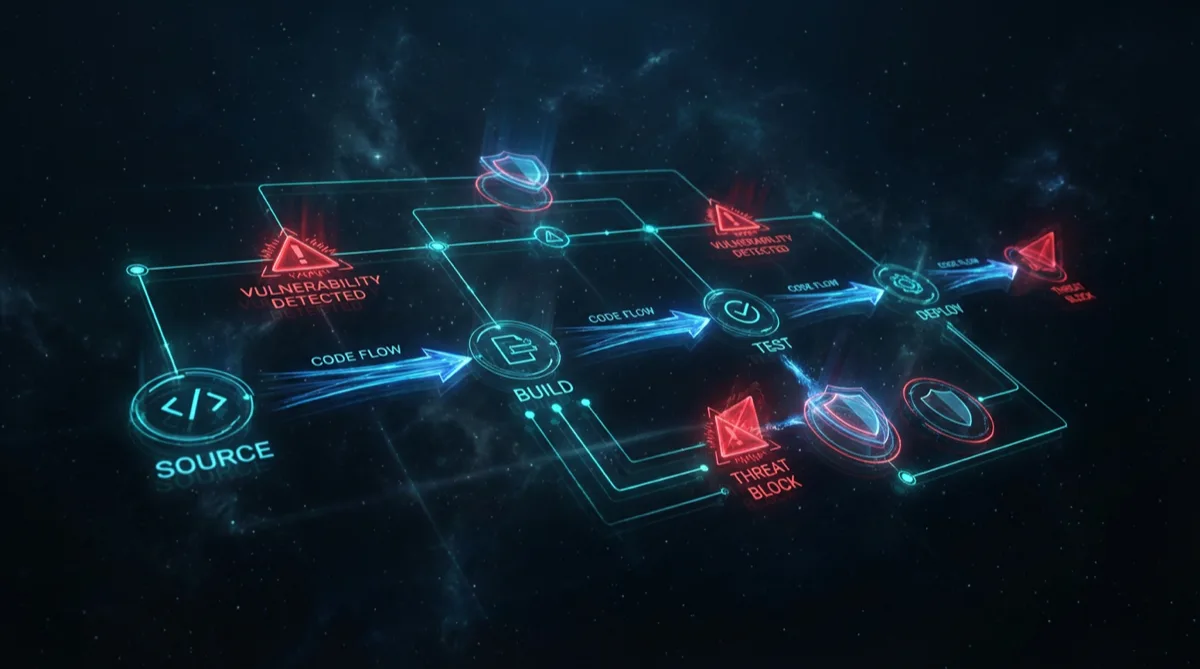
SAST and DAST in federal CI/CD pipelines — tools, DISA STIG scanning, vulnerability SLAs, and AppSec testing patterns for government programs.
Applying DISA STIGs to cloud environments — automated scanning, container baselines, network layer controls, and GovCloud-specific configuration patterns.
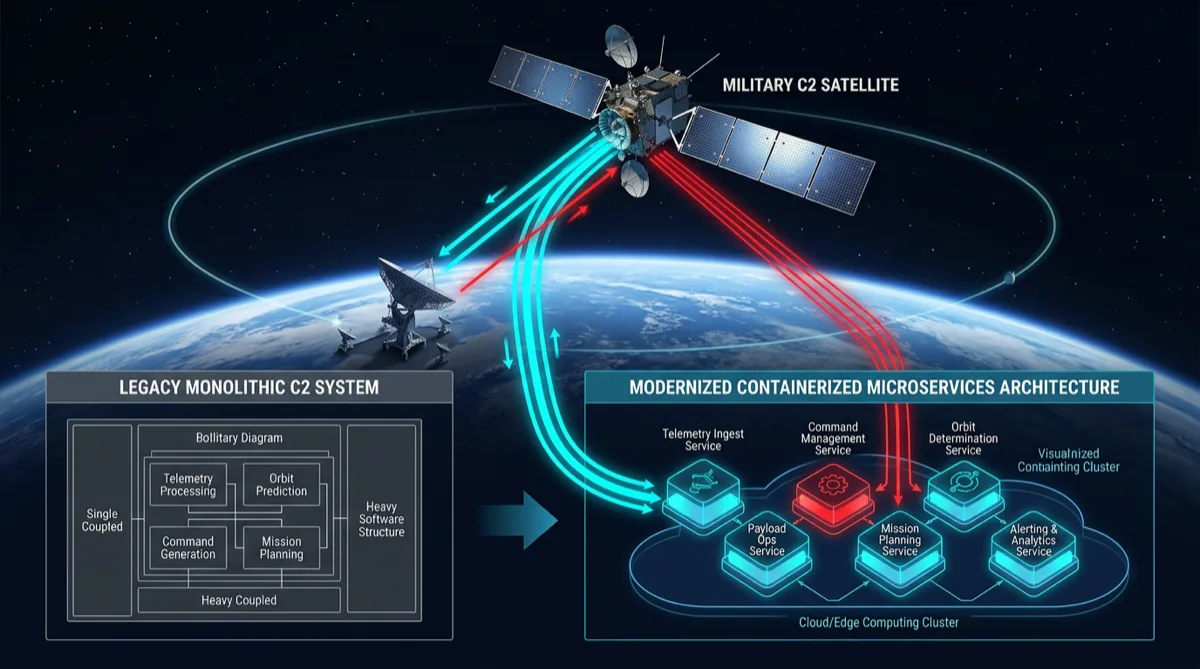
Satellite command and control re-architecture on GovCloud — service decomposition, telemetry pipelines, Iron Bank containers, and cATO alignment.
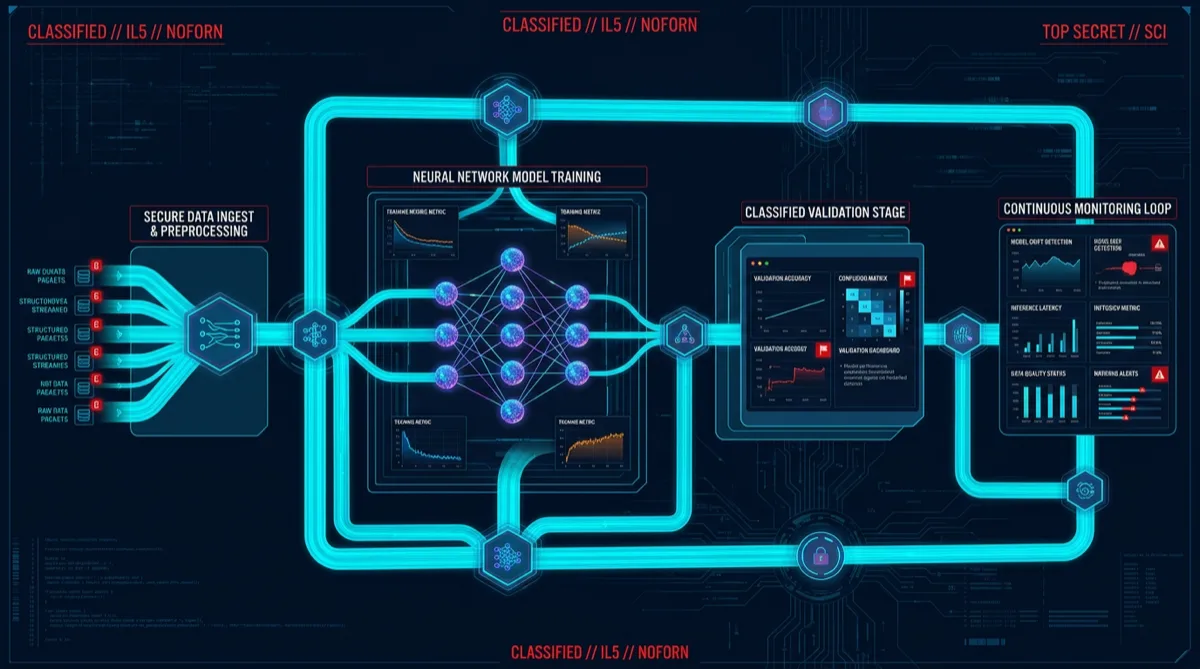
MLOps on IL5 classified cloud — model training, validation, monitoring at classification level, GovCloud tooling, and AI/ML for defense programs.
Istio service mesh for government cloud — mTLS zero trust, traffic policy, GovCloud Kubernetes observability, and production mesh deployment patterns.
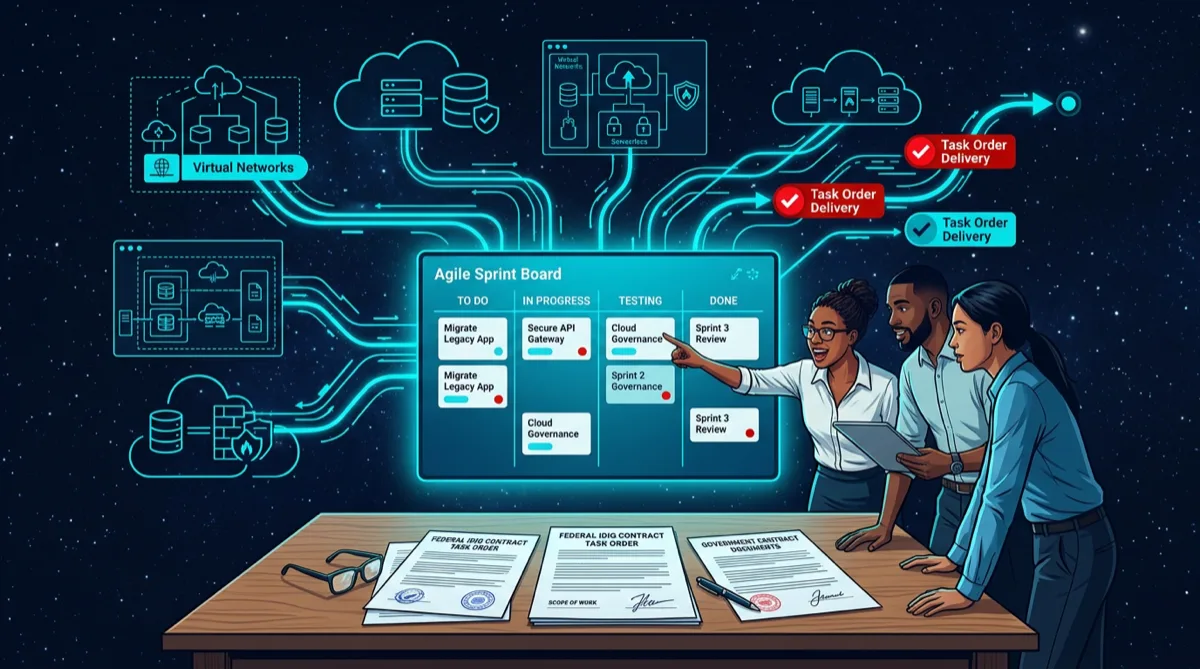
How cloud engineering subs work on IDIQ task orders — delivery model, ATO documentation, sprint cadence, and why small businesses win repeat orders.
Eliminating long-lived secrets in AWS GovCloud — Secrets Manager, Parameter Store, IRSA, and zero-secret CI/CD pipelines for federal programs.

CSPM on AWS GovCloud for NIST 800-53 — Config rules, Security Hub, GuardDuty for government, and automated posture monitoring for federal cloud.
Cloud-native application architecture for FedRAMP, CMMC Level 2, and NIST 800-53 — patterns that bake compliance in from the start.
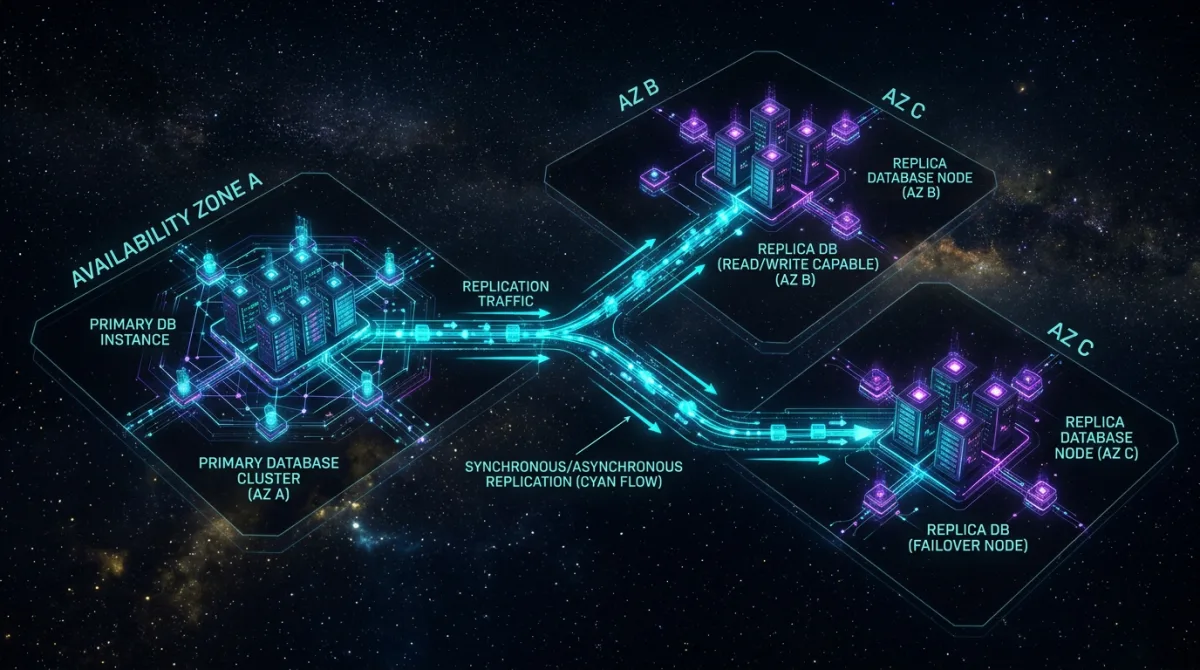
High-availability PostgreSQL on AWS GovCloud — multi-AZ RDS, Aurora Postgres, automated failover, and compliance-ready database architecture.

Oracle to PostgreSQL migration for government legacy systems — cost savings, migration patterns, schema conversion, and open-source compliance approach.

How HUBZone tech companies win defense contracts — set-aside eligibility, price preferences, Alaska advantage, and cloud engineering sub value.
ITAR-compliant cloud requires US-person access, data residency, and export controls. What prime contractors should expect from a cloud engineering sub.
What prime contractor BD teams look for when vetting a cloud engineering sub — technical criteria, past performance, teaming fit, and red flags to avoid.
API modernization of legacy government systems using the strangler-fig pattern. Contract-first design, phased extraction, and what primes should expect.
CUI creates specific cloud architecture requirements. What CUI-capable delivery looks like and what prime contractors should verify before subcontracting.
Section 508 requires federal web apps to be accessible. What technical compliance requires and how to build and deliver it on government programs.

How a high-performing federal IT sub structures delivery — sprint cadence, documentation, ATO evidence, and reporting that makes primes' lives easier.
SBIR Phase II-to-III transitions fail without the right engineering infrastructure. What primes and SBIR awardees need to scale prototype to production.
Defense microservices have constraints commercial software doesn't. What containerized, cATO-aligned delivery looks like as a defense program sub.
DoD's digital engineering mandate requires MBSE integration. What the software side means for engineering subs and prime contractor programs.
A pre-built DevSecOps pipeline accelerates prime task order delivery. What it includes, how it integrates with government programs, and what it delivers.

How Alaska-based defense technology companies use the SBA 8(a) program — eligibility requirements, sole-source award thresholds, Alaska Native Corporation advantages, and program strategy.
How federal agencies implement data mesh architecture — domain-driven data products, CDAO alignment, access control patterns, and cloud-native delivery on AWS GovCloud.

A phased government cloud migration strategy — impact level boundary mapping, lift-shift-modernize sequencing, ATO continuity, and production patterns for federal workloads on AWS GovCloud.
Software architecture patterns for missile defense systems — real-time data pipelines, sensor fusion at scale, fault-tolerant C2 design, and cloud-native modernization on AWS GovCloud.
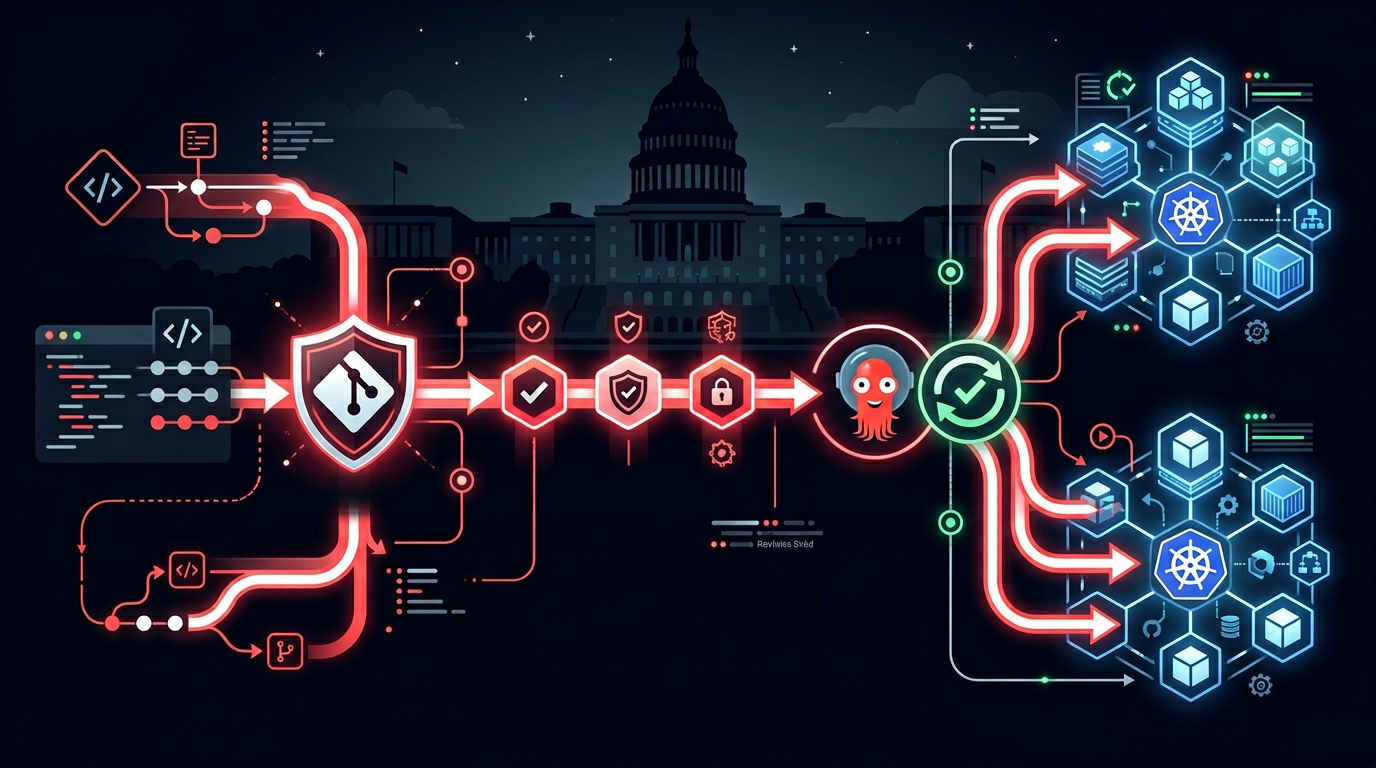
GitOps patterns for auditable, rollback-ready federal deployments — signed commits, pull request approval gates, ArgoCD on GovCloud Kubernetes, and immutable audit trails for FISMA compliance.
How small business IT contractors access DoD work through JWCC — task order structure, cloud provider options, teaming with JWCC holders, and what agencies buy through the vehicle.

Design patterns for multi-classification cloud environments spanning IL2 through IL5 — account segmentation, cross-domain data controls, shared services architecture, and GovCloud boundary enforcement.
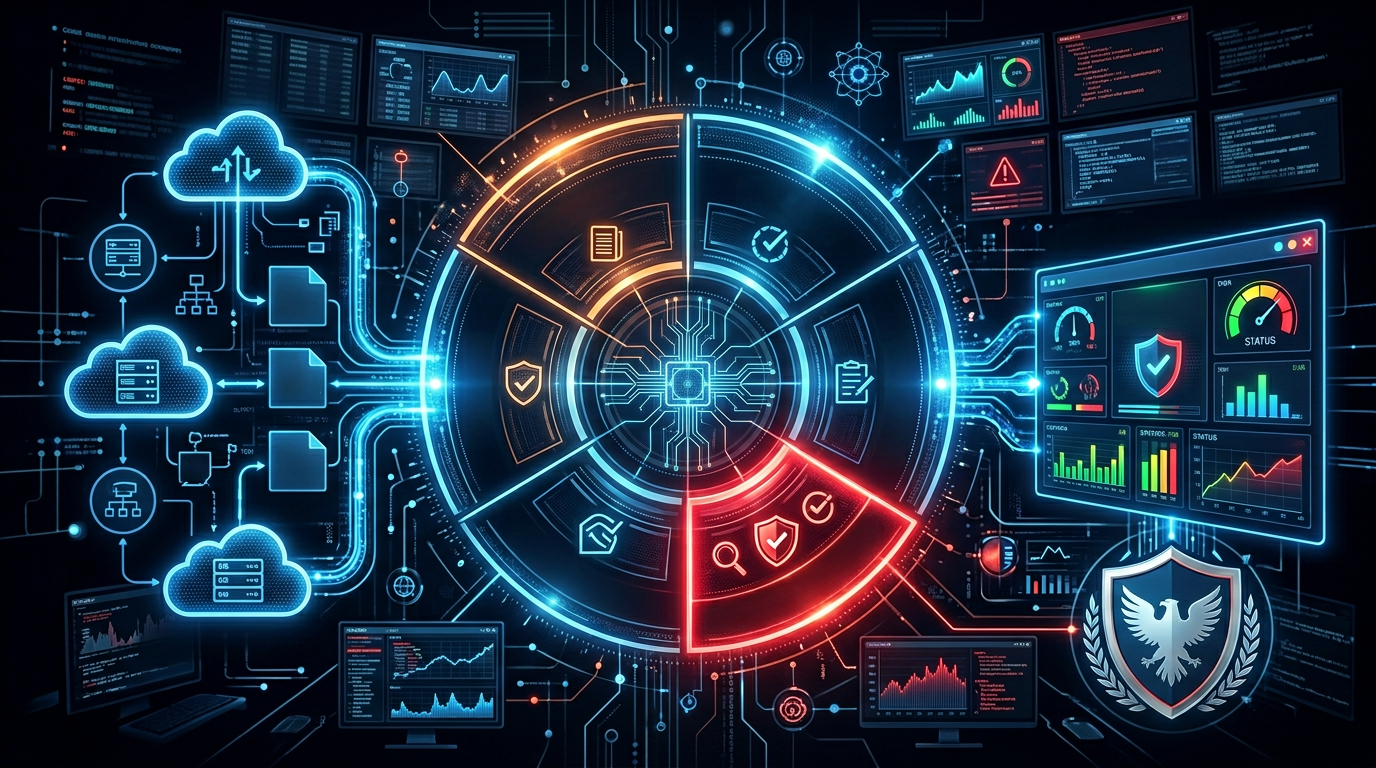
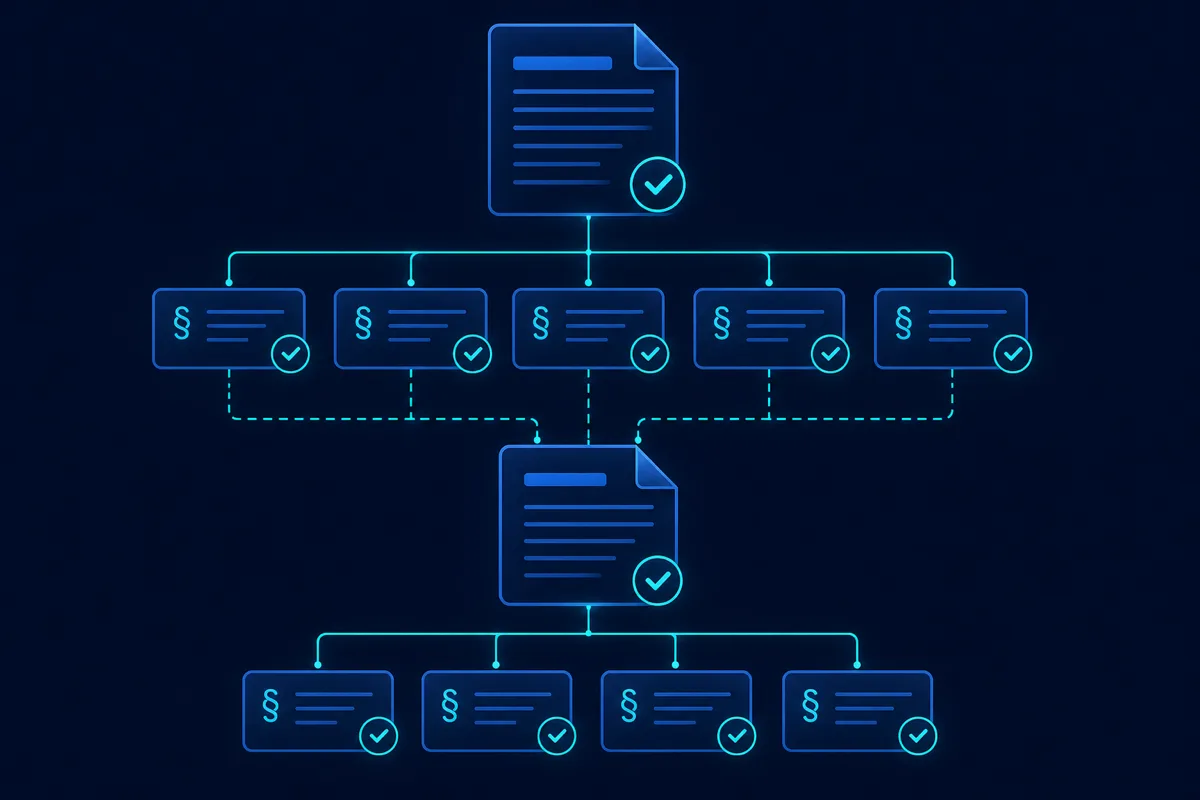
Automate NIST RMF Step 6 continuous monitoring — ConMon dashboards, automated evidence collection, POA&M management, and alerting that satisfies FISMA without manual spreadsheets.
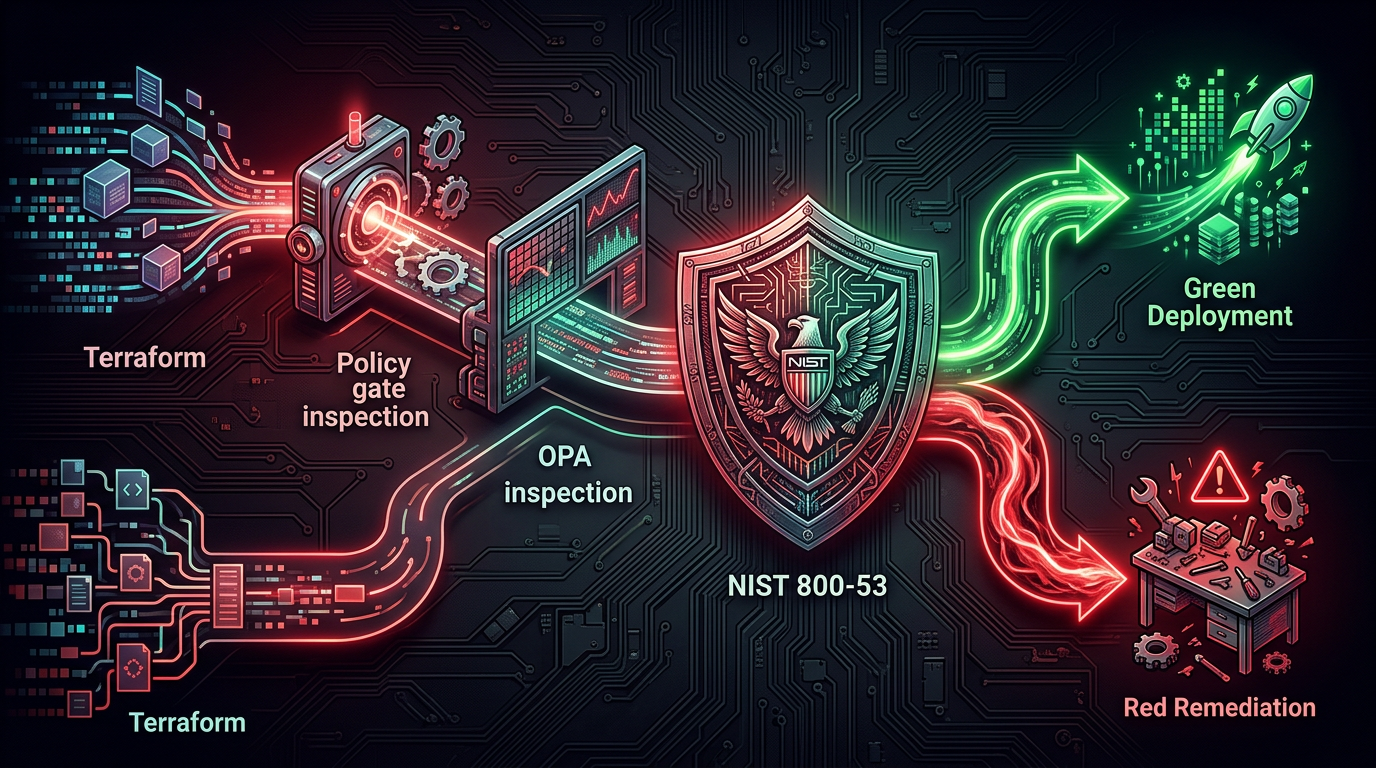
Pre-deploy compliance gates for federal IaC — Checkov, OPA Conftest, and custom NIST 800-53 policies that catch violations before they reach a GovCloud environment and block the ATO.

Architecture patterns for mission software in DDIL environments — offline-first design, store-and-forward data sync, edge-cloud reconciliation, and operational continuity when connectivity fails.

CUI cloud enclave on AWS GovCloud — marking, access enforcement, encryption, and the controls that satisfy NIST 800-171 and CMMC requirements.

Incident response for defense contractors — the 72-hour DFARS reporting window, detection pipelines, and infrastructure that satisfies DIBCAC audits.
IL4 and IL5 cloud architecture for DoD — impact level boundaries, GovCloud controls, isolation requirements, and what a compliant environment looks like.
STIG compliance automation in Kubernetes — pipeline integration, policy-as-code enforcement, and keeping DoD-regulated K8s clusters audit-ready.

FinOps for government cloud — cost visibility, Antideficiency Act compliance, rightsizing strategies, and keeping GovCloud spend auditable and optimized.
Platform One's Iron Bank for DoD-compliant container images — hardening standards, pipeline integration, and what DISA-approved base images require.

Space Force software contracts — what small businesses build, how cATO and DevSecOps fit acquisition, and what primes need from cloud-native subs.
Legacy defense system modernization — strangler-fig patterns, phased cloud migration, API wrapping, and delivering continuity without mission disruption.

Software architecture for polar ISR systems — edge computing in Arctic environments, pipeline design for high-latitude operations, and cloud integration patterns.

Automating System Security Plan generation — treating SSPs as living code artifacts, not stale Word documents, for NIST RMF and CMMC compliance.
Federal prime contractors must meet SBA small business subcontracting goals. Here's how a cloud-native sub like Rutagon satisfies those requirements.
What a CAGE code and SAM.gov registration mean for primes choosing a small business sub — and why Rutagon's March 2026 activation matters for teaming.
What primes get when they sub DevSecOps work to Rutagon: pipeline architecture, compliance automation, and delivery speed that reduces program risk.

Alaska Native Corporations win massive set-aside contracts and need qualified IT subs. Here's what primes and ANCs expect from a cloud engineering sub.
Federal primes choosing between a cloud-native subcontractor and staff augmentation face a capability and risk tradeoff. Here's how to evaluate the choice.
Defense primes building teams for Alaska-connected programs gain real proposal and delivery advantages from Alaska-based small business subcontractors.

Federal teaming agreements define how primes and subs split work and risk before award. Here's what they require and how Rutagon structures teaming deals.
Rutagon is an Alaska-based cloud engineering and DevSecOps subcontractor for federal primes. Active SAM.gov registration, CAGE 19ZR7, UEI FB2FHEJHM493.
Primes holding OASIS+ and CIO-SP4 task orders need cloud-native subs who are delivery-ready. Here's what those programs require and what Rutagon delivers.
Defense primes need NAICS 541512 small business cloud subs with SAM.gov registration. Here's what that NAICS code covers and why Rutagon qualifies.

DoD IL5 authorization demands US-person access controls, physical isolation, and DISA SRG compliance. Here's the reference architecture Rutagon delivers.
Continuous ATO eliminates authorization freezes by automating evidence collection and control validation. How Rutagon builds cATO-ready cloud pipelines.

Passing a C3PAO audit on first attempt requires the right cloud architecture from day one. How Rutagon engineers CMMC Level 2-compliant environments.
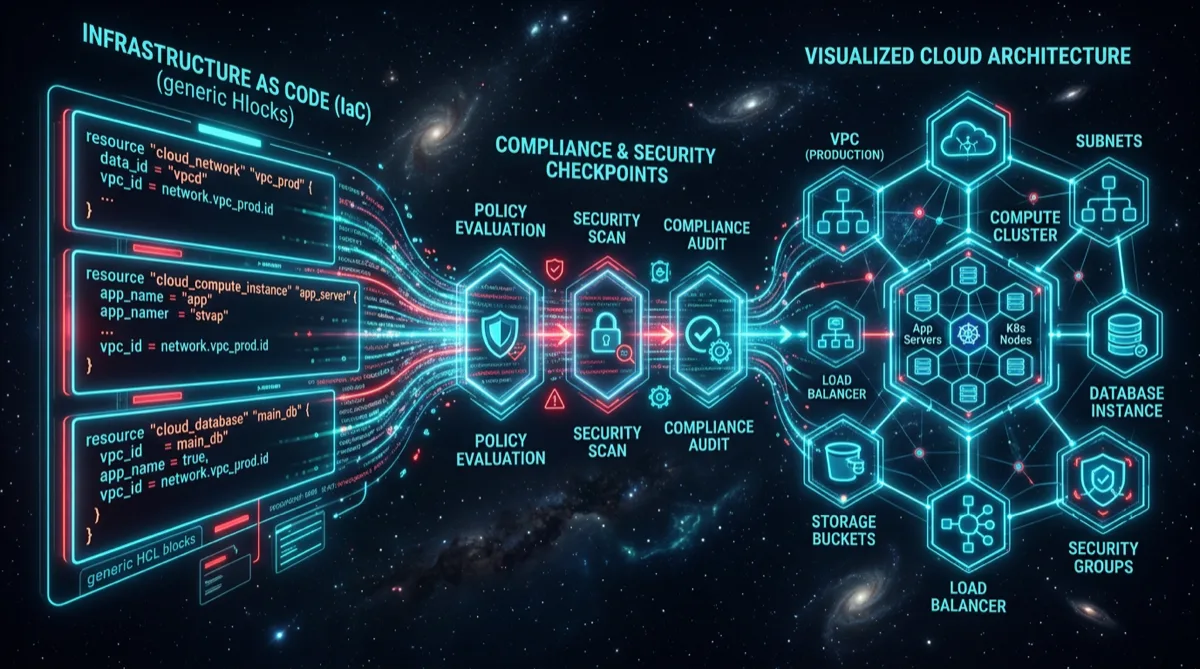
AWS GovCloud environments provisioned through Terraform IaC are reproducible, auditable, and compliant from day one. Rutagon's production approach.

The DoD 2027 zero trust mandate requires all 90 ZTA core activities to be implemented. How Rutagon architects compliant production systems.
DFARS 252.204-7012 requires CUI safeguarding and 72-hour cyber incident reporting. How Rutagon builds infrastructure that keeps contractors compliant.

A DoD software factory integrates hardened CI/CD, Iron Bank containers, and automated STIG scans. How Rutagon builds and operates software factories.

Legacy satellite command and control systems are brittle and expensive. How Rutagon re-architects monolithic C2 into containerized cloud-native systems.

Arctic military operations demand software that works disconnected and degraded. How Rutagon engineers resilient edge systems for austere environments.

Alaska is more than remote—it's strategic. Why an Alaska-based defense technology company like Rutagon has built-in advantages for DoD and Space Force.
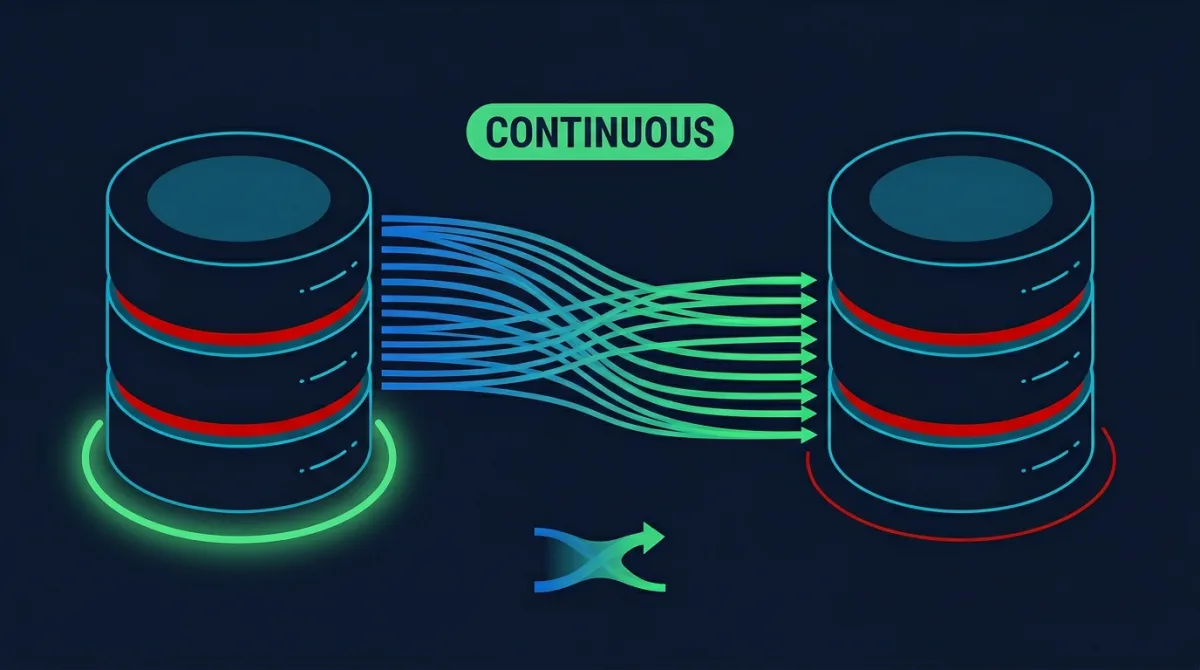
Proven zero-downtime database migration strategies for production systems including blue-green, rolling schema, and dual-write patterns for government and defense.
How small businesses deliver IDIQ task orders faster than large primes using cloud-native automation, pre-built infrastructure, and lean teams for government contracting.

How Rutagon automates satellite ground station operations with pass scheduling, telemetry routing, health monitoring, and anomaly detection for aerospace and defense.

How Rutagon architects secrets management in AWS production systems using rotation, cross-account access, and zero-credential deployment patterns for government and defense.
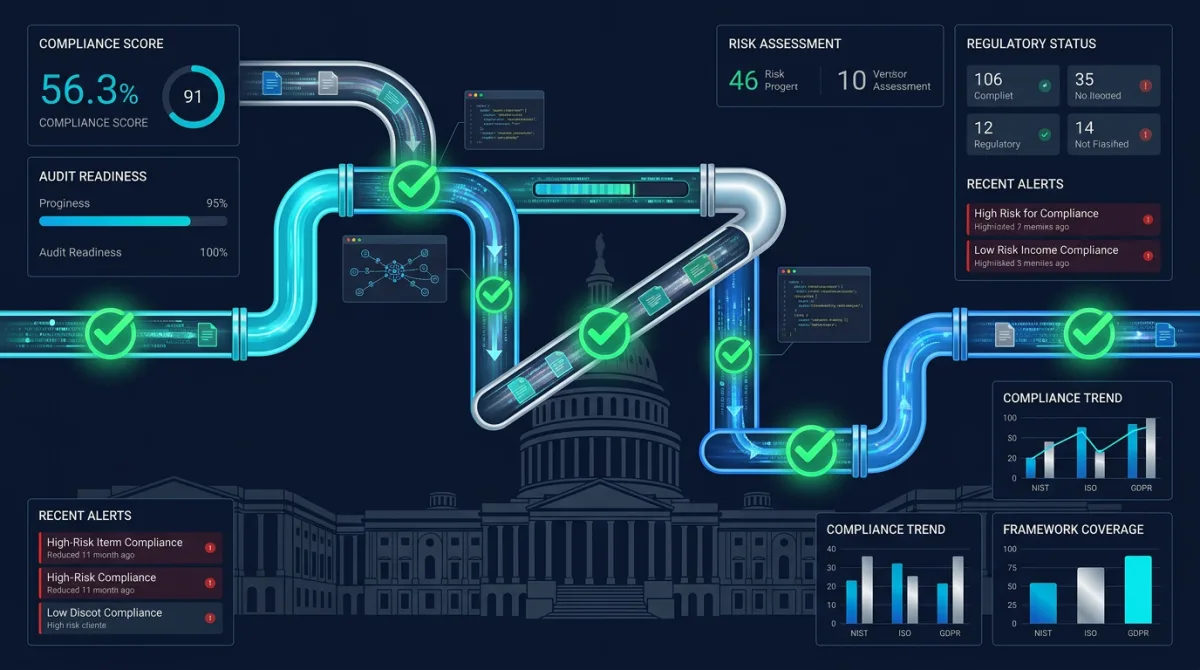
Automated compliance reporting architecture for government systems with continuous monitoring, evidence generation, and audit-ready dashboards for FISMA and FedRAMP.
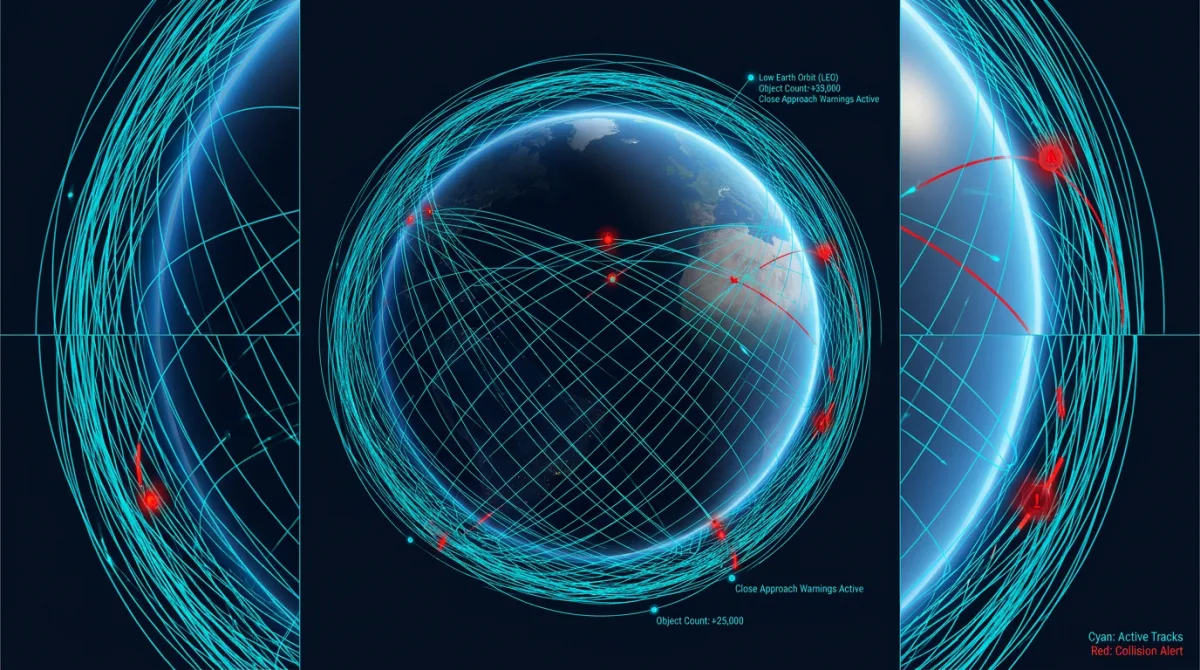
Software architecture for space situational awareness systems covering real-time object tracking, conjunction assessment, and orbital visualization.
WAF configuration patterns Rutagon deploys for government web applications covering rate limiting, bot protection, geo-blocking, and FISMA compliance for federal systems.

How Rutagon's Earn the Next Contract philosophy transforms every delivery into a proof point that drives repeat business and wins government IT contracts through exceptional past performance.

How Rutagon eliminates Lambda cold start latency in government applications using provisioned concurrency, SnapStart, and architecture patterns for defense and federal systems.

How Rutagon engineers the cloud security architecture that moves defense contractor SPRS scores from red to green before contract deadlines.
Rutagon automates CMMC evidence collection through CI/CD pipelines, generating compliance artifacts at every deployment instead of manual audit prep.
Replace long-lived AWS credentials with OIDC federation in CI/CD pipelines — eliminate stored secrets, reduce blast radius, and pass compliance audits.

Small businesses match prime contractor delivery speed with cloud-native automation, pre-built IaC modules, and DevSecOps pipelines for government work.

What prime contractors look for in small business cloud subcontractors — delivery speed, clearances, and risk reduction that earns repeat task orders.
Rutagon applies AI anomaly detection to space systems — real-time telemetry analysis, predictive alerts, and mission-critical reliability.
How Rutagon uses Aurora Serverless v2 for government workloads — scaling patterns, cost optimization, and compliance-ready architecture.

Serverless patterns that cut government system costs 60-80% — practical Lambda, DynamoDB, and API Gateway architecture for cost efficiency.

Implement CI/CD approval gates that satisfy government compliance without destroying deployment velocity — with GitHub Actions and GitLab CI samples.

Alaska military installations face unique cloud infrastructure challenges — extreme latency, harsh environments, and Arctic mission demands.

Rutagon ships working software, not slide decks. Here's what that delivery philosophy means for defense and government technology programs.
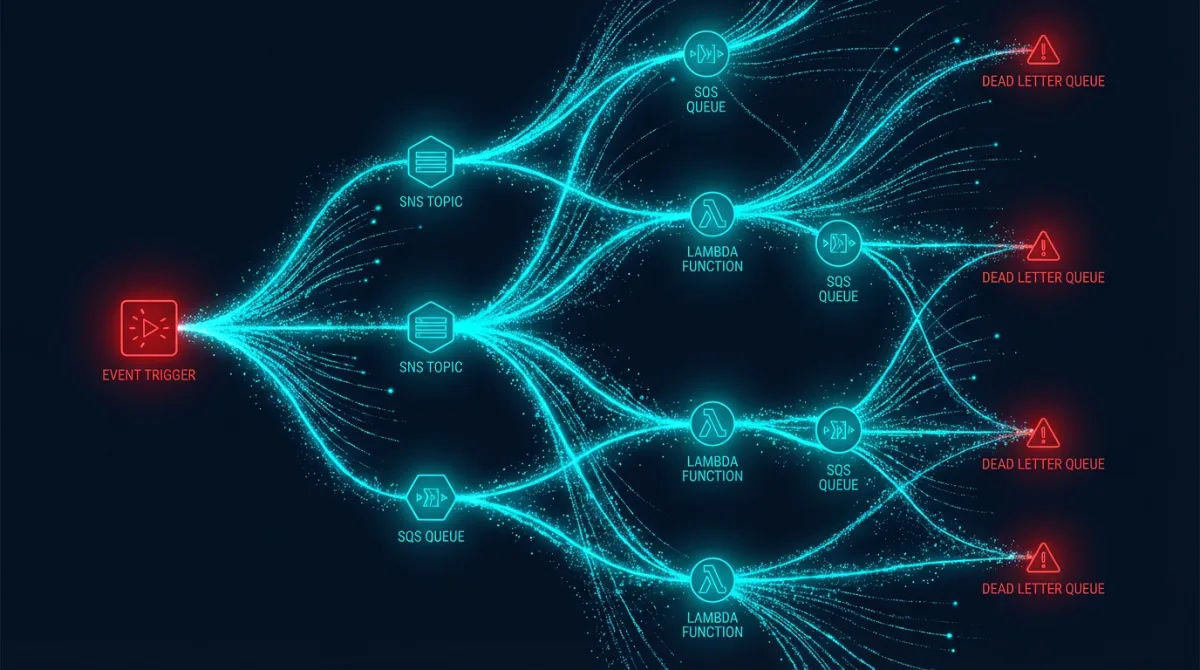
Event-driven architecture on AWS with SNS, SQS, EventBridge, and Lambda — retry logic, dead letter queues, and idempotency patterns.

NIST 800-171 cloud implementation patterns — mapping control families to AWS services, access control, audit logging, and monitoring.

Edge computing for defense and tactical systems — disconnected environments, containerized workloads, and data sync at the edge.

Why defense contractors need a fractional CTO — cloud modernization, compliance architecture, and competitive positioning on a budget.

Observability for regulated production systems — structured logging, distributed tracing, metrics, and compliance audit trails on AWS.
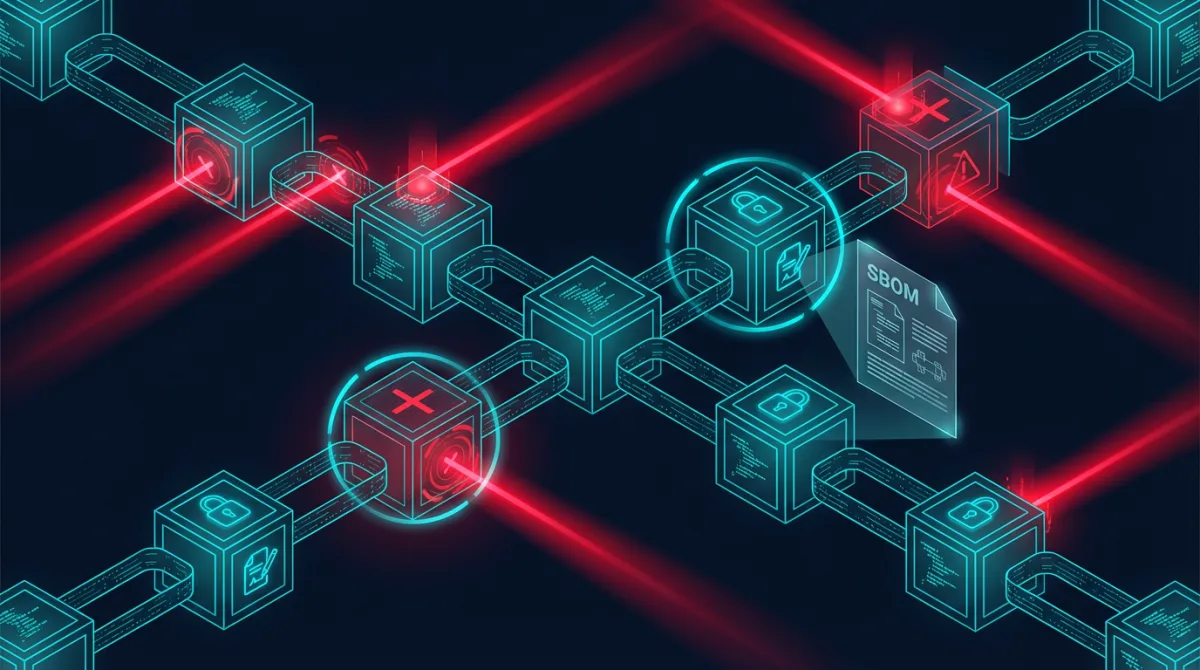
Software supply chain security for government — SBOM generation, dependency scanning, signed artifacts, SLSA compliance, and provenance.
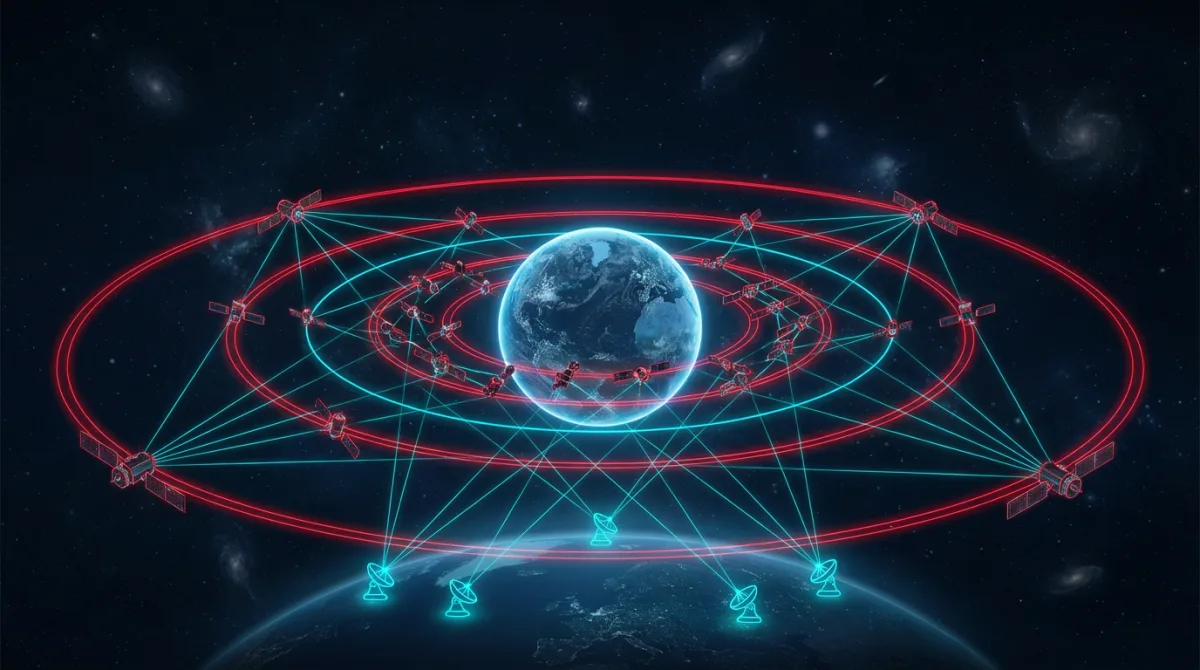
Software architecture for multi-orbit satellite constellations — LEO, MEO, GEO management, ground station handoff, and data routing.
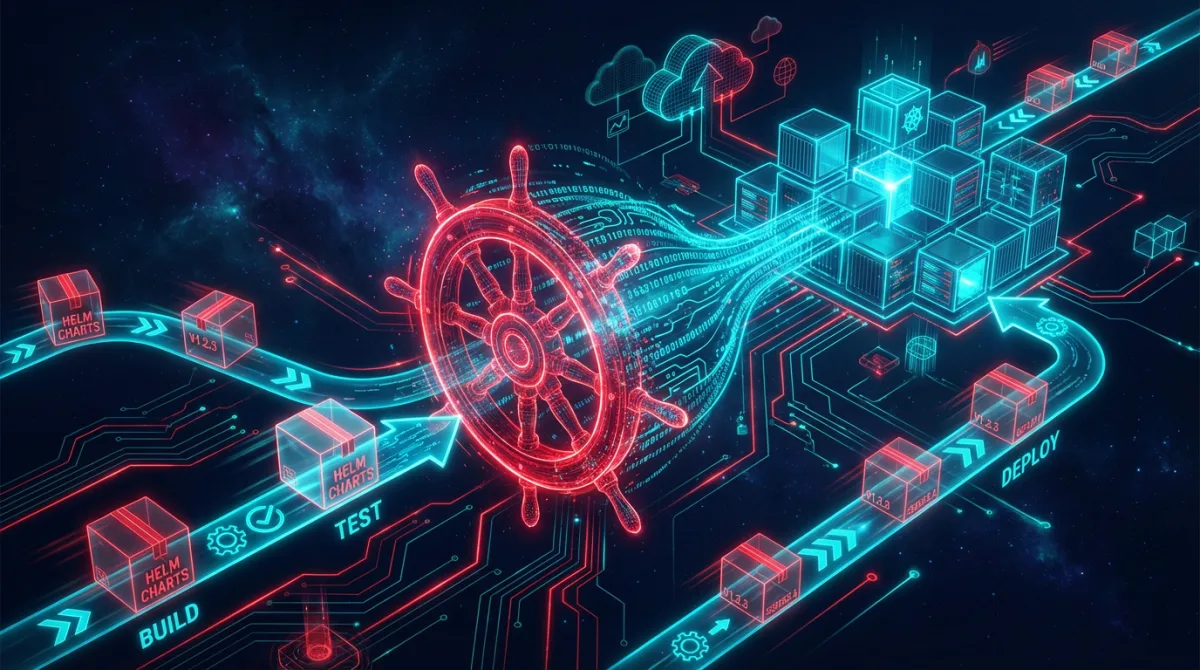
Production Helm charts for Kubernetes — chart structure, values templating, rollback strategies, secrets management, and chart testing.
API gateway patterns for microservices at scale — rate limiting, authentication, request transformation, caching, and API versioning.

The ATO process for cloud systems — RMF steps, continuous monitoring, documentation requirements, and accelerating Authority to Operate.
Production-tested container security CI/CD patterns: Trivy scanning, policy-as-code, signed images with Cosign, and CVE tracking automation in regulated pipelines.

How Rutagon designs FedRAMP cloud architecture with controls baked in: boundary definition, continuous monitoring, encryption, and audit logging from day one.
Architecture patterns for real-time dashboards on AWS using Kinesis, Glue, Athena, and QuickSight — production-tested for enterprise data pipelines.
How zero trust credentials architecture eliminates stored secrets, API keys, and long-lived tokens from production systems and CI/CD pipelines.
How federal website modernization replaces legacy systems with React, cloud-native architectures, 508 compliance, and sub-second performance at scale.
How custom software helps construction companies streamline operations with project dashboards, client portals, scheduling tools, and field management apps.
Professional web hosting vs DIY platforms: why serious businesses need managed hosting for security, performance, uptime, and SEO advantages.
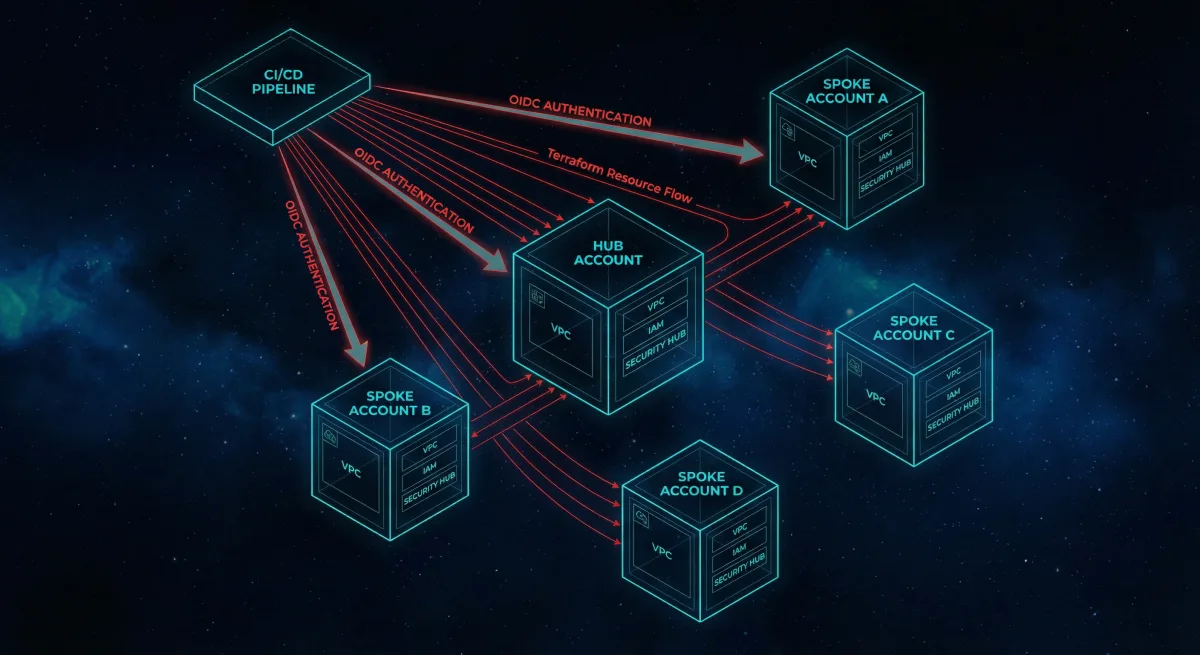
How to architect AWS multi-account environments with Terraform IaC — account segmentation, OIDC-based CI/CD, centralized security, and cost optimization.
Why defense contractors and small businesses need modern websites for GovWin visibility, prime teaming, capability demonstration, and CMMC compliance.

Software architecture for satellite ground systems: telemetry processing, command and control, data downlink management, and real-time monitoring dashboards.

Why Alaska is a strategic hub for space and defense technology — polar orbit access, military installations, Arctic domain awareness, and the growing defense tech ecosystem.
How Rutagon builds Section 508-compliant government websites with WCAG 2.1 AA standards — semantic HTML, ARIA patterns, keyboard navigation, and automated accessibility testing.

How Rutagon implements CMMC Level 2 security controls — access control, audit logging, configuration management, and incident response architecture for defense contracts.
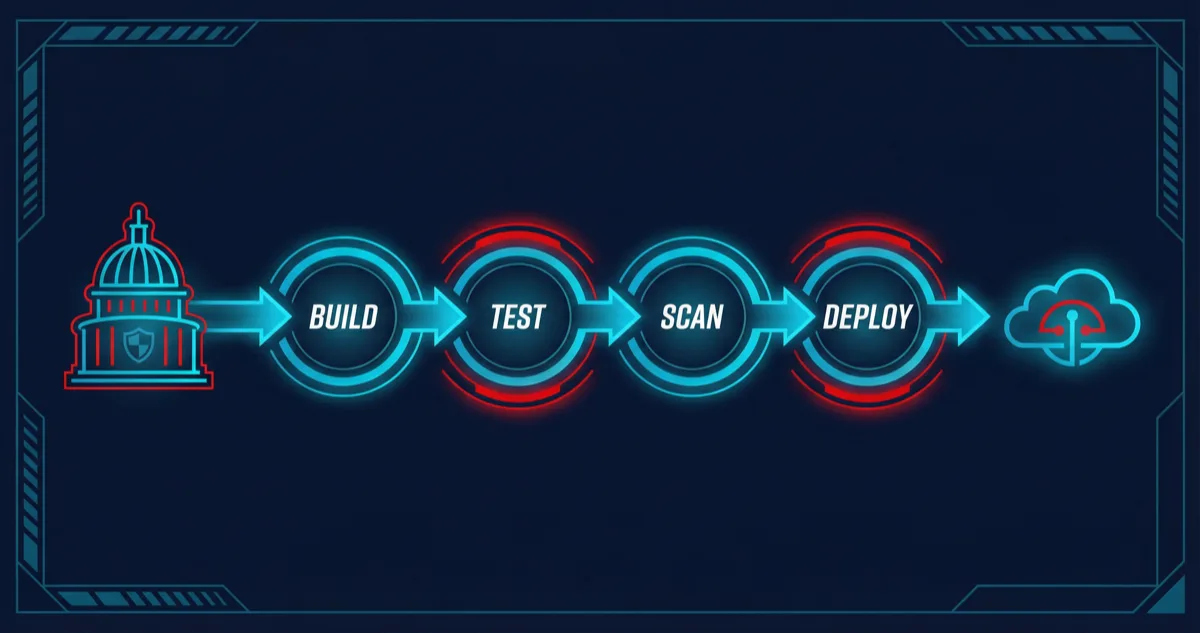
How Rutagon builds DevOps CI/CD pipelines for government systems — OIDC authentication, automated security scanning, approval gates, and artifact signing.
Production React TypeScript patterns — strict configs, component composition, custom hooks, error boundaries, and performance optimization.
How AI and machine learning process satellite imagery for space domain awareness — computer vision, change detection, real-time telemetry, and data pipeline architecture.
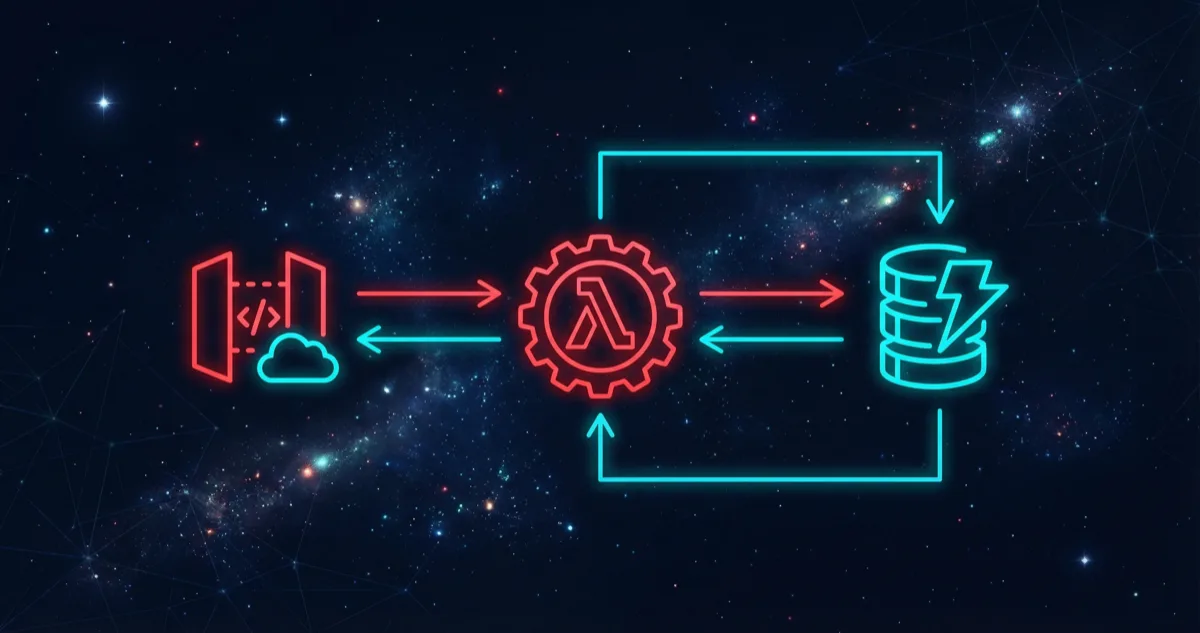
How Rutagon designs serverless APIs with AWS Lambda and DynamoDB — single-table design, function architecture, API Gateway patterns, and cost optimization.

Why federal agencies prefer small businesses for IT contracts — set-aside programs, agility advantages, and positioning as a small business prime.
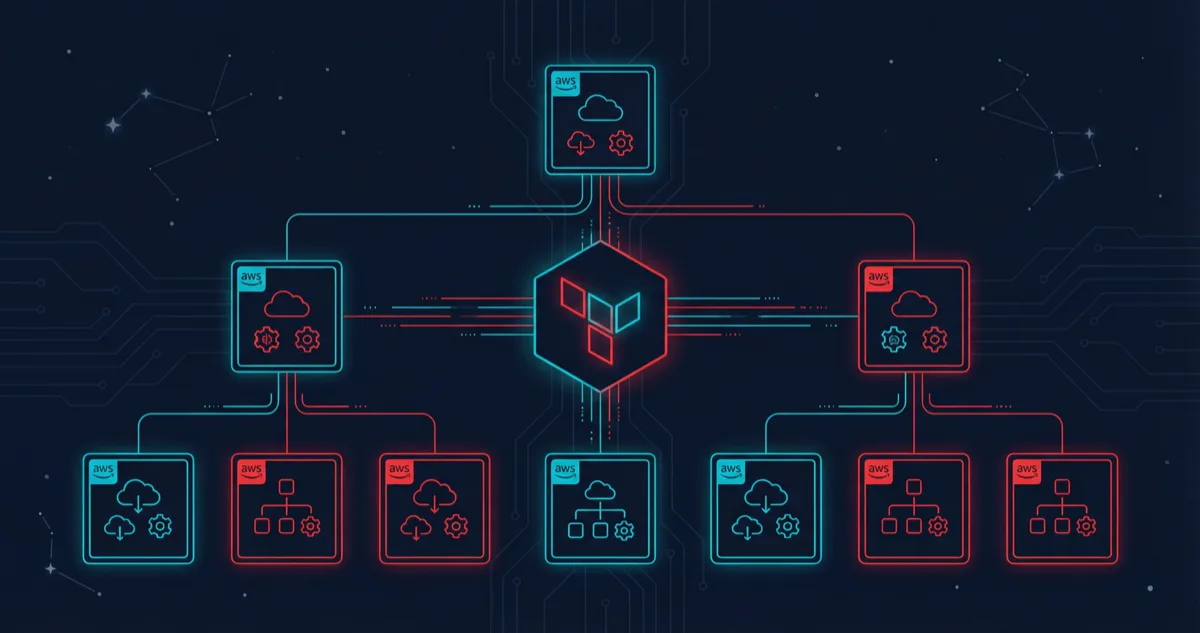
How Rutagon structures multi-account AWS Organizations with Terraform — account factory, shared networking, security baselines, and cross-account roles.

Rutagon's journey from commercial web development to defense contracting — building real products, earning revenue, and applying production engineering to government.

Architecture decisions, EKS vs. ECS vs. Lambda trade-offs, Terraform patterns, and CI/CD design for moving regulated workloads to AWS with zero downtime.

How to embed container scanning, CVE automation, identity management, and standardized logging directly into your deployment pipeline.

EKS architecture for compliance-sensitive workloads — network policies, pod security, image signing, Helm-based releases, and observability at scale.
Architecture patterns for mission-critical public-facing systems — CloudFront CDN, WAF, DDoS protection, multi-AZ failover, and performance at 10M+ monthly views.
We write about the problems we solve. If any of this resonates with your mission, let's discuss how Rutagon can help.
Initiate Contact