Cloud Security Posture Management (CSPM) answers a question that every federal ATO program struggles with: "Is our cloud environment still compliant right now, or just at the point of last assessment?" Static point-in-time assessments miss configuration drift — the team that deployed the ATO-compliant environment is the same team that opens a security group at 11pm to debug an issue and forgets to close it.
Rutagon implements CSPM as continuous, automated evidence generation — not a quarterly scan. Here's the architecture.
CSPM in Federal Context
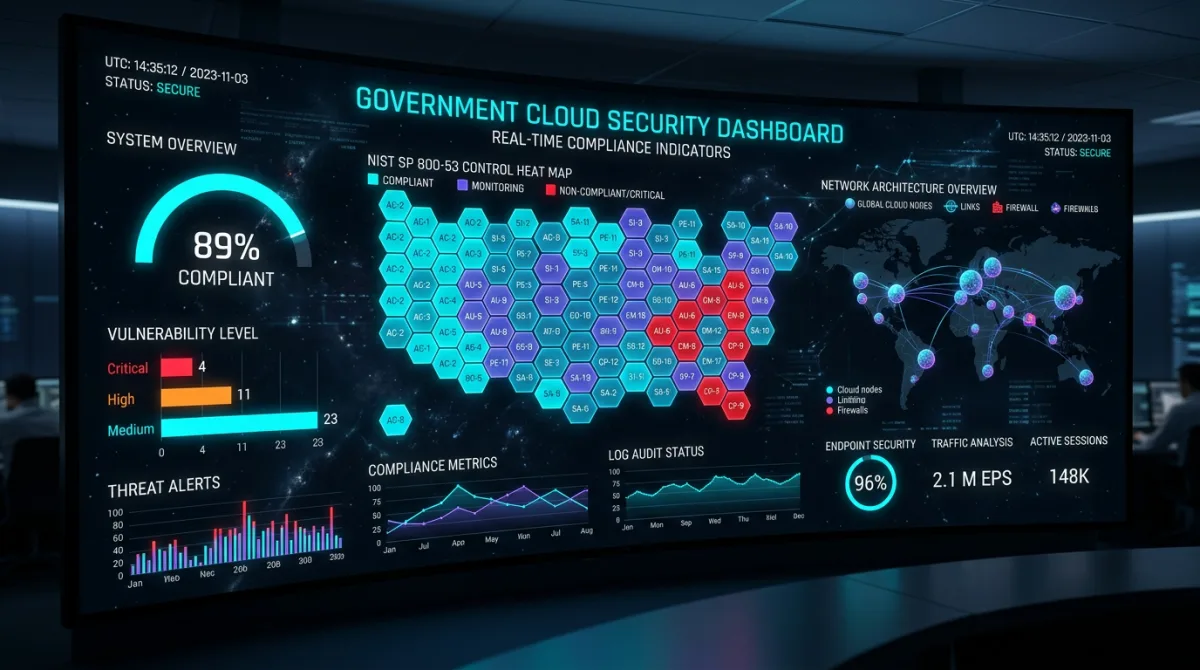
NIST RMF Step 6 — Monitoring — requires continuous monitoring of security controls. NIST SP 800-137 defines the ISCM strategy: "Ongoing awareness of information security, vulnerabilities, and threats to support organizational risk management decisions."
CSPM operationalizes this. The tools: AWS Config for infrastructure state tracking, AWS Security Hub for aggregated findings, Amazon GuardDuty for threat detection, and AWS Trusted Advisor for service-limit and security best practice checks.
AWS Config: The Foundation of Infrastructure ConMon
AWS Config records every configuration change to every tracked resource. For GovCloud, enable Config in every account and region:
resource "aws_config_configuration_recorder" "main" {
name = "govcloud-config-recorder"
role_arn = aws_iam_role.config_role.arn
recording_group {
all_supported = true
include_global_resource_types = true
}
}
resource "aws_config_delivery_channel" "main" {
name = "govcloud-config-delivery"
s3_bucket_name = aws_s3_bucket.config_bucket.bucket
sns_topic_arn = aws_sns_topic.config_notifications.arn
depends_on = [aws_config_configuration_recorder.main]
}
resource "aws_config_configuration_recorder_status" "main" {
name = aws_config_configuration_recorder.main.name
is_enabled = true
depends_on = [aws_config_delivery_channel.main]
}NIST 800-53 Config Rules
AWS provides a managed conformance pack that maps Config rules to NIST 800-53 Rev 5 controls. Deploy it:
resource "aws_config_conformance_pack" "nist_800_53" {
name = "NIST-800-53-Rev5"
template_body = <<EOF
Parameters:
AccessKeysRotatedParamMaxAccessKeyAge:
Default: "90"
...
EOF
}Custom Config rules for government-specific requirements:
# Lambda backing a custom Config rule: detect unencrypted S3 buckets without CMK
def evaluate_compliance(configuration_item, rule_parameters):
if configuration_item['resourceType'] != 'AWS::S3::Bucket':
return 'NOT_APPLICABLE'
bucket_config = configuration_item['configuration']
server_side_encryption = bucket_config.get('serverSideEncryptionConfiguration', {})
if not server_side_encryption:
return 'NON_COMPLIANT'
for rule in server_side_encryption.get('rules', []):
apply_rule = rule.get('applyServerSideEncryptionByDefault', {})
if apply_rule.get('sseAlgorithm') == 'aws:kms':
kms_key = apply_rule.get('kmsMasterKeyID', '')
if 'mrk-' in kms_key or 'alias/aws/' not in kms_key:
return 'COMPLIANT' # CMK is used
return 'NON_COMPLIANT' # No CMK encryptionConfig rules generate findings automatically on every resource change — before any human reviews the change.
AWS Security Hub: Aggregated Finding Dashboard
Security Hub ingests findings from Config, GuardDuty, Macie, Inspector, and third-party tools into a single normalized finding format. Configure Security Hub with the NIST 800-53 standard:
resource "aws_securityhub_account" "main" {}
resource "aws_securityhub_standards_subscription" "nist_800_53" {
standards_arn = "arn:aws-us-gov:securityhub:us-gov-west-1::standards/nist-800-53/v/5.0.0"
depends_on = [aws_securityhub_account.main]
}
# Also enable CIS AWS Foundations Benchmark
resource "aws_securityhub_standards_subscription" "cis" {
standards_arn = "arn:aws-us-gov:securityhub:us-gov-west-1::standards/cis-aws-foundations-benchmark/v/1.4.0"
depends_on = [aws_securityhub_account.main]
}Security Hub provides a compliance score per control family — your ATO package should include this score as evidence of ongoing compliance posture. Automate Security Hub finding export to your ConMon reporting infrastructure:
import boto3
from datetime import datetime, timedelta
def export_security_hub_findings_for_conmon():
sh_client = boto3.client('securityhub', region_name='us-gov-west-1')
# Get critical and high findings from last 30 days
response = sh_client.get_findings(
Filters={
'SeverityLabel': [
{'Value': 'CRITICAL', 'Comparison': 'EQUALS'},
{'Value': 'HIGH', 'Comparison': 'EQUALS'}
],
'RecordState': [{'Value': 'ACTIVE', 'Comparison': 'EQUALS'}],
'WorkflowStatus': [{'Value': 'NEW', 'Comparison': 'EQUALS'}]
},
SortCriteria=[{'Field': 'SeverityLabel', 'SortOrder': 'asc'}],
MaxResults=100
)
findings = response['Findings']
# Export to ConMon tracking system
return findingsGuardDuty: Threat Detection for SI-4
GuardDuty performs intelligent threat detection using ML and threat intelligence — detecting compromised credentials, cryptocurrency mining, unusual API calls, and port scanning without any agents to manage.
resource "aws_guardduty_detector" "main" {
enable = true
finding_publishing_frequency = "ONE_HOUR"
datasources {
s3_logs {
enable = true
}
kubernetes {
audit_logs {
enable = true
}
}
malware_protection {
scan_ec2_instance_with_findings {
ebs_volumes {
enable = true
}
}
}
}
}GuardDuty findings flow into Security Hub automatically. Configure EventBridge rules to route CRITICAL GuardDuty findings to your incident response workflow:
resource "aws_cloudwatch_event_rule" "guardduty_critical" {
name = "guardduty-critical-findings"
description = "Route critical GuardDuty findings to incident response"
event_pattern = jsonencode({
source = ["aws.guardduty"]
detail-type = ["GuardDuty Finding"]
detail = {
severity = [{ numeric = [">=", 7.0] }]
}
})
}
resource "aws_cloudwatch_event_target" "incident_response_sns" {
rule = aws_cloudwatch_event_rule.guardduty_critical.name
arn = aws_sns_topic.incident_response.arn
}This implements IR-6 (Incident Reporting) and SI-4 (System Monitoring) automated alerting requirements from NIST 800-53.
Automated ConMon Reporting
The CSPM data is only useful if it flows into continuous monitoring reports that satisfy the ATO sponsor. Automate monthly ConMon report generation:
def generate_conmon_report(month: str) -> dict:
config_client = boto3.client('config', region_name='us-gov-west-1')
sh_client = boto3.client('securityhub', region_name='us-gov-west-1')
# Get compliance summary from Config
compliance_summary = config_client.get_compliance_summary_by_config_rule()
# Get Security Hub score per control family
control_summary = sh_client.describe_standards_controls(
StandardsSubscriptionArn='arn:aws-us-gov:securityhub:...'
)
return {
'report_date': month,
'config_compliant_rules': compliance_summary['ComplianceSummary']['CompliantResourceCount'],
'config_noncompliant_rules': compliance_summary['ComplianceSummary']['NonCompliantResourceCount'],
'security_hub_score': calculate_sh_score(control_summary),
'open_critical_findings': get_open_critical_count(sh_client),
'open_high_findings': get_open_high_count(sh_client)
}This report structure maps directly to the continuous monitoring deliverables required by most ATO packages — providing automated evidence rather than manually compiled spreadsheets.
Integration with the ATO Lifecycle
CSPM data serves multiple ATO lifecycle stages:
- Initial authorization: Baseline Config rule compliance as evidence of Day 1 posture
- Annual assessment: Security Hub compliance scores demonstrate sustained posture
- Continuous ATO (cATO): CSPM is the real-time evidence that justifies removing periodic assessment requirements — see our continuous ATO automation architecture
- POA&M management: Config findings feed directly into POA&M items; Security Hub tracks remediation via workflow status
Related: DISA STIG cloud deployment patterns and NIST RMF continuous monitoring implementation.
Rutagon designs and implements CSPM architectures in production federal cloud environments. Contact Rutagon to build continuous monitoring capability for your federal program.
Frequently Asked Questions
What's the difference between CSPM and SIEM for government cloud?
CSPM (AWS Config, Security Hub) monitors cloud infrastructure configuration state — "is this S3 bucket encrypted?" "is this security group overly permissive?" SIEM (Splunk, Elastic, CloudWatch Logs) aggregates log data for threat hunting and incident investigation. Government programs need both: CSPM for configuration compliance (NIST RMF Step 6), SIEM for event-based threat detection and audit log analysis (AU-2, AU-6). The two feed each other — CSPM findings may trigger SIEM investigations.
How does CSPM satisfy FedRAMP continuous monitoring requirements?
FedRAMP requires monthly vulnerability scanning, annual penetration testing, and ongoing inventory tracking. CSPM tools satisfy the inventory tracking (Config) and configuration compliance monitoring components. Security Hub's compliance scores map to FedRAMP control families. The FedRAMP ConMon requirements specifically list Configuration Management as a monthly deliverable — automated Config rule compliance reports satisfy this requirement.
What happens when a Config rule fires a non-compliant finding?
The finding appears in the Config console, is forwarded to Security Hub, and triggers an SNS notification to the team. Automated remediation is possible via Config remediation actions (Lambda-backed) for common findings — automatically closing overly permissive security groups, enabling S3 encryption, etc. For POA&M, the finding enters the tracking workflow and must be remediated within the timeline defined by its severity level.
Is AWS Config expensive for GovCloud multi-account setups?
AWS Config charges per configuration item recorded — roughly $0.003 per item in GovCloud. A medium-complexity account with 500–1,000 resources generating 100,000 configuration items per month costs approximately $300/month. For the ConMon value delivered — automated compliance evidence for an ATO that costs thousands to maintain manually — this is highly favorable. Aggregate Config data to a central account to reduce per-account costs.
How do we handle false positives in Security Hub findings?
Security Hub findings can be suppressed or muted using workflow status. The process: review the finding, document the compensating control or accepted risk in the POA&M, then update the workflow status to "SUPPRESSED" with a note. Rutagon builds automation that cross-references POA&M entries with Security Hub findings — preventing the suppressed finding from reappearing in ConMon reports without documentation.
Discuss your project with Rutagon
Contact Us →