Most defense contractors treat CMMC evidence collection as a separate workstream — a painful, manual scramble that kicks off months before an assessment. Compliance teams chase down screenshots, export logs, compile spreadsheets, and pray nothing changed since the last time they gathered artifacts.
We decided that was unacceptable. At Rutagon, CMMC evidence is a byproduct of how we deploy software, not a project we spin up when auditors come knocking.
The Problem with Manual Evidence Collection
CMMC Level 2 requires demonstrating compliance across 110 practices derived from NIST 800-171. Each practice demands evidence — not just a policy document claiming you do something, but proof that controls are operational and consistently enforced.
For most organizations, this means:
- Dedicating personnel to screenshot access control configurations
- Manually exporting vulnerability scan results and mapping them to controls
- Compiling configuration baselines from multiple systems into a single package
- Reconstructing audit trails after the fact, hoping nothing was overwritten
The result is weeks or months of preparation, significant cost, and evidence that’s already stale by the time it reaches an assessor. Worse, it creates a perverse incentive to “freeze” systems before an audit rather than continuously improving them.
We built our pipeline to eliminate every one of these problems.
Evidence as a Deployment Artifact
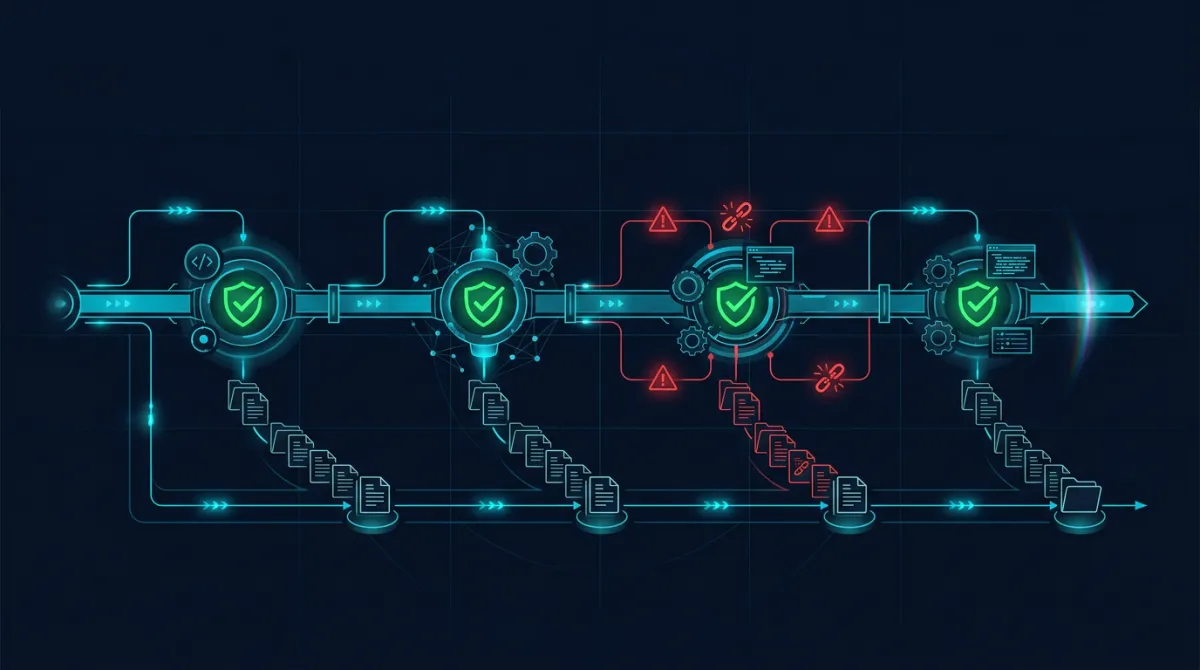
Every deployment through our CI/CD pipeline produces compliance artifacts automatically. When code moves through our pipeline, the system generates and archives evidence tied to specific CMMC practices — without any human intervention.
Here’s what that looks like at a high level:
Access Control Evidence (AC family): Every deployment records who initiated it, what credentials were used, and what approval gates were passed. Role-based access is enforced programmatically — the pipeline won’t execute without proper authorization, and every authorization event is logged with immutable timestamps. This directly addresses practices like AC.L2-3.1.1 (authorized access enforcement) and AC.L2-3.1.2 (transaction and function control).
Audit and Accountability (AU family): Our pipeline generates comprehensive audit records at every stage. Build logs, test results, deployment approvals, and infrastructure changes are captured with who, what, when, and where metadata. These logs feed into centralized, tamper-evident storage. We don’t reconstruct audit trails — they exist because the system creates them as it operates.
Configuration Management (CM family): Every deployment captures the full configuration baseline — infrastructure-as-code state, dependency versions, environment variables (encrypted), and system parameters. Configuration drift detection runs automatically, flagging any deviation from the approved baseline. The pipeline itself enforces CI/CD approval gates that prevent unauthorized configuration changes from reaching production.
Risk Assessment (RA family): Vulnerability scans execute as pipeline stages, not as separate scheduled activities. Static analysis, dependency vulnerability checks, and infrastructure security scanning all produce structured reports that map directly to CMMC practice requirements. These aren’t one-off scans — they run on every single deployment.
System and Communications Protection (SC family): Encryption configurations, network segmentation rules, and data-in-transit protections are validated programmatically during deployment. The pipeline verifies that security compliance requirements are met before any change reaches a protected environment.
Architecture Decisions That Make This Work
We made several deliberate architectural choices to enable continuous evidence generation:
Immutable infrastructure: We don’t patch servers in place. Every deployment creates new infrastructure from a known-good baseline. This means configuration evidence is always current and accurate — there’s no gap between “what we documented” and “what’s actually running.”
Infrastructure as code with compliance annotations: Our Terraform and deployment configurations include metadata that maps infrastructure components to specific CMMC practices. When the pipeline provisions resources, it simultaneously generates evidence that those resources meet their corresponding control requirements.
Centralized, append-only log architecture: All evidence flows into storage designed for regulatory retention. Logs cannot be modified or deleted within the retention window. This satisfies both the CMMC audit requirements and the evidentiary standards that assessors expect.
Automated control validation: Rather than relying on periodic manual checks, we run automated validation tests that confirm controls are functioning. These aren’t unit tests for application code — they’re compliance assertions that verify security controls are active and properly configured.
Our broader CMMC compliance approach informed these decisions. Each choice reduces human involvement in evidence generation while increasing the reliability and completeness of the artifacts produced.
What This Delivers in Practice
The results speak for themselves:
Assessment readiness on demand. When an assessor requests evidence for any CMMC practice, we generate a current evidence package in minutes, not weeks. The artifacts are timestamped, complete, and directly mapped to the practice being assessed.
Compressed ATO timelines. Organizations we work with have seen their Authority to Operate timelines shrink dramatically. When evidence is already organized, current, and comprehensive, the assessment process accelerates. Assessors spend their time validating controls rather than waiting for evidence compilation.
Zero manual evidence gathering. No one on our team spends time taking screenshots, exporting logs, or building compliance spreadsheets. The pipeline handles it. This frees security personnel to focus on actual security improvements rather than documentation busywork.
Continuous compliance posture. Because evidence is generated with every deployment, our compliance posture is always current. There’s no “audit preparation” period where teams scramble to bring documentation up to date. The documentation is up to date, always, because it’s produced by the same process that deploys the software.
Reduced human error. Manual evidence collection is error-prone. People miss controls, capture the wrong screenshots, or document configurations that have since changed. Automated collection eliminates these failure modes entirely.
How This Connects to NIST 800-171
CMMC Level 2 is built on NIST 800-171, and our evidence generation maps directly to the 800-171 control families. Every artifact our pipeline produces includes metadata identifying which 800-171 controls it satisfies. This traceability is critical — assessors can follow a direct line from a specific control requirement to the evidence demonstrating compliance.
This isn’t a bolted-on mapping exercise. The relationship between pipeline stages and control families was designed into the system from the beginning. When we add a new deployment stage, we simultaneously define what compliance evidence it produces and which controls it satisfies.
Why This Matters for Defense Contractors
The defense industrial base is under increasing pressure to demonstrate genuine cybersecurity maturity. CMMC isn’t going away — it’s expanding. Organizations that rely on manual compliance processes will face mounting costs, longer assessment cycles, and greater risk of findings.
Automated evidence collection isn’t just an efficiency play. It’s a fundamentally different compliance posture. Instead of proving you were compliant at a point in time, you demonstrate that compliance is an inherent property of how you build and deploy software.
That’s the standard we hold ourselves to at Rutagon, and it’s what we bring to every cybersecurity engagement we take on.
Frequently Asked Questions
How does automated evidence collection handle CMMC practice areas that aren’t technical?
CMMC includes practices around personnel security, physical protection, and awareness training that aren’t tied to CI/CD pipelines. Our automated collection covers the technical control families — access control, audit, configuration management, risk assessment, and system protection. For non-technical practices, we maintain separate documentation processes, but the technical evidence (which represents the majority of assessment effort) is fully automated.
Can automated evidence satisfy a C3PAO assessment, or do assessors require manually compiled packages?
C3PAO assessors evaluate evidence based on completeness, accuracy, and relevance — not based on how it was generated. Our automated artifacts include the same information (timestamps, responsible parties, control mappings, system states) that a manually compiled package would contain. Several assessment frameworks explicitly encourage automated evidence generation as a sign of mature security practices.
What happens if a deployment fails a compliance check — does it still generate evidence?
Yes, and this is important. Failed compliance checks generate evidence of the failure and evidence that the pipeline prevented the non-compliant change from reaching production. This actually strengthens the compliance narrative — it demonstrates that controls are not only monitored but actively enforced. Assessors view enforcement evidence favorably.
How frequently is evidence generated, and how long is it retained?
Evidence is generated with every deployment and every automated compliance scan. For active projects, this can mean multiple evidence packages per day. Retention follows federal records management requirements — we maintain evidence for the full retention period required by the contract and applicable regulations, stored in immutable, append-only archives.
Does this approach work for organizations at CMMC Level 1, or is it only relevant for Level 2?
The architecture supports both levels. Level 1 requires demonstrating basic cyber hygiene across 17 practices, all of which fall within the technical control families our pipeline covers. The same automated evidence generation applies — it’s just a subset of the full Level 2 evidence package. Organizations starting at Level 1 benefit from building automated collection early, as it provides a foundation for Level 2 readiness.
Discuss your project with Rutagon
Contact Us →