DFARS clause 252.204-7012 is one of the most consequential cybersecurity requirements in defense contracting. It flows down to subcontractors, it has teeth — contract termination and False Claims Act exposure for knowing misrepresentation — and it requires specific technical infrastructure that many contractors haven't fully implemented.
Here's what DFARS 252.204-7012 requires in technical terms, and how Rutagon builds cloud infrastructure that satisfies it.
What DFARS 252.204-7012 Requires
The DFARS 252.204-7012 clause has three primary requirements:
1. Adequate Security for Covered Defense Information (CDI/CUI)
Contractors must provide "adequate security" for all covered defense information — defined as implementing the 110 security requirements in NIST SP 800-171 Rev 2. This is the same control set as CMMC Level 2, which is why DFARS compliance and CMMC preparation overlap significantly.
2. Rapid Reporting of Cyber Incidents (72-Hour Window)
This is the most operationally demanding requirement. If a contractor discovers a cyber incident affecting a system that processes CUI or covered defense information, they must:
- Report within 72 hours to DIBNet (the DoD's cyber incident reporting portal at dibnet.dod.mil)
- Preserve all images of known or compromised systems for at least 90 days after reporting
- Submit malware discovered during the incident to the DoD Cyber Crime Center (DC3)
- Cooperate with any subsequent damage assessment
The 72-hour clock starts from when the contractor "discovers" the incident — not when they confirm it. The definition of "discovery" matters.
3. Cloud Service Provider Requirements
If CUI is processed in the cloud, the cloud service provider (CSP) must also implement the NIST 800-171 security requirements and meet or exceed FedRAMP Moderate standards. This is why DFARS-covered workloads effectively require AWS GovCloud or an equivalent government-authorized cloud environment.
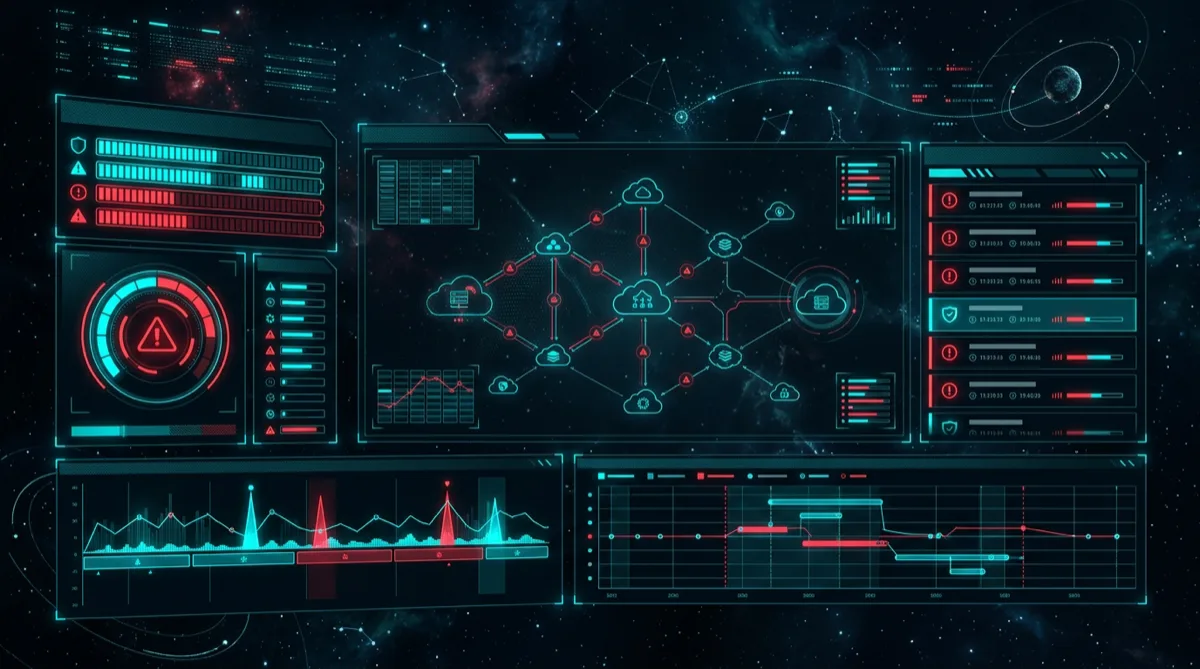
The Infrastructure Required for DFARS Compliance
CUI Identification and Boundary Definition
The first step is knowing what CUI you have and where it lives. The DFARS compliance posture depends entirely on the CUI boundary:
- Data classification tagging: All AWS resources processing CUI are tagged with classification labels
- Data flow documentation: Every path where CUI traverses the system is documented and monitored
- Boundary enforcement: CUI cannot flow outside the authorized boundary — enforced through network controls, data loss prevention, and access controls
# Tag all resources in the CUI boundary
resource "aws_s3_bucket" "cui_storage" {
bucket = "${var.environment}-cui-data"
tags = {
DataClassification = "CUI"
DFARSApplicable = "true"
ComplianceBaseline = "NIST-800-171"
}
}72-Hour Incident Response Infrastructure
Meeting the 72-hour reporting requirement requires pre-built incident response infrastructure. When an incident occurs is not the time to figure out how to capture system images or how to file a DIBNet report.
Detection infrastructure:
- AWS GuardDuty enabled across all accounts, with threat intelligence feeds
- AWS Security Hub aggregating and prioritizing findings
- CloudTrail with anomaly detection for unusual API activity
Notification and escalation:
- Automated notification from Security Hub to the Incident Response team for HIGH/CRITICAL findings
- Defined escalation path with 72-hour milestone tracking built into the IR playbook
- Pre-filled DIBNet incident report templates ready for rapid submission
# Lambda function: auto-notify IR team on critical GuardDuty finding
def notify_incident_response(event, context):
"""
Triggered by EventBridge rule on HIGH/CRITICAL GuardDuty findings.
Initiates 72-hour incident clock tracking.
"""
finding = event['detail']
severity = finding.get('severity', 0)
if severity >= 7.0: # HIGH or CRITICAL
# Send immediate notification
sns_client.publish(
TopicArn=os.environ['IR_TEAM_SNS_TOPIC'],
Subject=f"DFARS INCIDENT RESPONSE INITIATED - {finding['type']}",
Message=json.dumps({
'finding_id': finding['id'],
'type': finding['type'],
'severity': severity,
'affected_resources': finding.get('resources', []),
'incident_clock_start': datetime.utcnow().isoformat(),
'dibnet_deadline': (datetime.utcnow() + timedelta(hours=72)).isoformat(),
'action_required': 'ASSESS AND REPORT TO DIBNet WITHIN 72 HOURS IF CDI/CUI AFFECTED'
})
)Forensic preservation:
- Automated EBS snapshot on incident declaration
- CloudTrail and VPC Flow Log archives preserved for 90+ days beyond incident date
- System image preservation procedure documented and tested in advance
NIST 800-171 Implementation (All 110 Requirements)
DFARS compliance requires the same 110 NIST 800-171 requirements as CMMC Level 2. The cloud architecture implementation covers all 14 requirement families. Key technical implementations:
3.1 Access Control (22 requirements):
- IAM Identity Center with MFA enforcement
- No IAM users in production accounts
- Least-privilege role assignments with periodic review
3.3 Audit and Accountability (9 requirements):
- CloudTrail organization trail with log file validation
- 3-year log retention with 90-day hot retention
- Tamper-evident log archive in isolated audit account
3.4 Configuration Management (9 requirements):
- Terraform IaC as authoritative baseline
- AWS Config rules for continuous compliance validation
- Automated drift detection and alerting
3.13 System and Communications Protection (16 requirements):
- All data in transit: TLS 1.2 minimum
- All data at rest: AES-256 with customer-managed KMS keys
- Network segmentation enforced via security groups
- Encryption of all CUI in transit and at rest
SPRS Score Documentation
DFARS requires contractors to submit their NIST 800-171 self-assessment score to the Supplier Performance Risk System (SPRS). The SPRS score is calculated by subtracting point values for each failed requirement from a perfect score of 110.
Cloud-native systems with comprehensive IaC implementations can often achieve scores in the 90–110 range, depending on the physical controls (which cloud systems partially inherit from the CSP) and administrative controls (policies and procedures).
The SPRS score must reflect the actual implemented posture — not the desired posture. CISA's guidance and DoJ False Claims Act actions against contractors with inflated SPRS scores make honest assessment critical.
See our related work on SPRS and cloud security architecture and NIST 800-171 cloud implementation.
View Rutagon's government capabilities →
Frequently Asked Questions
What does DFARS 252.204-7012 require defense contractors to do?
DFARS 252.204-7012 requires contractors (and subcontractors) to: (1) implement "adequate security" for covered defense information by satisfying all 110 NIST SP 800-171 Rev 2 requirements, (2) report cyber incidents affecting CDI/CUI to DIBNet within 72 hours of discovery, (3) preserve system images and relevant data for at least 90 days after reporting, (4) submit malware to DC3, and (5) use only cloud service providers that meet or exceed FedRAMP Moderate standards for CUI workloads.
What is the 72-hour cyber incident reporting requirement?
Under DFARS 252.204-7012, contractors must report cyber incidents affecting systems that process covered defense information within 72 hours of discovering the incident. "Discovery" is when the contractor reasonably concludes an incident has occurred — not when it's confirmed. Reports go to DIBNet (dibnet.dod.mil). Late reporting or failure to report is a contract compliance violation that can trigger remedies up to contract termination.
Does DFARS 252.204-7012 flow down to subcontractors?
Yes. Contractors are required to include the DFARS 252.204-7012 clause in all subcontracts involving covered defense information. This means if you're a prime receiving CUI from DoD, every subcontractor who touches that CUI also bears the same 110 NIST 800-171 requirements and 72-hour reporting obligations. Prime contractors should verify subcontractor compliance as part of their vendor risk management.
What cloud service providers are acceptable under DFARS 252.204-7012?
DFARS 252.204-7012 requires CSPs to meet or exceed FedRAMP Moderate security requirements. AWS GovCloud (US) has FedRAMP High authorization, which exceeds this requirement and is the standard choice for DFARS-covered workloads. Microsoft Azure Government (DoD regions) is also used. Commercial cloud regions (AWS commercial, Azure non-government) are generally not acceptable for CUI processing under DFARS without significant additional security controls documentation.
What is the SPRS score and how does it relate to DFARS?
The Supplier Performance Risk System (SPRS) score reflects a contractor's self-assessed compliance with NIST SP 800-171. Contractors subject to DFARS 252.204-7012 are required to submit their current NIST 800-171 assessment score to SPRS. The score starts at 110 (perfect) and points are deducted for each failed requirement. DoJ has pursued False Claims Act cases against contractors who submitted inflated SPRS scores, making honest self-assessment legally important.