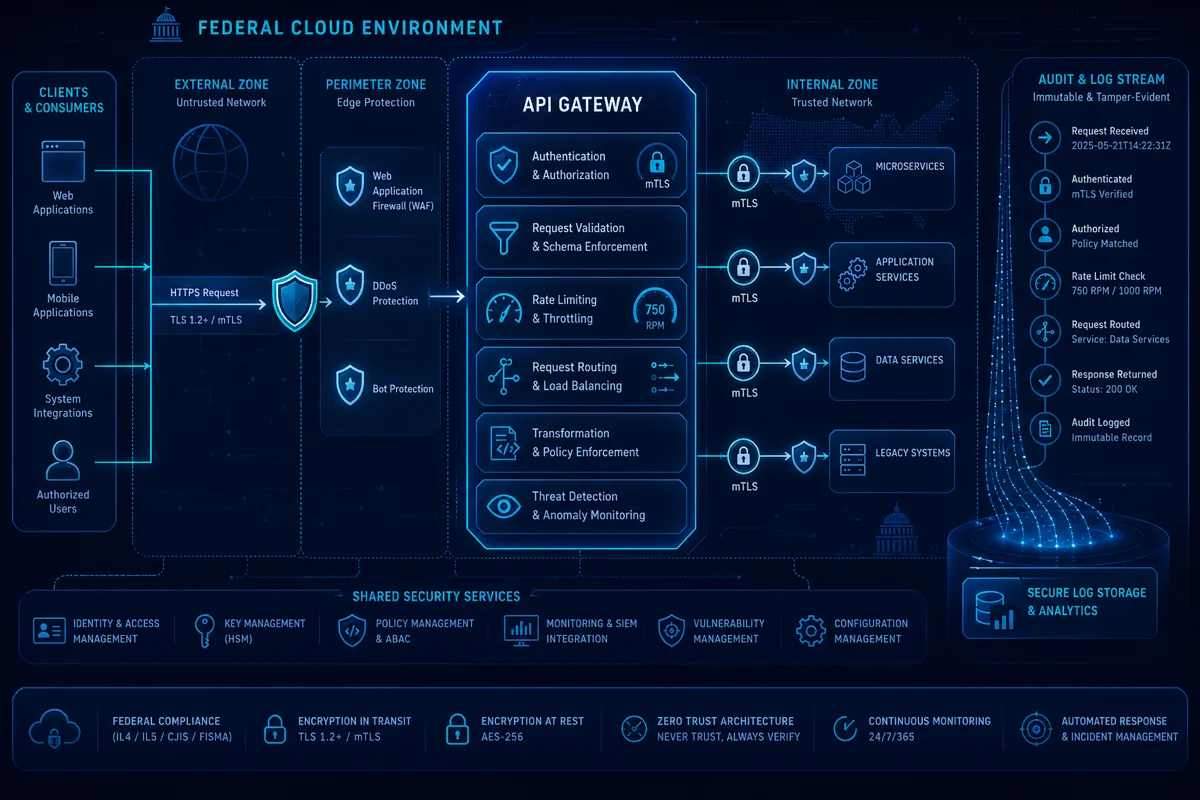
Every federal cloud system exposes APIs. Whether it's a microservices architecture exchanging internal data, a data platform serving analytics endpoints, or a mission system providing programmatic access to warfighters — the API gateway layer is where authentication, authorization, rate limiting, and audit logging converge.
Getting this layer wrong means failed ATO, production security findings, and mission risk. Getting it right means a composable, audit-ready API layer that satisfies NIST 800-53 controls and holds up under C3PAO assessment.
Why API Gateway Architecture Matters for Federal Programs
Federal APIs have requirements that commercial implementations often don't account for:
- FIPS 140-2 validated encryption — TLS 1.2 minimum, FIPS-validated cipher suites
- mTLS for service-to-service communication — client certificate verification, not just server-side TLS
- Continuous audit logging — every request/response must be logged to the program's ConMon infrastructure
- ITAR/CUI boundary enforcement — data classification labels must be honored at the API layer
- Zero trust alignment — no implicit trust based on network location
AWS API Gateway (REST, HTTP, and WebSocket APIs) is available in AWS GovCloud (US-West), making it the primary API gateway service for FedRAMP High and DoD IL2/IL4 workloads on AWS. For IL5 and C2S/SC2S environments, additional configurations apply.
Core AWS API Gateway Configuration for FedRAMP
Endpoint Type and Domain
# Terraform — API Gateway with custom domain and FIPS endpoint
resource "aws_api_gateway_rest_api" "federal_api" {
name = "${var.program_name}-api"
endpoint_configuration {
types = ["REGIONAL"] # Required for GovCloud FedRAMP — EDGE not FIPS-compliant
}
}
resource "aws_api_gateway_domain_name" "federal_domain" {
domain_name = "api.${var.program_domain}"
regional_certificate_arn = aws_acm_certificate.api_cert.arn
endpoint_configuration {
types = ["REGIONAL"]
}
security_policy = "TLS_1_2" # Enforce TLS 1.2 minimum
}Critical for FedRAMP: Use REGIONAL endpoints, not EDGE (CloudFront-backed). Edge endpoints route through CloudFront's global PoPs which are not FIPS-validated. Regional endpoints in GovCloud use FIPS 140-2 validated endpoints.
Authentication and Authorization
Federal APIs require strong authentication at every endpoint. Rutagon's standard patterns:
# Terraform — Cognito authorizer with GovCloud User Pool
resource "aws_api_gateway_authorizer" "cognito_auth" {
name = "cognito-authorizer"
rest_api_id = aws_api_gateway_rest_api.federal_api.id
type = "COGNITO_USER_POOLS"
provider_arns = [aws_cognito_user_pool.federal_idp.arn]
}
# Lambda authorizer for custom claims-based authorization
resource "aws_api_gateway_authorizer" "lambda_auth" {
name = "lambda-authorizer"
rest_api_id = aws_api_gateway_rest_api.federal_api.id
type = "TOKEN"
authorizer_uri = aws_lambda_function.authorizer.invoke_arn
authorizer_result_ttl_in_seconds = 0 # No caching for classified endpoints
}For DoD programs, PIV/CAC smart card authentication flows through an identity provider (Okta, Azure AD FIPS) before issuing short-lived tokens validated by the API Gateway authorizer.
mTLS for Service-to-Service APIs
Internal service-to-service APIs require mTLS — both sides present certificates:
resource "aws_api_gateway_domain_name" "service_domain" {
domain_name = "internal-api.${var.program_domain}"
regional_certificate_arn = aws_acm_certificate.service_cert.arn
mutual_tls_authentication {
truststore_uri = "s3://${aws_s3_bucket.truststore.bucket}/truststore.pem"
truststore_version = aws_s3_object.truststore.version_id
}
}The truststore contains the CA certificates for all services authorized to call this API. Services presenting certificates signed by an unauthorized CA are rejected at the TLS handshake — before authentication processing begins.
Rate Limiting and Throttling
Federal APIs serving multiple client types need usage plans and throttling to prevent any one client from degrading service for others — and to satisfy availability controls (NIST SA-17, SC-5):
resource "aws_api_gateway_usage_plan" "mission_critical" {
name = "mission-critical-tier"
api_stages {
api_id = aws_api_gateway_rest_api.federal_api.id
stage = aws_api_gateway_stage.prod.stage_name
}
throttle_settings {
burst_limit = 500 # Per-second burst
rate_limit = 1000 # Requests per second steady state
}
quota_settings {
limit = 100000 # Monthly quota
period = "MONTH"
}
}
resource "aws_api_gateway_usage_plan" "analytics_tier" {
name = "analytics-tier"
api_stages {
api_id = aws_api_gateway_rest_api.federal_api.id
stage = aws_api_gateway_stage.prod.stage_name
}
throttle_settings {
burst_limit = 100
rate_limit = 200
}
}Per-client API keys and usage plan associations mean that a runaway analytics job can't starve mission-critical API consumers.
Audit Logging to CloudWatch
Federal programs require every API call to be logged with sufficient detail for audit reconstruction (NIST AU-2, AU-3, AU-12):
resource "aws_api_gateway_stage" "prod" {
rest_api_id = aws_api_gateway_rest_api.federal_api.id
stage_name = "prod"
access_log_settings {
destination_arn = aws_cloudwatch_log_group.api_access.arn
format = jsonencode({
requestId = "$context.requestId"
sourceIp = "$context.identity.sourceIp"
requestTime = "$context.requestTime"
protocol = "$context.protocol"
httpMethod = "$context.httpMethod"
resourcePath = "$context.resourcePath"
routeKey = "$context.routeKey"
status = "$context.status"
responseLength = "$context.responseLength"
integrationError = "$context.integrationErrorMessage"
user = "$context.authorizer.principalId"
})
}
xray_tracing_enabled = true
}Logs are shipped to the program's SIEM through CloudWatch Logs subscription filters — providing the centralized audit trail required by ConMon procedures.
WAF Integration for IL4/IL5
At IL4 and above, AWS WAF is attached to the API Gateway to provide managed rule sets aligned with OWASP Top 10 and NIST control requirements:
resource "aws_wafv2_web_acl" "federal_api_waf" {
name = "${var.program_name}-api-waf"
scope = "REGIONAL"
default_action {
allow {}
}
rule {
name = "AWSManagedRulesCommonRuleSet"
priority = 1
override_action { none {} }
statement {
managed_rule_group_statement {
name = "AWSManagedRulesCommonRuleSet"
vendor_name = "AWS"
}
}
visibility_config {
cloudwatch_metrics_enabled = true
metric_name = "CommonRuleSet"
sampled_requests_enabled = true
}
}
}WAF block/allow decisions are logged separately and fed into the ConMon dashboard — satisfying SI-3 (Malicious Code Protection) and SC-7 boundary protection requirements.
NIST Control Coverage Summary
| Control Family | Implementation | |---|---| | AC-2/AC-3 | Cognito/Lambda authorizer + usage plan key enforcement | | AU-2/AU-3/AU-12 | CloudWatch access logs with full context fields | | SC-5 | Rate limiting + WAF managed rules | | SC-7 | WAF + mTLS boundary enforcement | | SC-28 | FIPS 140-2 TLS on regional endpoints | | SI-3 | WAF OWASP ruleset | | SA-17 | API Gateway design-level boundary enforcement |
For programs building API-intensive architectures, Rutagon delivers this full stack as part of an integrated cloud infrastructure engagement — configuration, IaC modules, ConMon integration, and ATO evidence collection.
Discuss API gateway architecture requirements →
Frequently Asked Questions
Should government programs use REST or HTTP APIs in AWS API Gateway?
For new government API implementations, HTTP APIs (not REST APIs) are preferred — they offer lower latency, lower cost, and native JWT authorizer support. REST APIs are required when you need features like API keys/usage plans, request/response transformation, or WAF integration directly at the API layer. For most mission system APIs, HTTP APIs with Lambda authorizers or Cognito authentication provide the right capability at lower operational cost.
What is the FIPS 140-2 compliance status of AWS API Gateway in GovCloud?
AWS API Gateway in GovCloud (US-West) uses FIPS 140-2 validated endpoints when accessed through the FIPS endpoint URL (apigateway.us-gov-west-1.amazonaws.com). Custom domain configurations with regional endpoints also route through FIPS-validated infrastructure. EDGE endpoint types use CloudFront PoPs that are not FIPS-validated and should not be used for FedRAMP High or IL4+ workloads.
How does mTLS differ from standard TLS for API gateways?
Standard TLS authenticates only the server (the API gateway proves its identity to the client). mTLS (mutual TLS) requires both sides to present and validate certificates — the client must prove its identity using a certificate signed by a CA in the API gateway's truststore. This is critical for service-to-service APIs in federal architectures where network-location-based trust is insufficient.
Can API Gateway audit logs satisfy NIST AU-12 requirements?
API Gateway access logs, when configured with a complete JSON format and shipped to CloudWatch Logs (then to a long-term archive), satisfy AU-12 generation requirements. The log format must capture: request time, source IP, authenticated identity, resource path, HTTP method, response status, and request ID. CloudWatch Logs Insights can be used to query these logs for audit investigations, satisfying AU-6 (Audit Review, Analysis, and Reporting).
How are API gateways configured for IL5 classified programs?
IL5 programs on AWS C2S/SC2S have additional constraints: EDGE endpoints are unavailable, mTLS is mandatory, all logs must remain within the program boundary, and third-party WAF rules require approval. Rutagon's IL5 configurations use private REST APIs (within a VPC), service control policies limiting access to the program's AWS OU, and an internal API catalog rather than public documentation.