The traditional Authorization to Operate process is broken. A defense program completes an ATO package over 12–18 months, gets authorization, deploys into production — and then freezes. Any code change, infrastructure update, or new dependency requires navigating the authorization process again. Security stagnates while threat actors evolve.
Continuous ATO changes this model. Instead of a point-in-time authorization ceremony, cATO is an ongoing validation state where security controls are continuously monitored, evidence is continuously collected, and authorization stays current with the system.
Here's how Rutagon builds cATO-ready cloud systems for DoD and federal programs — and what it actually requires in infrastructure terms.
What Continuous ATO Actually Means
The DoD's cATO guidance defines Continuous ATO as the ability to:
- Deploy code changes without re-initiating the full ATO process, because security controls are continuously validated
- Maintain real-time compliance visibility through automated monitoring, not quarterly snapshots
- Integrate with a DoD-recognized DevSecOps platform (typically Platform One or a service-equivalent)
- Demonstrate continuous monitoring at the ISSM/ISSO level without manual evidence collection cycles
The goal is to keep authorization active across the system's full deployment lifecycle — not freeze it at an initial approval snapshot.
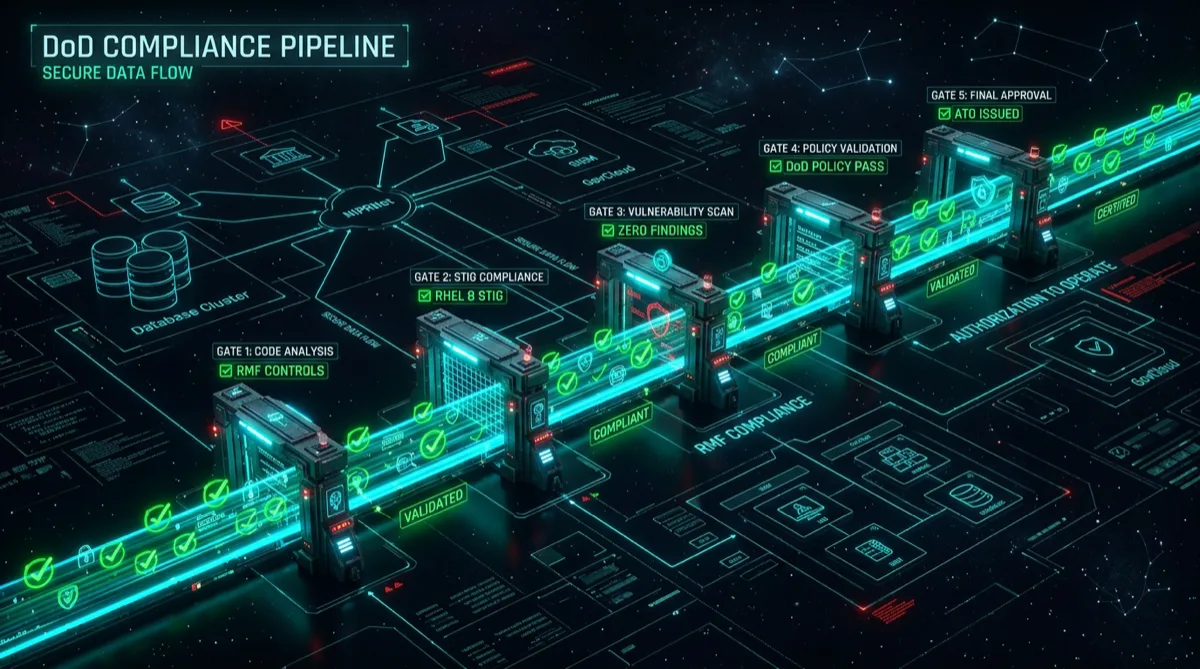
The Infrastructure Requirements for cATO
Achieving a defensible cATO posture requires specific infrastructure investments. This isn't a documentation exercise — it's an engineering outcome. Here are the components that matter:
1. Automated Security Control Testing in CI/CD
Every commit to the repository should trigger automated validation against the system's security controls. In a production Rutagon system, this pipeline includes:
# Example: Security gate in GitLab CI
security-scan:
stage: validate
image: aquasec/trivy:latest
script:
- trivy fs --exit-code 1 --severity HIGH,CRITICAL .
- trivy config --exit-code 1 --severity HIGH,CRITICAL ./terraform
rules:
- if: $CI_PIPELINE_SOURCE == "merge_request_event"
- if: $CI_COMMIT_BRANCH == "main"This blocks deployments that introduce HIGH or CRITICAL vulnerabilities — preventing control violations before they reach production and generating the evidence trail that cATO requires.
2. Policy-as-Code Enforcement
NIST 800-53 controls must translate into code. Policy-as-code tools like Open Policy Agent (OPA) and Checkov enforce infrastructure configurations against control baselines:
# Checkov check: Ensure S3 buckets have public access blocked (SC-7)
resource "aws_s3_bucket_public_access_block" "example" {
bucket = aws_s3_bucket.example.id
block_public_acls = true
block_public_policy = true
ignore_public_acls = true
restrict_public_buckets = true
}A Terraform plan that fails this check in the pipeline generates immediate evidence that the control violation was caught and remediated before deployment — exactly the kind of continuous monitoring evidence an ISSO needs.
3. Real-Time Compliance Dashboard
Static SSP documents are incompatible with cATO. Authorization officials need live visibility into control status. This means:
- AWS Security Hub (for FedRAMP/DoD workloads) aggregating findings from GuardDuty, Inspector, Config, and Macie
- Custom dashboards correlating control status against the RMF control baseline
- Automated findings routing to the responsible ISSO/system owner with remediation SLAs
In GovCloud environments, AWS Config Rules can be mapped directly to NIST 800-53 controls, providing real-time evidence collection that satisfies NIST SP 800-137 continuous monitoring requirements.
4. Zero-Drift Infrastructure
cATO requires that what's running in production matches what was authorized. Infrastructure drift — configuration changes made manually, outside the IaC pipeline — breaks the authorization model.
The solution: GitOps with mandatory drift detection. Every infrastructure change must flow through the Terraform pipeline. Drift detection runs on a schedule (every 4–6 hours in production environments) and alerts on any deviation from the IaC-defined state.
See our full discussion of eliminating secrets and credentials in AWS for the zero-credentials component that makes GitOps-enforced pipelines fully automated.
5. Automated Evidence Collection
The SSP and continuous monitoring report can't require an ISSO to manually gather screenshots. In a cATO system, evidence is generated and stored automatically:
- Configuration state snapshots from AWS Config
- Vulnerability scan results from Inspector and Trivy (stored as artifacts in the pipeline)
- Access logs from CloudTrail, aggregated and queryable
- Automated Plan of Action and Milestones (POA&M) generation from Security Hub findings
When an authorization official asks for evidence that AC-2 (Account Management) is being enforced, the response is a programmatic query against the log archive — not a manual audit.
Integration With Platform One
DoD's Platform One is the reference DevSecOps platform for defense software. Systems operating on Platform One's Big Bang baseline inherit significant cATO-relevant infrastructure: Iron Bank-hardened containers, Istio service mesh, automated STIG compliance scanning, and integration with cATO-supporting tools.
For programs not on Platform One, building a Platform One-equivalent capability requires:
- Iron Bank-compatible container hardening (DISA STIG-compliant base images)
- CI/CD integration with DoD-approved security scan tooling
- Documentation mapping the custom pipeline to Platform One equivalencies
Rutagon builds this capability for programs operating outside the Platform One umbrella — either on Commercial Cloud with DoD-approved controls, or on GovCloud environments requiring full program-level security architecture.
What cATO Enables for Program Teams
The operational payoff of continuous ATO is significant:
- Sprint-velocity deployments: Program teams can ship features at commercial velocity without authorization gate interruptions
- Rapid vulnerability patching: When a new CVE drops (Log4Shell, for example), a cATO-enabled program can patch, test, and redeploy within hours rather than waiting for re-authorization
- Live security posture: Program leadership has real-time visibility into compliance status — not a quarterly ISSO report
This is the delivery model defense software programs need to keep pace with adversary capability development.
View Rutagon's security automation capabilities →
Also see our related work on the ATO process for cloud systems and security compliance in CI/CD for related architectural patterns.
Frequently Asked Questions
What is Continuous ATO (cATO) in the DoD context?
Continuous ATO (cATO) is a DoD authorization framework that maintains active system authorization through ongoing automated security monitoring and evidence collection, rather than point-in-time authorization ceremonies. A cATO-authorized system can deploy code changes without re-initiating the full ATO process, because security controls are continuously validated and authorization remains current with the live system state.
What infrastructure is required to achieve cATO?
The core infrastructure requirements for cATO include: automated security control testing in CI/CD pipelines (SAST, container scanning, IaC compliance gates), policy-as-code enforcement (OPA, Checkov, or equivalent), real-time compliance dashboards integrated with SIEM/SOAR tooling, zero-drift infrastructure enforced through GitOps pipelines, and automated evidence collection covering all NIST 800-53 controls in the system's authorization baseline.
How does Platform One support cATO?
DoD's Platform One provides a hardened DevSecOps environment with built-in cATO-supporting capabilities: Iron Bank container images that meet DISA STIG requirements, integrated CI/CD pipelines with security scan tooling, Istio service mesh for mTLS and traffic policy, and documentation supporting authorization claims. Programs deployed on Platform One's Big Bang baseline inherit significant compliance posture, but cATO still requires program-specific control implementation and continuous monitoring.
How does cATO differ from a traditional ATO?
A traditional ATO is a point-in-time authorization: the system is assessed, documentation is reviewed, and authorization is granted for a specific system state. Changes require re-authorization. A cATO is a persistent authorization state maintained by continuous automated monitoring. The system can evolve — new features, security patches, infrastructure updates — without triggering a full re-authorization cycle, because compliance is continuously validated rather than periodically assessed.
What does Rutagon deliver for programs pursuing cATO?
Rutagon builds the engineering infrastructure that makes cATO achievable: CI/CD pipelines with automated security gates, policy-as-code frameworks mapped to the program's NIST 800-53 baseline, real-time compliance dashboards in GovCloud or commercial cloud environments, GitOps-enforced infrastructure with drift detection, and automated evidence collection that satisfies continuous monitoring requirements. Contact Rutagon to discuss your program's cATO requirements.