Rutagon as a Federal Cloud and DevSecOps Subcontractor
Prime contractors looking for a cloud engineering and DevSecOps subcontractor for federal IT programs have a specific set of requirements: technical depth, compliance posture, administrative readiness, and delivery accountability. This page documents what Rutagon brings to each of those dimensions.
Company Data
| Field | Value |
|---|---|
| Legal name | Rutagon LLC |
| SAM.gov UEI | FB2FHEJHM493 |
| CAGE Code | 19ZR7 |
| SAM Status | Active (March 17, 2026) |
| Principal Office | 7879 W Sally Ct, Wasilla, AK 99623 |
| Primary NAICS | 541512 (Computer Systems Design) |
| Secondary NAICS | 541511, 541519, 518210 |
| Business Type | Small Business, LLC |
| HUBZone Status | Application pending (Q2 2026) — Wasilla, AK qualifies (Indian Land designation) |
| SPRS | Submitted (CMMC Level 1 self-assessment complete) |
| Website | rutagon.com |
| Government Page | rutagon.com/government |
Core Delivery Capabilities
Cloud Infrastructure (AWS Primary, Multi-Cloud IaC)
Rutagon's cloud infrastructure work is Terraform-first. Every environment — development, staging, production — is defined as code, version-controlled, and deployable from a clean state without manual configuration. This approach produces reproducible environments, comprehensive audit trails of infrastructure changes, and compliance-demonstrable deployment histories.
Primary AWS experience spans 25+ services across compute (Lambda, EC2, ECS, EKS), storage (S3, Aurora Serverless v2, DynamoDB), networking (CloudFront, WAF, Route 53, VPC), security (IAM, Secrets Manager, KMS, GuardDuty, Security Hub), and observability (CloudWatch, X-Ray, Athena). Infrastructure patterns are documented, portable, and adaptable across GovCloud and commercial AWS environments.
See: AWS GovCloud with Terraform: Compliant IaC
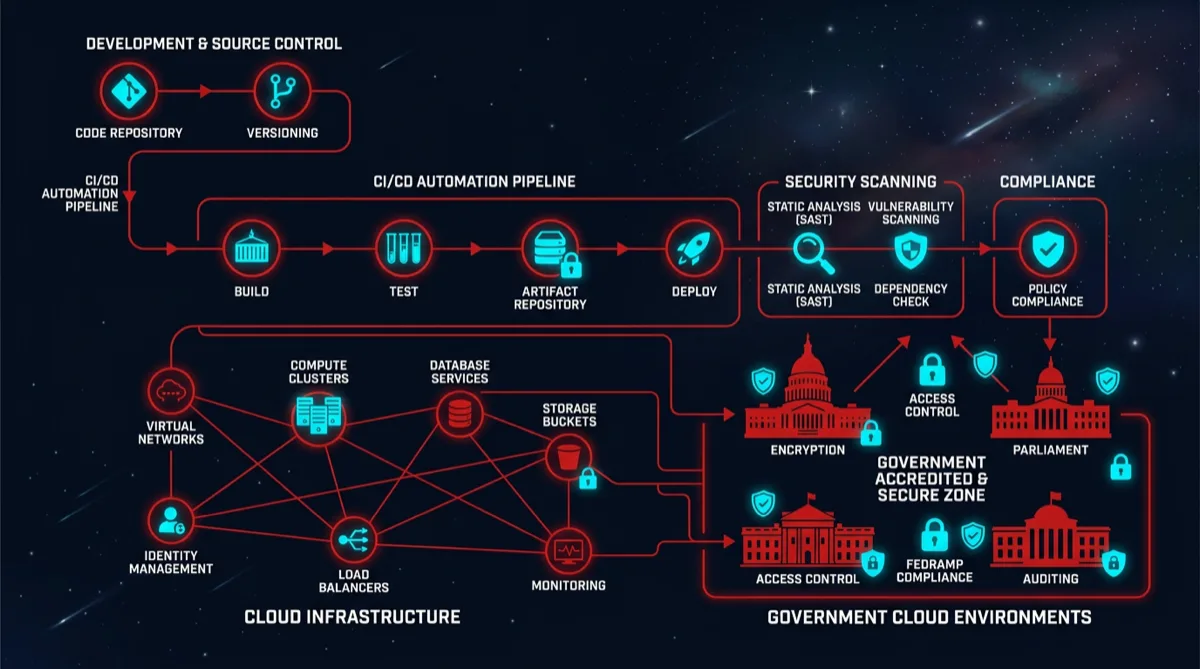
DevSecOps Pipeline Architecture
Rutagon builds CI/CD pipelines that integrate security as a gate, not a reporting step. The standard pipeline stack:
- Authentication: OIDC federation — zero long-lived AWS credentials in CI/CD. Short-lived session tokens, minimal IAM scope per pipeline stage.
- Container scanning: Trivy with CRITICAL/HIGH exit codes as hard pipeline gates. Scan results archived as artifacts for ATO evidence.
- SAST: Bandit (Python), ESLint security plugins (TypeScript/JS), Checkov (Terraform infrastructure). Results in pipeline artifacts.
- DAST: OWASP ZAP against staging environments before production promotion.
- Image signing: Cosign with AWS KMS-managed key pairs. SLSA Level 2 provenance attestation.
- Artifact management: GitLab Container Registry with image lifecycle policies, vulnerability report retention.
See: DevSecOps Subcontracting: What a Prime Gets
Government Compliance Architecture
Rutagon's compliance posture is maintained continuously, not assembled for assessments:
- CMMC Level 1: All 17 basic cyber hygiene practices implemented. Self-assessment complete, SPRS score submitted.
- DFARS 252.204-7012: CUI handling procedures documented, 72-hour incident reporting infrastructure configured and tested, NIST SP 800-171 control mapping maintained.
- NIST 800-171: 110-control mapping to AWS services documented, including access control (AC), audit logging (AU), identification and authentication (IA), and system/communications protection (SC) families.
- Continuous monitoring: Pipeline-generated evidence (scan artifacts, deployment manifests, signed image digests) provides the evidence stream for cATO frameworks.
See: CMMC Level 2 Cloud Infrastructure: Our Approach
Full-Stack Software Development
Beyond infrastructure, Rutagon delivers production application software. The production SaaS platform in Rutagon's portfolio — a native iOS and Android mobile application with 25+ AWS backend services — demonstrates full-stack delivery capability from UI to data layer:
- Frontend: React, TypeScript, Astro. Section 508 compliant by default.
- Mobile: Native Swift (iOS), native Kotlin (Android).
- Backend: Python Lambda functions, Node.js, PostgreSQL (Aurora Serverless v2), DynamoDB.
- APIs: RESTful and event-driven. API Gateway, Lambda, EventBridge, SQS.
For government programs requiring Section 508-compliant web applications, the accessibility architecture is built in — not retrofitted. See: Building 508-Compliant Government Websites.
Past Performance (Reference Projects)
Production SaaS Platform (Commercial): End-to-end design and delivery of a production-grade home services marketplace. Native iOS + Android + web application. 25+ AWS services, 24 Lambda functions, Aurora Serverless v2 database, OIDC-federated CI/CD pipeline with zero long-lived credentials. Deployed to production, serving active users.
Content Platform (Commercial): Multi-site content platform with server-side rendering, Terraform-managed AWS Amplify + CloudFront infrastructure, automated deployment pipeline. 30+ indexed pages across multiple domains.
Defense Technology Company Website (Commercial): Full-stack web development and hosting for a defense industry client. Compliance-aware architecture, GitLab-based CI/CD, WAF-protected CloudFront delivery.
Subcontracting Arrangement Terms
Rutagon accepts the following as standard flow-down provisions in subcontracts with federal primes:
- FAR standard clauses (Part 52 — applicable by contract type)
- DFARS cybersecurity and CUI requirements (252.204-7012 and related)
- CMMC Level 1 compliance requirements (self-assessed)
- SBA small business subcontracting reporting obligations (eSRS)
- Equal Opportunity and Affirmative Action clauses
- Intellectual Property — work made for hire on deliverables; Rutagon retains IP in pre-existing tools and frameworks
Billing is available as T&M (labor categories consistent with NAICS 541512 prevailing rates), cost-plus-fixed-fee, or firm-fixed-price for defined deliverables. Rutagon does not use subcontracting arrangements as staffing vehicles — engagements are structured around owned deliverables, not individual labor hours directed by the prime.
Starting a Teaming Discussion
Rutagon is open to teaming conversations for programs in:
- Federal cloud migration and modernization (civilian and defense)
- DoD DevSecOps software factory buildout
- Government web application development (Section 508)
- CMMC compliance architecture and implementation
- Data pipeline and analytics dashboards for federal customers
- Alaska-based or Arctic-environment programs
View the full capability statement at rutagon.com/government or reach out directly for teaming discussions, capability briefs, or proposal support.
Frequently Asked Questions
What is Rutagon's CAGE code and SAM.gov status?
Rutagon's CAGE code is 19ZR7, assigned by the Defense Logistics Agency in March 2026. The SAM.gov registration became active on March 17, 2026, with UEI FB2FHEJHM493. Primary NAICS is 541512 (Computer Systems Design). The registration renews annually through March 2027.
Is Rutagon a small business under FAR size standards?
Yes. For NAICS 541512, the SBA size standard is $34M in average annual receipts. Rutagon qualifies as a small business and can be counted toward a prime's SB subcontracting plan goals in eSRS reporting.
What CMMC level has Rutagon self-assessed?
Rutagon has completed a CMMC Level 1 self-assessment covering all 17 basic cyber hygiene practices. The SPRS score has been submitted. CMMC Level 2 third-party assessment is planned for 2027 when contracts requiring CUI handling are anticipated.
Does Rutagon have security clearances?
Rutagon currently operates at the unclassified and CUI level. Individual security clearance and a Facility Clearance (FCL) are being pursued through sub arrangements with cleared primes. Secret clearance sponsorship is a priority for Q4 2026, with the target of cleared operations beginning in 2027.
What types of federal programs is Rutagon focused on?
Rutagon targets programs in cloud engineering, DevSecOps, software modernization, government web development, and CMMC compliance architecture. Primary customers are DoD and federal civilian agencies. Geographic focus areas include Alaska installations (JBER, Eielson, Clear SFS) and programs where Alaska presence is an advantage. Secondary focus: national programs where cloud-native DevSecOps capability and lean delivery speed are differentiators.